On March 8, 2024, KrebsOnSecurity published a deep dive on the consumer data broker Radaris, showing how the original owners are two men in Massachusetts who operated multiple Russian language dating services and affiliate programs, in addition to a dizzying array of people-search websites. The subjects of that piece are threatening to sue KrebsOnSecurity for defamation unless the story is retracted. Meanwhile, their attorney has admitted that the person Radaris named as the CEO from its inception is a fabricated identity.
Radaris is just one cog in a sprawling network of people-search properties online that sell highly detailed background reports on U.S. consumers and businesses. Those reports typically include the subject’s current and previous addresses, partial Social Security numbers, any known licenses, email addresses and phone numbers, as well as the same information for any of their immediate relatives.
Radaris has a less-than-stellar reputation when it comes to responding to consumers seeking to have their reports removed from its various people-search services. That poor reputation, combined with indications that the true founders of Radaris have gone to extraordinary lengths to conceal their stewardship of the company, was what prompted KrebsOnSecurity to investigate the origins of Radaris in the first place.
On April 18, KrebsOnSecurity received a certified letter (PDF) from Valentin “Val” Gurvits, an attorney with the Boston Law Group, stating that KrebsOnSecurity would face a withering defamation lawsuit unless the Radaris story was immediately retracted and an apology issued to the two brothers named in the story as co-founders.
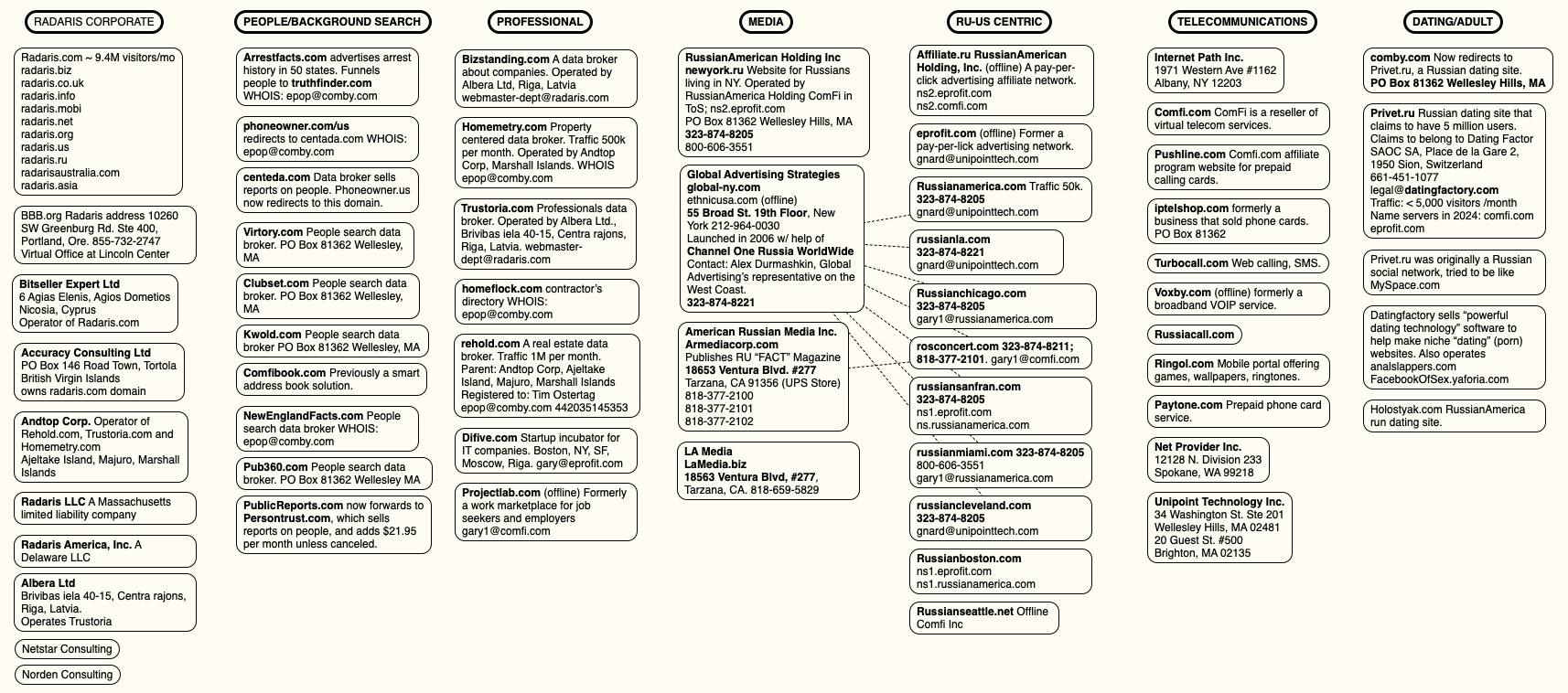
That March story worked backwards from the email address used to register radaris.com, and charted an impressive array of data broker companies created over the past 15 years by Massachusetts residents Dmitry and Igor Lubarsky (also sometimes spelled Lybarsky or Lubarski). Dmitry goes by “Dan,” and Igor uses the name “Gary.”
Those businesses included numerous websites marketed to Russian-speaking people who are new to the United States, such as russianamerica.com, newyork.ru, russiancleveland.com, russianla.com, russianmiami.com, etc. Other domains connected to the Lubarskys included Russian-language dating and adult websites, as well as affiliate programs for their international calling card businesses.
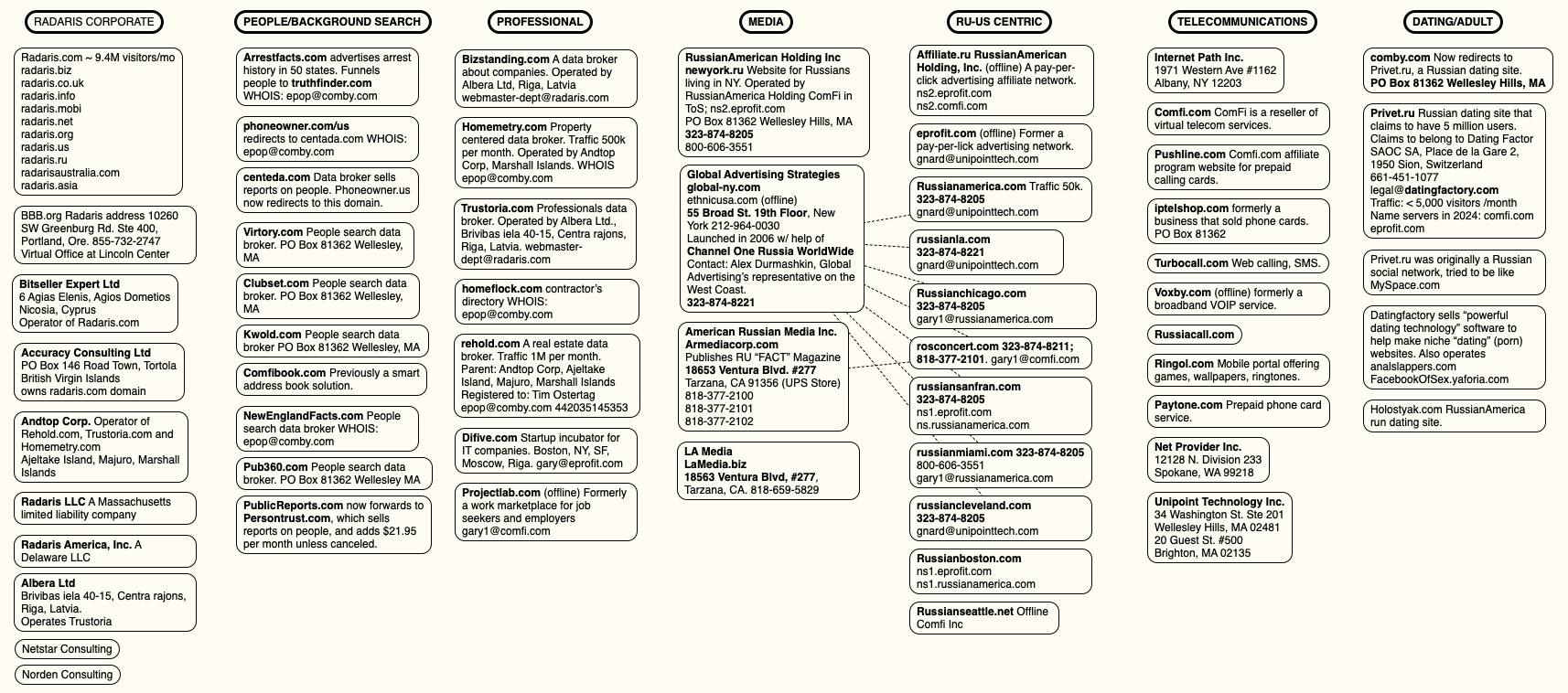
A mind map of various entities apparently tied to Radaris and the company’s co-founders. Click to enlarge.
The story on Radaris noted that the Lubarsky brothers registered most of their businesses using a made-up name — “Gary Norden,” sometimes called Gary Nord or Gary Nard.
Mr. Gurvits’ letter stated emphatically that my reporting was lazy, mean-spirited, and obviously intended to smear the reputation of his clients. By way of example, Mr. Gurvits said the Lubarskys were actually Ukrainian, and that the story painted his clients in a negative light by insinuating that they were somehow associated with Radaris and with vaguely nefarious elements in Russia.
But more to the point, Mr. Gurvits said, neither of his clients were Gary Norden, and neither had ever held any leadership positions at Radaris, nor were they financial beneficiaries of the company in any way.
“Neither of my clients is a founder of Radaris, and neither of my clients is the CEOs of Radaris,” Gurvits wrote. “Additionally, presently and going back at least the past 10 years, neither of my clients are (or were) officers or employees of Radaris. Indeed, neither of them even owns (or ever owned) any equity in Radaris. In intentional disregard of these facts, the Article implies that my clients are personally responsible for Radaris’ actions. Therefore, you intentionally caused all negative allegations in the Article made with respect to Radaris to be imputed against my clients personally.”
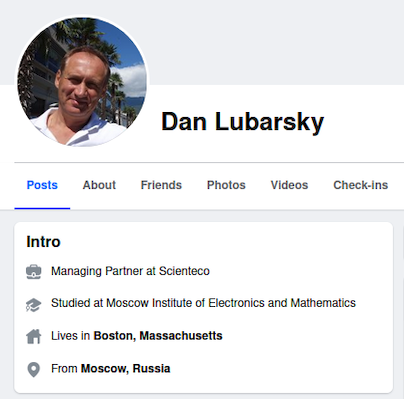
Dan Lubarsky’s Facebook page, just prior to the March 8 story about Radaris, said he was from Moscow.
We took Mr. Gurvits’ word on the ethnicity of his clients, and adjusted the story to remove a single mention that they were Russian. We did so even though Dan Lubarsky’s own Facebook page said (until recently) that he was from Moscow, Russia.
KrebsOnSecurity asked Mr. Gurvits to explain precisely which other details in the story were incorrect, and replied that we would be happy to update the story with a correction if they could demonstrate any errors of fact or omission.
We also requested specifics about several aspects of the story, such as the identity of the current Radaris CEO — listed on the Radaris website as “Victor K.” Mr. Gurvits replied that Radaris is and always has been based in Ukraine, and that the company’s true founder “Eugene L” is based there.
While Radaris has claimed to have offices in Massachusetts, Cyprus and Latvia, its website has never mentioned Ukraine. Mr. Gurvits has not responded to requests for more information about the identities of “Eugene L” or “Victor K.”
Gurvits said he had no intention of doing anyone’s reporting for them, and that the Lubarskys were going to sue KrebsOnSecurity for defamation unless the story was retracted in full. KrebsOnSecurity replied that journalists often face challenges to things that they report, but it is more than rare for one who makes a challenge to take umbrage at being asked for supporting information.
On June 13, Mr. Gurvits sent another letter (PDF) that continued to claim KrebsOnSecurity was defaming his clients, only this time Gurvits said his clients would be satisfied if KrebsOnSecurity just removed their names from the story.
“Ultimately, my clients don’t care what you say about any of the websites or corporate entities in your Article, as long as you completely remove my clients’ names from the Article and cooperate with my clients to have copies of the Article where my clients’ names appear removed from the Internet,” Mr. Gurvits wrote.
MEET THE FAKE RADARIS CEO
The June 13 letter explained that the name Gary Norden was a pseudonym invented by the Radaris marketing division, but that neither of the Lubarsky brothers were Norden.
This was a startling admission, given that Radaris has quoted the fictitious Gary Norden in press releases published and paid for by Radaris, and in news media stories where the company is explicitly seeking money from investors. In other words, Radaris has been misrepresenting itself to investors from the beginning. Here’s a press release from Radaris that was published on PR Newswire in April 2011:

A press release published by Radaris in 2011 names the CEO of Radaris as Gary Norden, which was a fake name made up by Radaris’ marketing department.
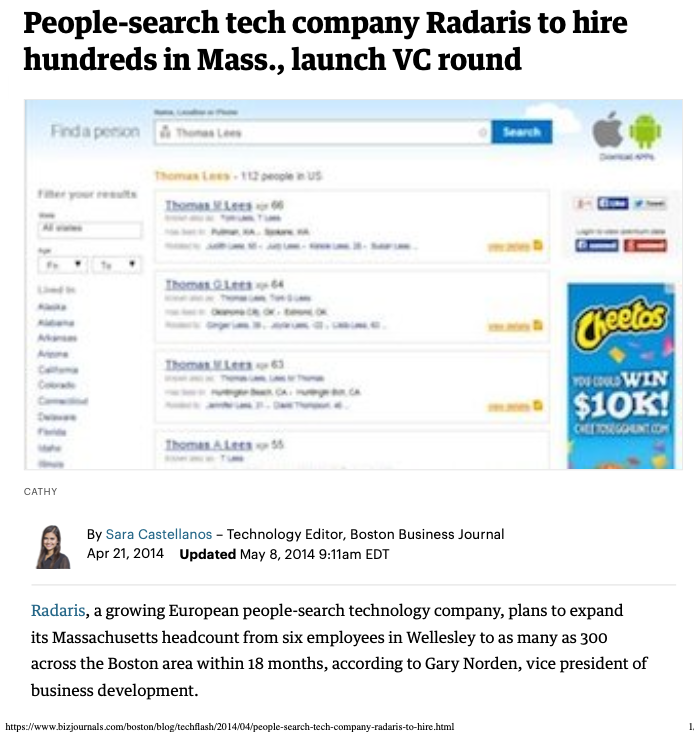
In April 2014, the Boston Business Journal published a story (PDF) about Radaris that extolled the company’s rapid growth and considerable customer base. The story noted that, “to date, the company has raised less than $1 million from Cyprus-based investment company Difive.”
“We live in a world where information becomes much more broad and much more available every single day,” the Boston Business Journal quoted Radaris’ fake CEO Gary Norden, who by then had somehow been demoted from CEO to vice president of business development.
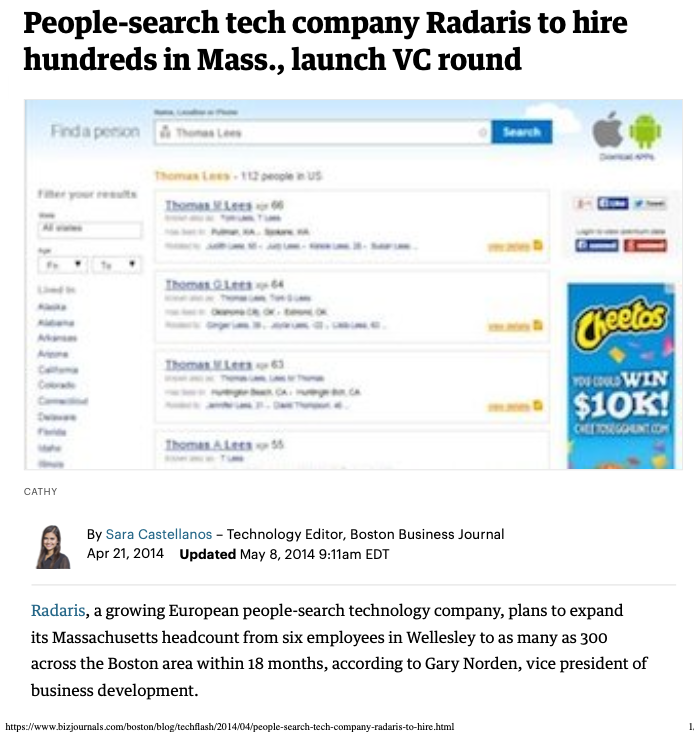
A Boston Business Journal story from April 2014 quotes the fictitious Radaris CEO Gary Norden.
“We decided there needs to be a service that allows for ease of monitoring of information about people,” the fake CEO said. The story went on to say Radaris was seeking to raise between $5 million and $7 million from investors in the ensuing months.
THE BIG LUBARSKY
In his most recent demand letter, Mr. Gurvits helpfully included resumes for both of the Lubarsky brothers.
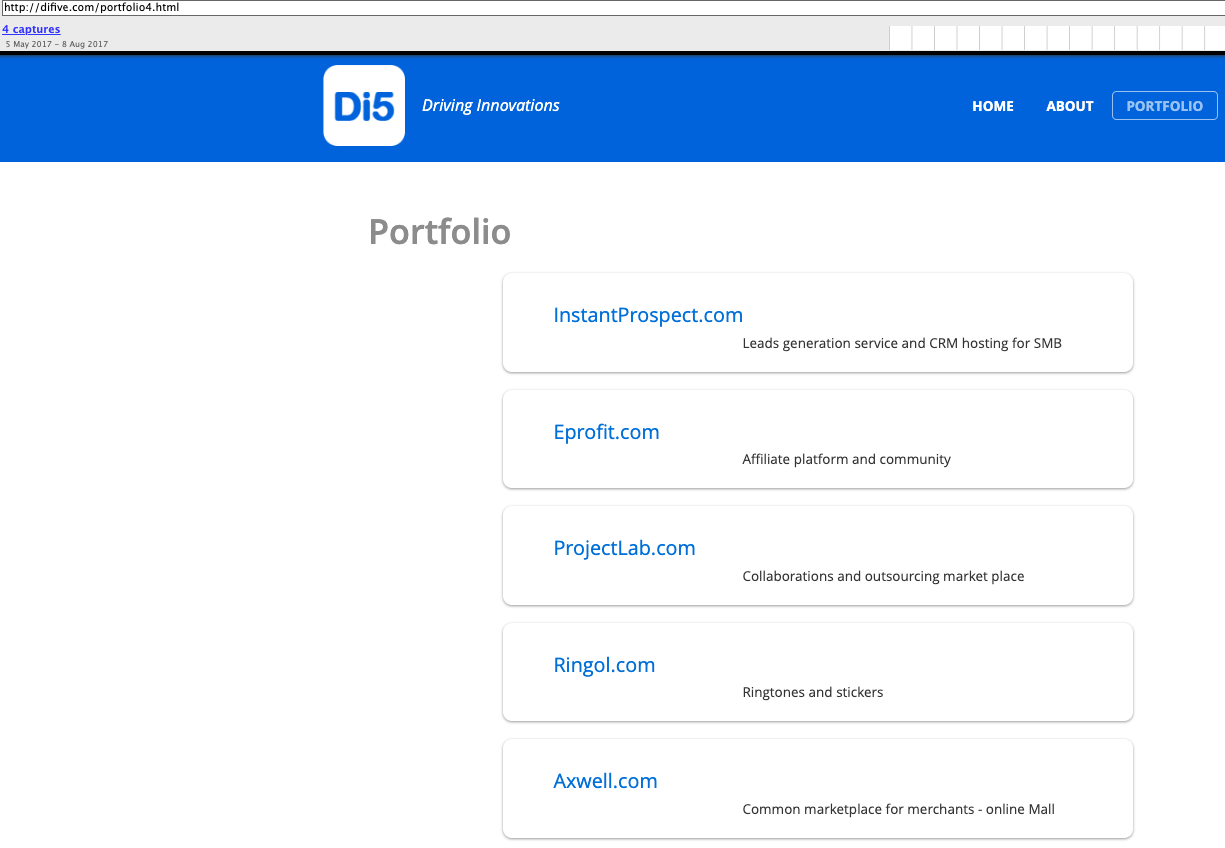
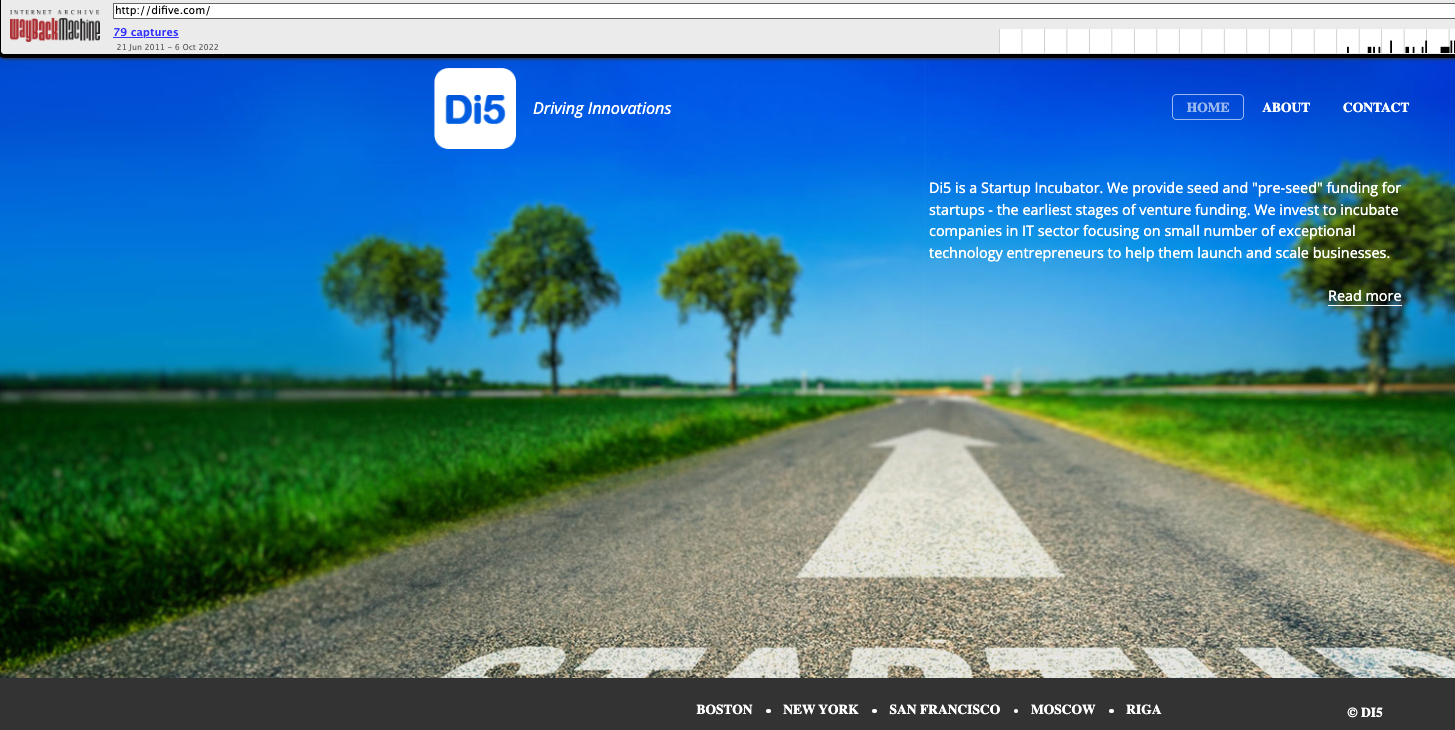
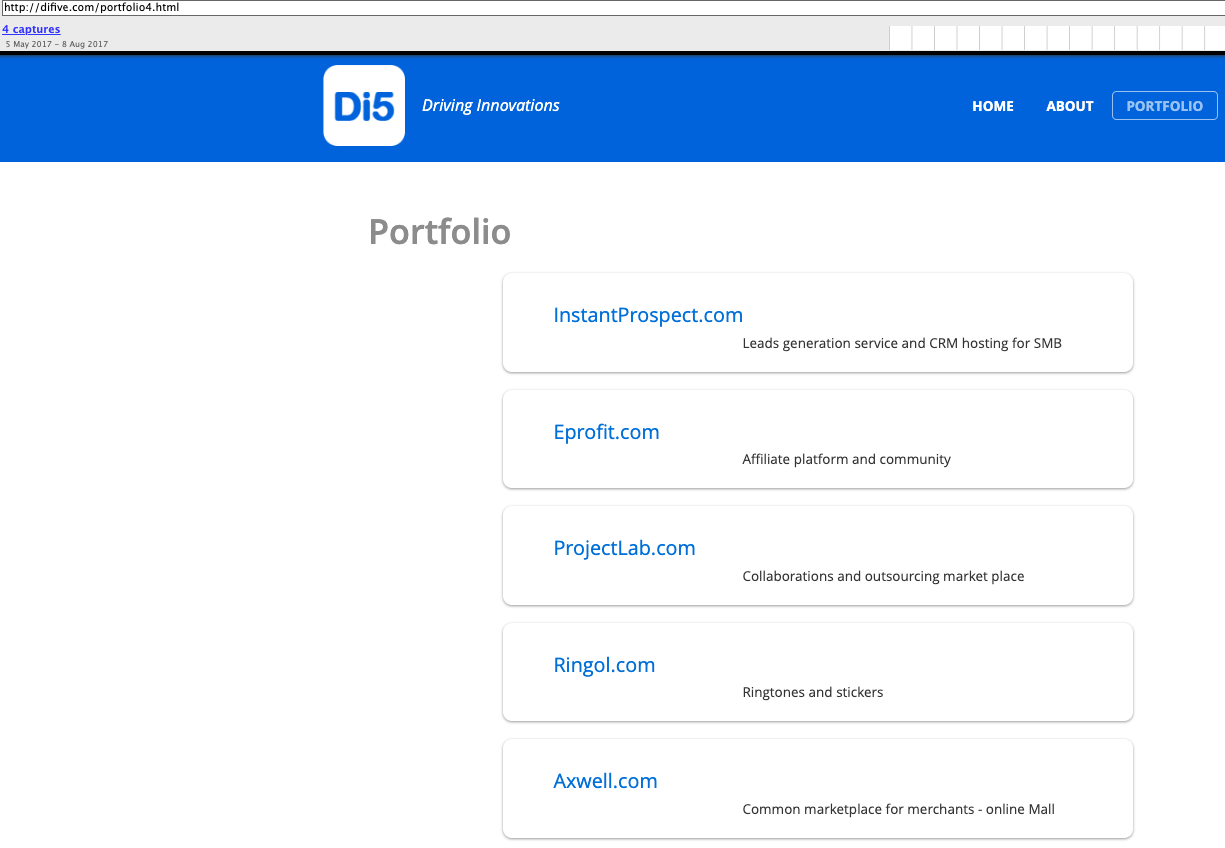
Dmitry Lubarsky’s resume states he is the owner of Difive.com, a startup incubator for IT companies. Recall that Difive is the same company mentioned by the fake Radaris CEO in the 2014 Boston Business Journal story, which said Difive was the company’s initial and sole investor.
Difive’s website in 2016 said it had offices in Boston, New York, San Francisco, Riga (Latvia) and Moscow (nothing in Ukraine). Meanwhile, DomainTools.com reports difive.com was originally registered in 2007 to the fictitious Gary Norden from Massachusetts.
Archived copies of the Difive website from 2017 include a “Portfolio” page indexing all of the companies in which Difive has invested. That list, available here, includes virtually every “Gary Norden” domain name mentioned in my original report, plus a few that escaped notice earlier.
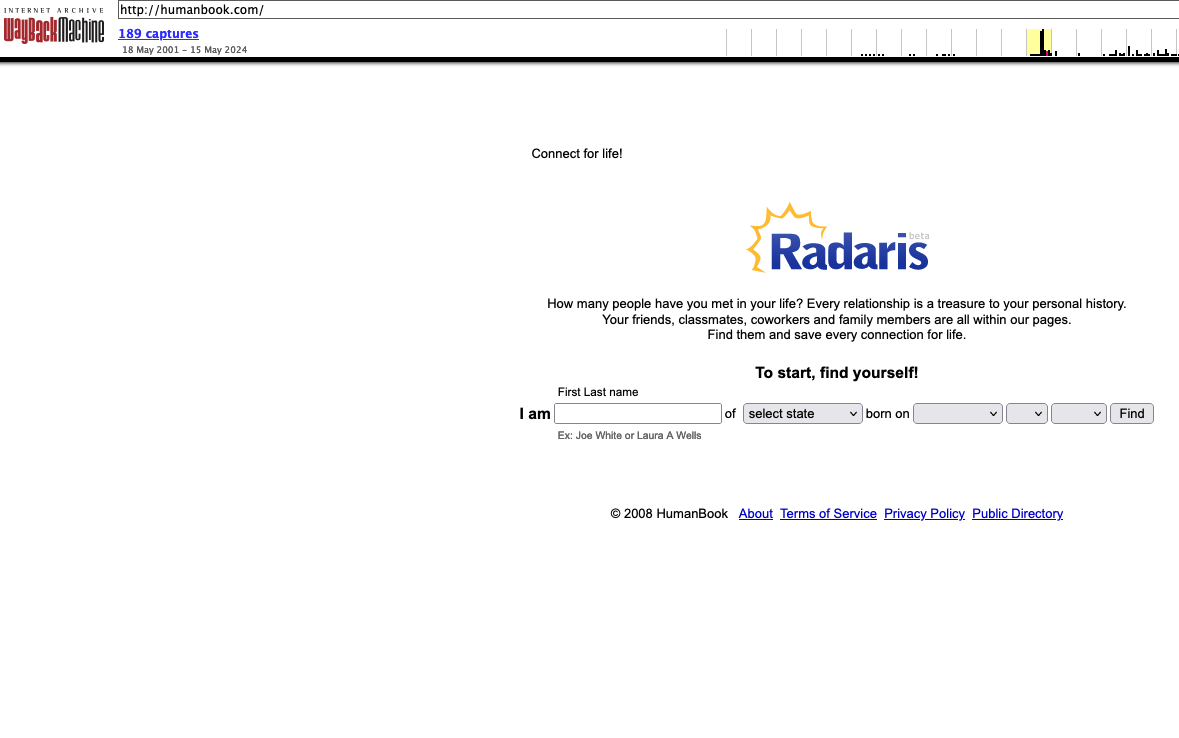
Dan Lubarsky’s resume says he was CEO of a people search company called HumanBook. The Wayback machine at archive.org shows the Humanbook domain (humanbook.com) came online around April 2008, when the company was still in “beta” mode.
By August 2008, however, humanbook.com had changed the name advertised on its homepage to Radaris Beta. Eventually, Humanbook simply redirected to radaris.com.
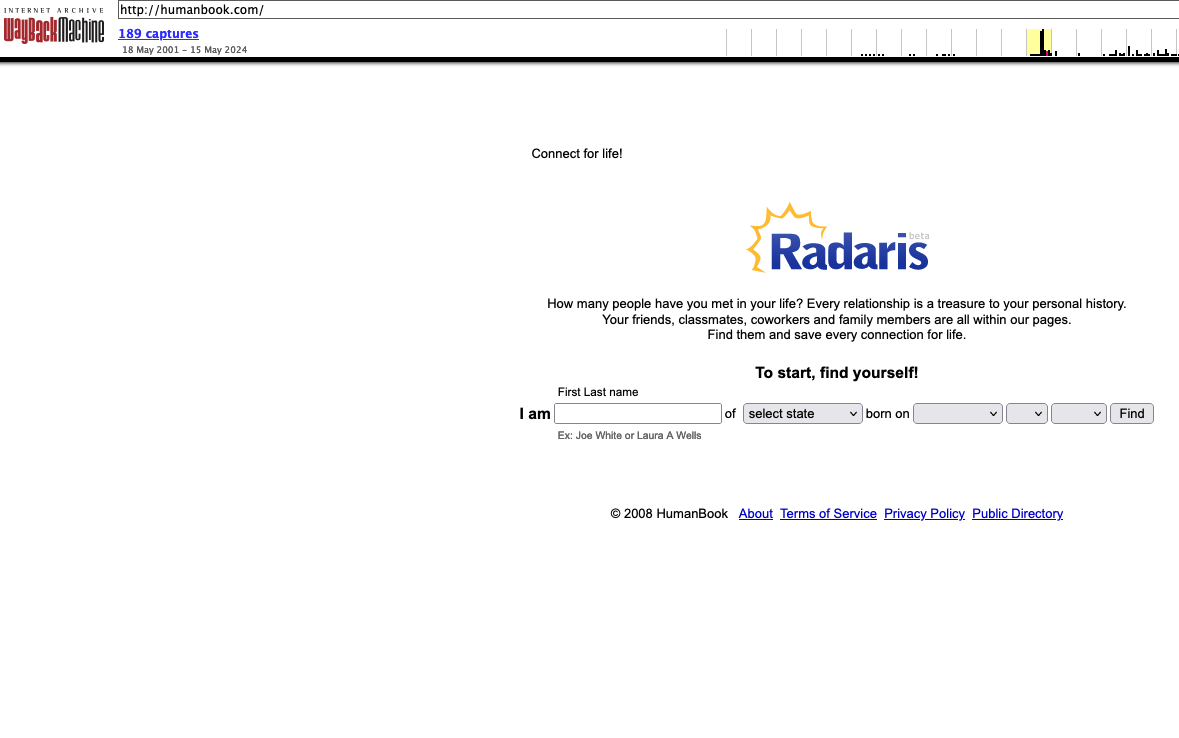
Archive.org’s record of humanbook.com from 2008, just after its homepage changed to Radaris Beta.
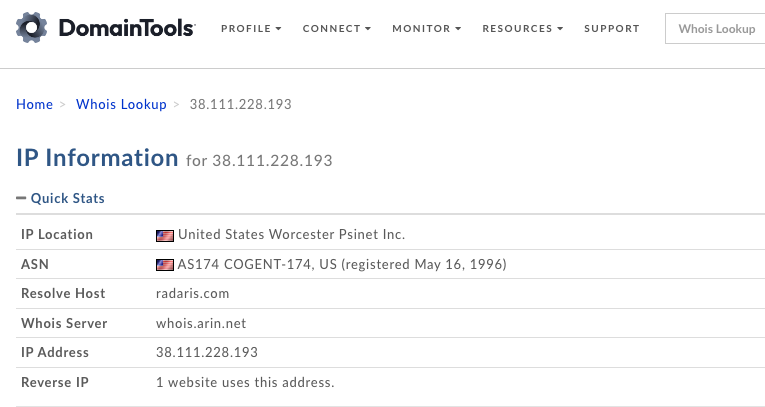
Astute readers may notice that the domain radaris.com is not among the companies listed as Difive investments. However, passive domain name system (DNS) records from DomainTools show that between October 2023 and March 2024 radaris.com was hosted alongside all of the other Gary Norden domains at the Internet address range 38.111.228.x.
That address range simultaneously hosted every domain mentioned in this story and in the original March 2024 report as connected to email addresses used by Gary Norden, including radaris.com, radaris.ru, radaris.de, difive.com, privet.ru, blog.ru, comfi.com, phoneowner.com, russianamerica.com, eprofit.com, rehold.com, homeflock.com, humanbook.com and dozens more. A spreadsheet of those historical DNS entries for radaris.com is available here (.csv).
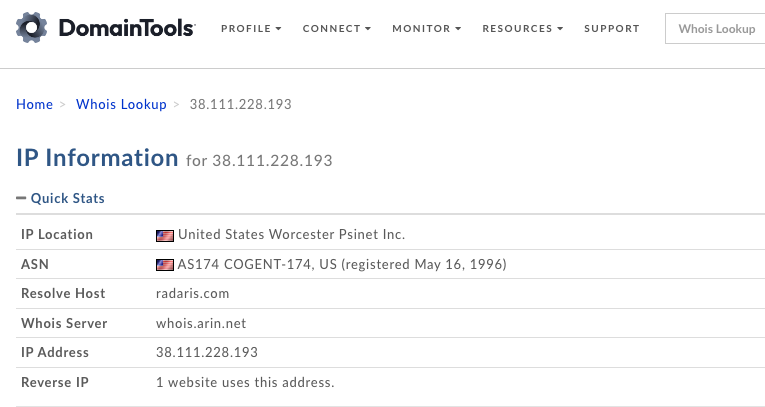
Image: DomainTools.com
The breach tracking service Constella Intelligence finds just two email addresses ending in difive.com have been exposed in data breaches over the years: dan@difive.com, and gn@difive.com. Presumably, “gn” stands for Gary Norden.
A search on the email address gn@difive.com via the breach tracking service osint.industries reveals this address was used to create an account at Airbnb under the name Gary, with the last four digits of the account’s phone number ending in “0001.”
Constella Intelligence finds gn@difive.com was associated with the Massachusetts number 617-794-0001, which was used to register accounts for “Igor Lybarsky” from Wellesley or Sherborn, Ma. at multiple online businesses, including audiusa.com and the designer eyewear store luxottica.com.
The phone number 617-794-0001 also appears for a “Gary Nard” user at russianamerica.com. Igor Lubarsky’s resume says he was the manager of russianamerica.com.
DomainTools finds 617-794-0001 is connected to registration records for three domains, including paytone.com, a domain that Dan Lubarsky’s resume says he managed. DomainTools also found that number on the registration records for trustoria.com, another major consumer data broker that has an atrocious reputation, according to the Better Business Bureau.
Dan Lubarsky’s resume says he was responsible for several international telecommunications services, including the website comfi.com. DomainTools says the phone number connected to that domain — 617-952-4234 — was also used on the registration records for humanbook.net/biz/info/mobi/us, as well as for radaris.me, radaris.in, and radaris.tel.
Two other key domains are connected to that phone number. The first is barsky.com, which is the website for Barsky Estate Realty Trust (PDF), a real estate holding company controlled by the Lubarskys. Naturally, DomainTools finds barsky.com also was registered to a Gary Norden from Massachusetts. But the organization listed in the barsky.com registration records is Comfi Inc., a VOIP communications firm that Dan Lubarsky’s resume says he managed.
The other domain of note is unipointtechnologies.com. Dan Lubarsky’s resume says he was the CEO of Wellesley Hills, Mass-based Unipoint Technology Inc. In 2012, Unipoint was fined $179,000 by the U.S. Federal Communications Commission, which said the company had failed to apply for a license to provide international telecommunications services.
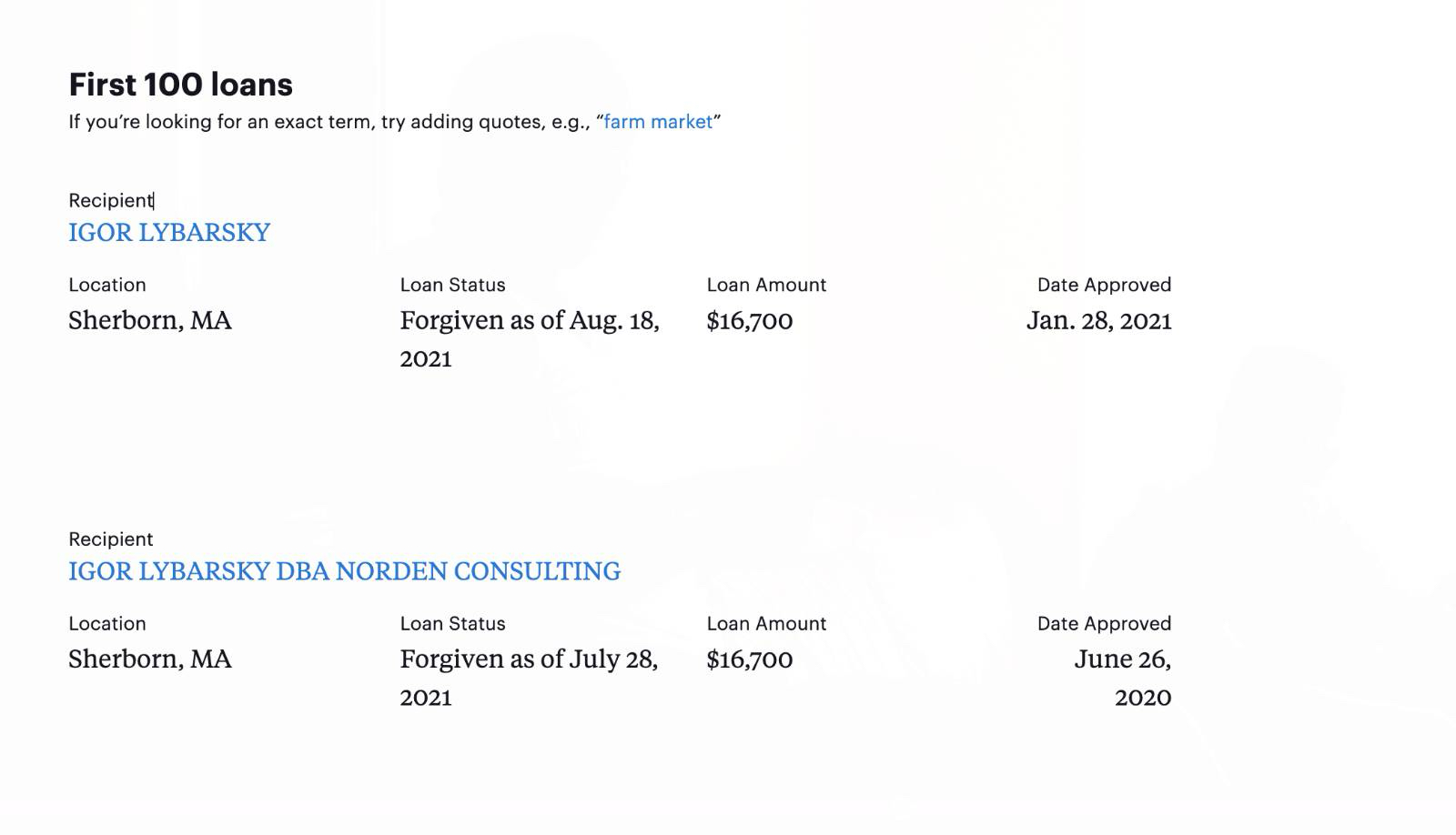
A pandemic assistance loan granted in 2020 to Igor Lybarsky of Sherborn, Ma. shows he received the money to an entity called Norden Consulting.
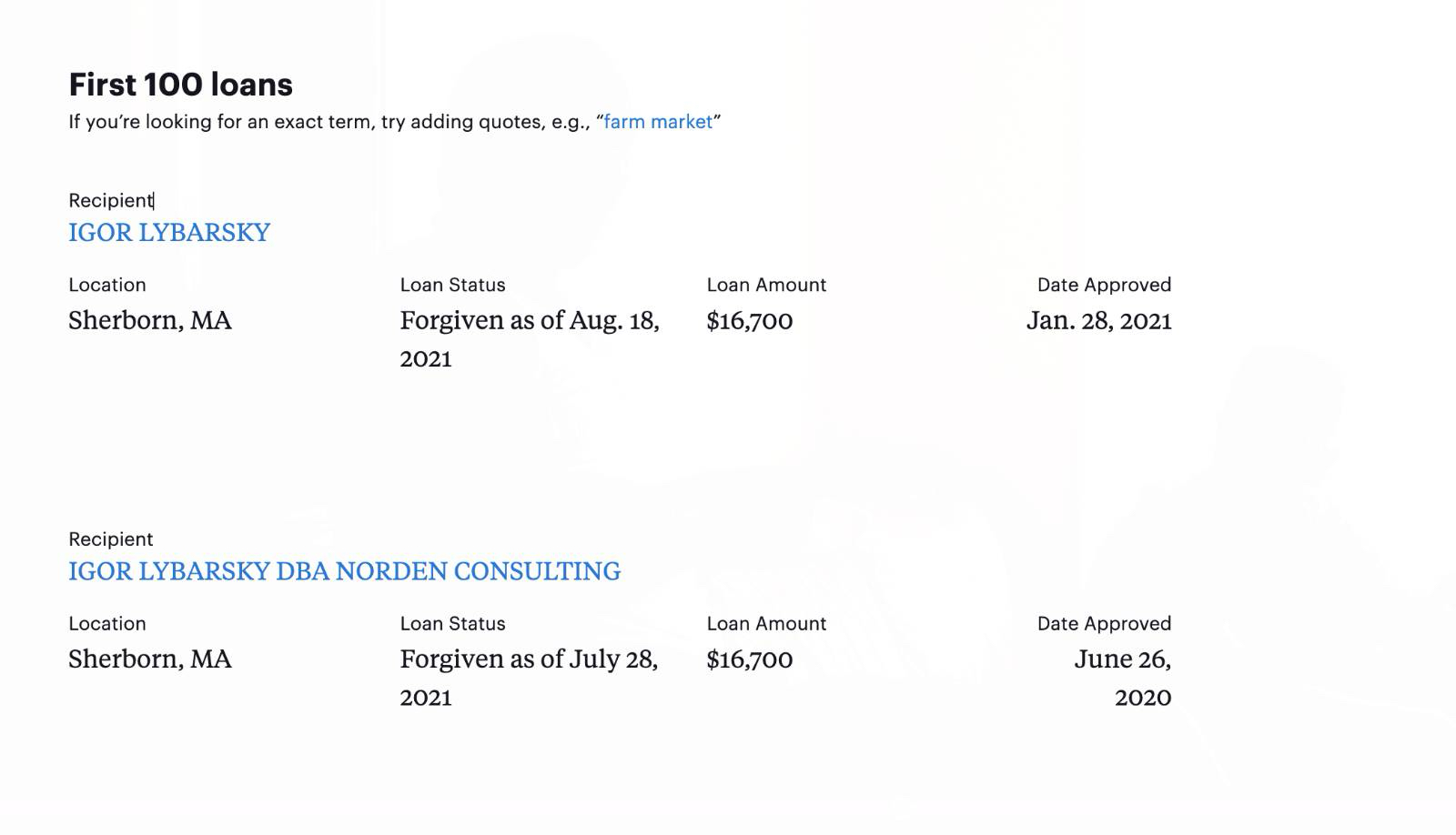
Notice the name on the recipient of this government loan for Igor Lybarsky from Sherborn, Ma: Norden Consulting.
PATENTLY REMARKABLE
The 2011 Radaris press release quoting their fake CEO Gary Norden said the company had four patents pending from a team of computer science PhDs. According to the resume shared by Mr. Gurvits, Dan Lubarsky has a PhD in computer science.
The U.S. Patent and Trademark Office (PTO) says Dan Lubarsky/Lubarski has at least nine technology patents to his name. The fake CEO press release from Radaris mentioning its four patents was published in April 2011. By that time, the PTO says Dan Lubarsky had applied for exactly four patents, including, “System and Method for a Web-Based People Directory.” The first of those patents, published in 2009, is tied to Humanbook.com, the company Dan Lubarsky founded that later changed its name to Radaris.
If the Lubarskys were never involved in Radaris, how do they or their attorney know the inside information that Gary Norden is a fiction of Radaris’ marketing department? KrebsOnSecurity has learned that Mr. Gurvits is the same attorney responding on behalf of Radaris in a lawsuit against the data broker filed earlier this year by Atlas Data Privacy.
Mr. Gurvits also stepped forward as Radaris’ attorney in a class action lawsuit the company lost in 2017 because it never contested the claim in court. When the plaintiffs told the judge they couldn’t collect on the $7.5 million default judgment, the judge ordered the domain registry Verisign to transfer the radaris.com domain name to the plaintiffs.
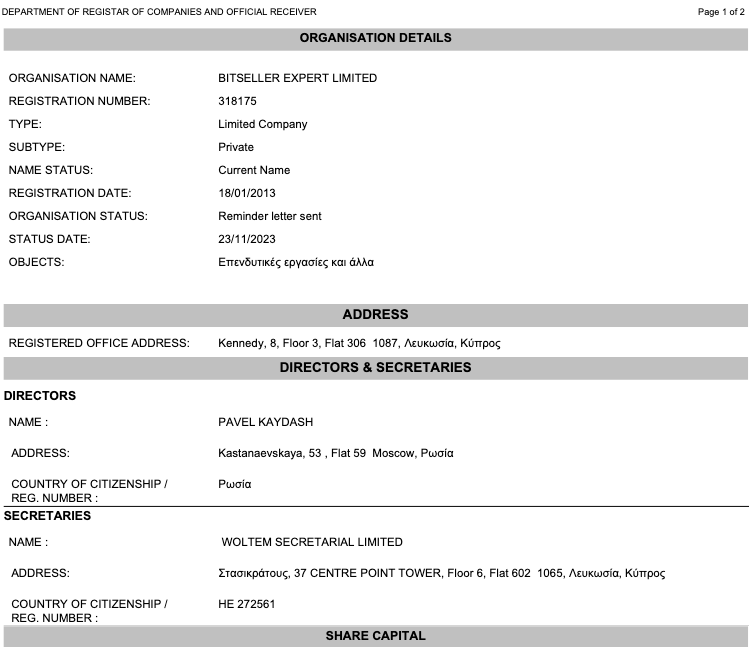
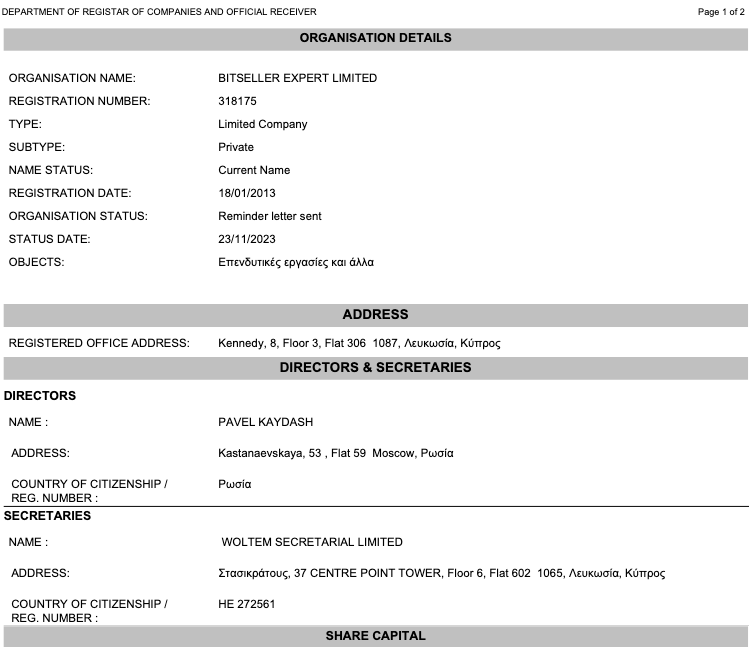
Mr. Gurvits appealed the verdict, arguing that the lawsuit hadn’t named the actual owners of the Radaris domain name — a Cyprus company called Bitseller Expert Limited — and thus taking the domain away would be a violation of their due process rights.
The judge ruled in Radaris’ favor — halting the domain transfer — and told the plaintiffs they could refile their complaint. Soon after, the operator of Radaris changed from Bitseller to Andtop Company, an entity formed (PDF) in the Marshall Islands in Oct. 2020. Andtop also operates the aforementioned people-search service Trustoria.
Mr. Gurvits’ most-publicized defamation case was a client named Aleksej Gubarev, a Russian technology executive whose name appeared in the Steele Dossier. That document included a collection of salacious, unverified information gathered by the former British intelligence officer Christopher Steele during the 2016 U.S. presidential campaign at the direction of former president Donald Trump’s political rivals.
Gubarev, the head of the IT services company XBT Holding and the Florida web hosting firm Webzilla, sued BuzzFeed for publishing the Steele dossier. One of the items in the dossier alleged that XBT/Webzilla and affiliated companies played a key role in the hack of Democratic Party computers in the spring of 2016. The memo alleged Gubarev had been coerced into providing services to Russia’s main domestic security agency, known as the FSB.
In December 2018, a federal judge in Miami ruled in favor of BuzzFeed, saying the publication was protected by the fair report privilege, which gives news organizations latitude in reporting on official government proceedings.
Radaris was originally operated by Bitseller Expert Limited. Who owns Bitseller Expert Limited? A report (PDF) obtained from the Cyprus business registry shows this company lists its director as Pavel Kaydash from Moscow. Mr. Kaydash could not be reached for comment.








 Source: Coinstats on X[/caption]
Source: Coinstats on X[/caption]









 (Source: X)[/caption]
According to the threat actor, the stolen data included 380 million customer profiles, containing names, emails, mobile numbers, phone numbers, addresses; information on 358,000 employees, 44 million Loyalty/Gas card numbers, the company’s sales history, among other details.
(Source: X)[/caption]
According to the threat actor, the stolen data included 380 million customer profiles, containing names, emails, mobile numbers, phone numbers, addresses; information on 358,000 employees, 44 million Loyalty/Gas card numbers, the company’s sales history, among other details.

 Source: Chris Pashley's LinkedIn Post[/caption]
Source: Chris Pashley's LinkedIn Post[/caption]

