WordPress Plugin Supply Chain Attack Gets Worse

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

A report from the Government Accountability Office (GAO) highlighted an urgent need to address critical cybersecurity challenges facing the nation.
The post GAO Urges Action to Address Critical Cybersecurity Challenges Facing U.S. appeared first on Security Boulevard.

In the first quarter of 2024, nearly half of all security incidents our team responded to involved multi-factor authentication (MFA) issues, according to the latest Cisco Talos report.
The post Misconfigured MFA Increasingly Targeted by Cybercriminals appeared first on Security Boulevard.
The post The Check Point Challenge: Safeguarding Against the Latest CVE appeared first on Votiro.
The post The Check Point Challenge: Safeguarding Against the Latest CVE appeared first on Security Boulevard.
Organizations face an overwhelming number of vulnerabilities and threats. The traditional approach has been to prioritize exposures—identifying and addressing the most critical vulnerabilities first. However, this method, while logical on the surface, has significant limitations. At Veriti, we advocate for a different strategy: prioritizing actions. By focusing on remediations rather than merely cataloging exposures, we believe […]
The post Prioritizing Exposures vs. Prioritizing Actions appeared first on VERITI.
The post Prioritizing Exposures vs. Prioritizing Actions appeared first on Security Boulevard.
Rate limiting is a well-known technique for limiting network traffic to web servers, APIs, or other online services. It is also one of the methods available to you for blocking DDoS attackers from flooding your system with requests and exhausting network capacity, storage, and memory. You typically define rate-limiting rules in your Web Application Firewall […]
The post 6 Tips for Preventing DDoS Attacks Using Rate Limits appeared first on Security Boulevard.
The tragedy of the commons is a concept in economics and ecology that describes a situation where individuals, acting in their own self-interest, collectively deplete a shared resource. In simpler terms, it's the idea that when a resource is available to everyone without restriction, some individuals tend to overuse it, leading to its eventual depletion and harming everyone in the long run. In the case of Maven Central, we are experiencing an unwitting tyranny by the few.
The post Maven Central and the tragedy of the commons appeared first on Security Boulevard.
Multiple vulnerabilities have been addressed in ADOdb, a PHP database abstraction layer library. These vulnerabilities could cause severe security issues, such as SQL injection attacks, cross-site scripting (XSS) attacks, and authentication bypasses. The Ubuntu security team has released updates to address them in various versions of Ubuntu, including Ubuntu 22.04 LTS, Ubuntu 20.04 LTS, Ubuntu […]
The post Critical ADOdb Vulnerabilities Fixed in Ubuntu appeared first on TuxCare.
The post Critical ADOdb Vulnerabilities Fixed in Ubuntu appeared first on Security Boulevard.
Containerized applications offer several advantages over traditional deployment methods, making them a powerful tool for modern application development and deployment. Understanding the security complexities of containers and implementing targeted security measures is crucial for organizations to protect their applications and data. Adopting specialized security practices, such as Linux live kernel patching, is essential in maintaining […]
The post Navigating Security Challenges in Containerized Applications appeared first on TuxCare.
The post Navigating Security Challenges in Containerized Applications appeared first on Security Boulevard.

McLean, United States of America, 26th June 2024, CyberNewsWire
The post FireTail Unveils Free Access for All to Cutting-Edge API Security Platform appeared first on Security Boulevard.

Red Teaming security assessments aim to demonstrate to clients how attackers in the real world might link together various exploits and attack methods to reach their objectives.
The post Stepping Into the Attacker’s Shoes: The Strategic Power of Red Teaming (Insights from the Field) appeared first on Security Boulevard.

By introducing a mobile device management (MDM) platform into the existing infrastructure, administrators gain the ability to restrict sideloading on managed devices.
The post EU Opens the App Store Gates: A Call to Arms for MDM Implementation appeared first on Security Boulevard.

Many organizations today use a jump server (also known as jump box or jump host) as the intermediary device to access a remote network securely. It is the go-to solution for remote administration of servers and devices and for development and testing environments. It is also commonly used to control vendor access to an organization’s internal systems and to meet compliance in certain industries.
While this is definitely a step up in security from using VPNs, jump server can sometimes create a false sense of security because there still exists security risks and loopholes.
In this blog post, we will first explore the security benefits and risks of a jump server. Finally, we will unveil strategies to mitigate those security risks.
Top 5 Security Benefits of a Jump Server
Top 5 Security Risks of a Jump Server
How to Mitigate Jump Server Security Risks Using Best Practices
Mamori Adds Two Additional Layers of Security to Your Jump Host
When access is centralized, it is easy monitor and manage who access their network, ensuring all access to protected networks are authorized. Centralized access also simplifies managing permissions and security policies. while also making it easier to monitor and log activities.
With centralized access, monitoring traffic and logging activities are simplified. Jump servers also allow session recording, session timeout, and the ability terminate sessions to enhance control and security.
Jump servers should be isolated from the internet and shouldn’t be able to browse the intranet. This reduces the attack surface and adds a layer of defense against external threats.
By limiting direct access to critical systems and databases, jump servers minimize the risk of unauthorized access from any unauthorized sources.
User activity and traffic passing through the controlled central access point can be logged and recorded, which helps meet regulatory.
A compromised jump server can jeopardize the entire network. Also, a compromised user account, a privileged user, or an infected device can jeopardize the entire system and database the jump server protects.
A simple jump server contains a Windows Server with RDP and user accounts from Active Directory. Additional setup and tools can be used to create more secure policies. In some cases, coding and debugging is required, which makes it difficult to add additional security policies.
A misconfigured architecture can completely bypass the jump server and access privileged resources, as indicated in the image below with the non-privileged resource. If the non-privileged resource is compromised, then the privileged resource can be accessed, bypassing the jump server. Because privileged resources are usually databases, many mistakenly think that jump server protects the database. Although jump servers do protect database access (in a way), it is NOT database security, as you’ll see later in this article.
Above: Workstation can circumvent access to privileged resources when the security architecture is misconfigured. Image source: Improsec. 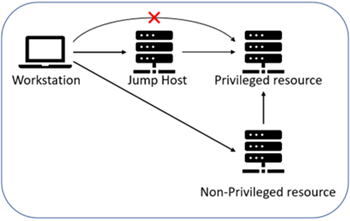
Running outdated software on the jump server is known to expose the jump server to vulnerabilities. Default and weak passwords should be changed, and strong authentication policies should be enforced.
Disgruntled or malicious employees who have access can cause data loss and data breaches. Although all traffic can be monitored, jump servers by default lack the ability immediately respond to insiders who are mass downloading or deleting data.
Simply put, the easiest and simplest way to mitigate jump server security risks is to implement security best practices on your jump server. However, that is easily said than done.
Here at Mamori.io, we make it extremely easy to implement jump server security best practices (including ransomware prevention and cybersecurity best practices).
Below lists the jump server security best practices and how they mitigate the security risks mentioned earlier.
2FA adds another layer of security even when your password is compromised, or if you’re using default password.
Security Risk Mitigated: Credentials Management, Database Security
Mamori’s Approach: Mamori.io uses a zero-trust approach that assumes your password has already been compromised. Every access is secured by MFA, from accessing the network using Zero Trust Network Access (ZTNA) to accessing the database using our Database Privileged User Access (DB PAM) via SSO. Even certain operations within the database, such as mass deleting data, can be authorized to certain individuals and secured using 2FA.
Regularly patching and updating the software and operating system on the jump server is the quickest and easiest way to close security gaps against known vulnerabilities and exploits.
Security Risk Mitigated: Outdated Software
Mamori’s Approach: Even if an external threat uses a known vulnerability to compromise your jump server, your critical resources and database can still be protected by database privileged access controls secured by 2FA.
Only grant access to those who need access. Enforce role-based access so users have the minimal necessary permissions (least-privileged access). This limits the number of potential attack vectors and reduces insider threats.
Security Risk Mitigated: Setup Complications, Misconfigured Architecture and Database Security, Insider Threats
Mamori’s Approach: Mamori provides Privileged Access Management (PAM) to limit jump server access to only those who need access. Once the user connects to the database or privileged resource, Mamori provides Database Privileged Access Management (DB PAM) to limit the user’s access to resource, his visibility (eg. data masking) and the types of operations (eg. read, write, delete, etc.) the user can perform onto those resources.
Comprehensive logging and monitoring allow for the detection of suspicious activities and help with IT audits and compliance. Logging and monitoring also facilitates forensic analysis post-incident, enhancing the overall security posture.
Security Risk Mitigated: Insider Threats, Incident Response
Mamori’s Approach: At Mamori, we believe logging and monitoring is NOT comprehensive if users are able to share accounts. That is why we use a zero-trust approach, where the user, device, location, (and more) needs to be authenticated for access and for certain database operations. Thus, when each session is monitored, logged, and recorded, we ensure that each session can easily be traced back and be used as forensics or incident response.
Strong password policies, such as password complexity, regular changes, and restricting reuse, make it harder for attackers to guess or crack passwords. This strengthens the first line of defense against unauthorized access.
Security Risk Mitigated: Credentials Management and weak passwords
Mamori’s Approach: We encourage the use of strong password policies, but we emphasize on Two Factor Authentication (2FA). That’s because we use a zero-trust approach, where we assume every password is already compromised or will be compromised one day.
Jump servers should only have access to select servers. One practice is to isolate the jump server from other parts of the network, which limits the potential damage of the jump server is compromised. Segmenting a network prevents attacks from moving laterally across the network to access other critical systems.
Security Risk Mitigated: Setup Complications, Misconfigured Architecture
Mamori’s Approach: Mamori uses Zero Trust Network Access (ZTNA) to microsegment a network. The microsegmented network can then be used for the jump server to ensure an isolated, secure environment.
Mamori ensures that only the right user with the right permission has access to the jump server using the following modules and features:
Zero Trust Network Access (ZTNA) – Before a user gets connects to the network, the user’s device and identity is verified using 2FA. Other security policies, such as access restrictions by IP address, can also be enforced.
Privileged Access Management (PAM) – Once a user connects onto the network, policies set forth in the PAM module will restrict or allow that user’s access to the jump server.
After a person connects onto a jump server, the following Mamori modules and features ensure that the person can only view, access, and perform operations that is needed to do his job:
Database Privileged Access Management (DB PAM) – Once a user connects onto a database via a jump server, DB PAM will determine what resources the user has access to and what database operations the user can execute.
SQL Firewall – DB PAM can create rules and privileges on what SQL commands a user can run. You can choose to block all SQL commands or allow specific types of SQL commands.
Data Privacy Policies – You can easily create policies such as data masking policies, who has access to which tables, rows, or columns, and how users can work with those data.
By default, jump servers do not allow you to control uploads and downloads to and from the jump server. When someone needs to upload or download, admins might choose to share passwords, or create a new account with excess privileges that is to be a forgotten account – both of which introduce considerable security risks.
With Mamori’s PAM features, you can set permissions that allow what user(s) is able to upload, download, or do both from the jump server. Permission include having the user request access on-demand, limit access by IP address, or setting a time frame where the user account is granted access. This is another form of securing access that improves both security and workflow efficiency.
Unlike the configuring a jump server, using Mamori requires no coding. We offer a simple dashboard and user interface that even the most non-technical users can create security policies that can mitigate the security risks of your jump server.
By understanding the benefits and addressing the risks associated with jump servers, you can enhance the security of your network while maintaining efficient, controlled, and secure access to critical systems. If you have further questions or need assistance in securing your jump server, feel free to reach out for a detailed consultation.
Schedule a demo with Mamori.io or request your free trial. If you’re a small business with fewer than 20 users, you can use Mamori.io for free.
The post Understanding and Mitigating Jump Server Security Risks appeared first on Security Boulevard.

SANTA CLARA, Calif., June 26, 2024 — At the 16th Information Security Forum and 2024 RSAC Hot Topics Seminar held on June 7, 2024, Richard Zhao, Chief Operating Officer of International Business at NSFOCUS, presented the new picture of cybersecurity in the post-cloud era with his professional insights. Key Highlights Richard’s speech focused on three […]
The post Efficiency is Key to Cybersecurity in the Post-Cloud Era appeared first on NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks..
The post Efficiency is Key to Cybersecurity in the Post-Cloud Era appeared first on Security Boulevard.
Snowflakes has become the latest corporate victim in a cyberattack but how it is playing out is a little different than many breaches.
The post Snowflake Breach appeared first on Security Boulevard.
See how DataDome learns about proxy networks from bots as a service, how BaaS can be detected, and what kind of IP addresses are behind BaaS.
The post Proxies as a Service: How to Identify Proxy Providers via Bots as a Service appeared first on Security Boulevard.
Authors/Presenters:Jiangyi Deng, Yanjiao Chen, Yinan Zhong, Qianhao Miao, Xueluan Gong, Wenyuan Xu
Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open Access.
Originating from the conference’s events situated at the Anaheim Marriott; and via the organizations YouTube channel.
The post USENIX Security ’23 – Catch You and I Can: Revealing Source Voiceprint Against Voice Conversion appeared first on Security Boulevard.
Explore why shadow AI poses a greater risk than shadow IT. See how unmanaged AI tools in the workplace can jeopardize security and lead to harmful consequences.
The post Why Shadow AI is a Bigger Challenge than Shadow IT | Grip appeared first on Security Boulevard.
Let’s explore some of the details behind this escalating threat to SaaS applications, what may be driving it, and what you can do to better protect your SaaS footprint from these types of threats.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on RevealSecurity.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on Security Boulevard.

via the inimitable Daniel Stori at Turnoff.US!
The post Daniel Stori’s ‘The Over Engineer’ appeared first on Security Boulevard.

The LockBit ransomware group is claiming that it hacked into systems at the U.S. Federal Reserve and stole 33TB of data that it will begin leaking as early as Tuesday if the institution doesn’t pay the unspecified ransom. The notorious cybercriminals announced the attack on its dark web leak site on June 23, giving the..
The post LockBit Claims Ransomware Attack on U.S. Federal Reserve appeared first on Security Boulevard.
The 10.6 release of SonarQube includes some significant changes, such as autoscaling in Kubernetes, auto-configuration for C and C++ projects, support for running in a FIPS-enforced environment, set rule priority to uphold your coding standards, easy setup of monorepos, monitoring the time it takes to upgrade, and expanded library coverage for AI/ML developers.
The post SonarQube 10.6 Release Announcement appeared first on Security Boulevard.

Security analysts at Google are developing a framework that they hope will enable large language models (LLMs) to eventually be able to run automated vulnerability research, particularly analyses of malware variants. The analysts with Google’s Project Zero – a group founded a decade ago whose job it is to find zero-day vulnerabilities – have been..
The post Google’s Project Naptime Aims for AI-Based Vulnerability Research appeared first on Security Boulevard.

Copying users’ files and deleting some? Even a cartoon hound knows this isn’t fine.
The post Microsoft Privacy FAIL: Windows 11 Silently Backs Up to OneDrive appeared first on Security Boulevard.
The post Five Signs You’re Using “Good Enough” Automation appeared first on AI Enabled Security Automation.
The post Five Signs You’re Using “Good Enough” Automation appeared first on Security Boulevard.
Learn why HTTPie is a great replacement for curl and how to use it when conducting your own API security testing.
The post Hacking APIs with HTTPie appeared first on Dana Epp's Blog.
The post Hacking APIs with HTTPie appeared first on Security Boulevard.
Effective April 30, 2024 Airbnb, the global vacation rental giant, announced a significant policy change: the prohibition of all indoor security cameras in its listings worldwide. This decision, aims to bolster the privacy of guests and address longstanding concerns about hidden cameras. While the majority of Airbnb’s over 7 million listings did not report having […]
The post Airbnb’s Ban on Indoor Security Cameras: What It Means for Your Personal Cybersecurity appeared first on BlackCloak | Protect Your Digital Life™.
The post Airbnb’s Ban on Indoor Security Cameras: What It Means for Your Personal Cybersecurity appeared first on Security Boulevard.
Distinguished Paper Award Winner
Authors/Presenters:Tadayoshi Kohno, Yasemin Acar, Wulf Loh
Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open Access.
Originating from the conference’s events situated at the Anaheim Marriott; and via the organizations YouTube channel.
The post USENIX Security ’23 – Ethical Frameworks and Computer Security Trolley Problems: Foundations for Conversations appeared first on Security Boulevard.
Stefan Dumitrascu Brings Expertise to AMTSO Board We are delighted to announce that our Chief Technology Officer, Stefan Dumitrascu, has been elected as a Board Member of the Anti-Malware Testing Standards Organisation (AMTSO). What is AMTSO? AMTSO is an international non-profit association dedicated to improving the objectivity, quality, and relevance of anti-malware testing methodologies worldwide. […]
The post Our CTO joins AMTSO Board appeared first on SE Labs Blog.
The post Our CTO joins AMTSO Board appeared first on Security Boulevard.
Designing software from the ground up to be secure, as recommended by the Secure by Design initiative from the Cybersecurity and Infrastructure Security Agency (CISA), has its challenges, especially if it's done at scale. .
The post How platform engineering helps you get a good start on Secure by Design appeared first on Security Boulevard.
Federal agencies need strong security controls and continuous compliance. The Cyber Operational Readiness Assessment (CORA) by the DHS and industry partners enhances critical infrastructure resilience against cyber threats.
The post How AttackIQ Can Bolster CORA Compliance in the Federal Government appeared first on AttackIQ.
The post How AttackIQ Can Bolster CORA Compliance in the Federal Government appeared first on Security Boulevard.
What is a Compliance Report? A compliance report describes how successfully or poorly a company complies with security and business-related regulations. It is distributed to various audiences, including the board, senior executives, regulators, business partners, third-party vendors, etc. Whatever compliance requirements a company may already have, a good rule of thumb is to ensure the […]
The post Top 6 Compliance Reporting Tools in 2024 appeared first on Centraleyes.
The post Top 6 Compliance Reporting Tools in 2024 appeared first on Security Boulevard.
eBPF is one of the most widely used technologies in today’s computing ecosystem, starting from the cloud sector
The post Reverse engineering eBPF programs appeared first on ARMO.
The post Reverse engineering eBPF programs appeared first on Security Boulevard.
Node.js is an open-source, cross-platform JavaScript runtime environment built on the powerful V8 engine from Chrome. It allows you to run JavaScript code outside a web browser, making it popular for building real-time applications and data streaming services. However, like any software, it is not immune to security vulnerabilities. Recently, multiple vulnerabilities were discovered in […]
The post Addressing Node.js Vulnerabilities in Ubuntu appeared first on TuxCare.
The post Addressing Node.js Vulnerabilities in Ubuntu appeared first on Security Boulevard.
Our guide provides essential insights on cyberbullying, helping parents recognize signs and take steps to protect their children's online.
The post What is Cyberbullying: Parents Guide appeared first on SternX Technology.
The post What is Cyberbullying: Parents Guide appeared first on Security Boulevard.
PALO ALTO, Calif. – June 25, 2024 – TuxCare, the enterprise solutions division of CloudLinux and a global innovator in cybersecurity for Linux, today announced that Virtuozzo, the alternative cloud platform leader, now offers TuxCare’s CentOS 7 Extended Lifecycle Support (ELS). Virtuozzo solutions enable virtualization and cloud for service providers and enterprises. For customers […]
The post TuxCare Extended Lifecycle Support Services Now Offered through Virtuozzo appeared first on TuxCare.
The post TuxCare Extended Lifecycle Support Services Now Offered through Virtuozzo appeared first on Security Boulevard.
Google’s initiative to phase out third-party tracking cookies through its Google Privacy Sandbox has encountered criticism from Austrian privacy advocacy group noyb (none of your business). The non-profit alleges that Google’s proposed solution still facilitates user tracking, albeit in a different form. Allegations of Misleading Practices According to noyb, Google’s Privacy Sandbox, marketed as […]
The post Alert: Australian Non-Profit Accuses Google Privacy Sandbox appeared first on TuxCare.
The post Alert: Australian Non-Profit Accuses Google Privacy Sandbox appeared first on Security Boulevard.
Securing the Journey to AI with Thales Sovereign Solutions for AWS
josh.pearson@t…
Mon, 06/24/2024 - 22:28

Amazon Web Services (AWS) is the world's largest cloud service provider. Unsurprisingly, they are committed to providing tools, solutions, and best practices that allow their customers to leverage Generative Artificial Intelligence (GenAI) workloads on AWS securely. Organizations are rapidly employing GenAI to bring increased productivity and creativity to businesses. In nearly all uses of GenAI, the AI models require access to data and that data can be nonpublic and private to the organization. Private and nonpublic data can include trade secrets, personal identifying information, and compliance data.
Thales and AWS have a strong partnership of working together to provide sovereign solutions for AWS customers. In 2022, Thales and AWS jointly unveiled external key management as a Hold Your Own Key (HYOK) strategy in AWS. AWS and Thales continue to jointly engineer and develop enhanced data protection capabilities, focusing on advanced encryption solutions and secure key management to support organizations working to secure their hybrid enterprises.
GenAI is now being rapidly deployed across many verticals along a widely diverse set of use cases. Organizations, large and small, across many industries are looking to gain benefits from GenAI. A partial list of already identified benefits include:
A majority of GenAI options are powered by Large Language Models (LLMs) that are pre-trained with source input data to perform desired tasks such as content generation and code generation.
The AI lifecycle typically encompasses three phases:
Each phase of the AI lifecycle is a potential exposure point for threat actors to engage in cyberattacks. Two methods to limit data exposure and mitigate the risk to cyberattacks for organizations training LLMs in GenAI include:
Before organizations expose nonpublic data to an AI model, they should verify the sensitivity of the data that the GenAI can access is verified. Tools such as Thales Data Discovery and Classification ensure that only properly classified and identified data is available to the AI model and are integral to ensuring that sensitive data is not exposed to or being queried by the AI model.
Each year Thales co-authors the Global Data Threat Report, where over 3,000 security professionals and executives around the world share their security concerns. In the 2023 study, a major concern highlighted was about data leakage regarding AI creating code, regulatory compliance, data privacy, and lack of control. The report found that 68% of the respondents expressed concerns that rapid changes in AI are challenging existing organizational plans.
The chart below summarizes additional organizational concerns about data leakage, privacy concerns, and lack of control over the rapid implementation of AI.

Amazon Q, Bedrock, and SageMaker are a few of the primary AWS offerings that allow AWS customers to quickly develop GenAI solutions, including the AWS AI–powered assistant. Amazon Q is aimed primarily at supporting business use cases and offers solutions that allow organizations the opportunity to integrate and leverage their internal data. Whether that data includes commercial intellectual property, trade secrets, supplier, or customer nonpublic data, organizations must understand how to limit the sensitive data visible to Amazon Q. It is imperative that precautions are taken to ensure no unauthorized apps, processes, or individuals, such as bots or threat actors, can access the nonpublic data.
AWS employs the Nitro System and Nitro Enclaves as their computing backbone, with unparalleled security and performance. AWS has announced extended support for Nitro Systems that will be optimized for GenAI and AI workloads, notably GPU intensive processes. AWS Nitro Enclaves offer an integrated solution with AWS Key Management System (KMS) that enables AWS customers to manage and encrypt sensitive data using encryption keys that the organization owns and controls. The ownership of the keys is managed using the Thales CipherTrust Manager which provides Enterprise Key Management and enables digital sovereignty for AWS customers. In a recent blog, AWS outlined their approach to securing data used for Generative AI.
AWS has developed the Nitro System to fulfill the principles of Secure AI Infrastructure. The first principle isolates your AI data from AWS operators, ensuring its security. The second principle allows you to remove administrative access, enhancing control over your AI data. With Nitro Enclaves and AWS KMS, you can encrypt your sensitive AI data using your keys, store it securely, and transfer it to an isolated compute environment for inferencing. Throughout the process, your data remains encrypted and isolated from your users, software, and AWS operators.
AWS KMS External Key Store (XKS) is integrated with the Thales CipherTrust Cloud Key Management (CCKM) solution so that organizations can keep their encryption keys outside of AWS KMS. This approach is also called Hold Your Own Key (HYOK), which provides sovereign controls. When deploying GenAI solutions, AWS customers can manage the encryption of their nonpublic data using AWS XKS with Thales CCKM.
The XKS collaboration between Thales and AWS has led to the development of services that help organizations maintain control over their encryption keys and manage access to sensitive data securely. These technologies enable organizations to address challenges related to cloud migration, digital sovereignty, and the secure handling of sensitive information across various cloud platforms. Understanding when and how to employ AWS external key management with Thales is a crucial use case for organizations developing in-house AI capabilities and maintaining data security and compliance across different regulatory environments.
Developed with Thales since its inception, the AWS XKS combined with CCKM offers organizations looking to use critical workloads in AI a way to maintain sovereign control of sensitive data throughout their AI journey. Thales enables external key management and is an integral part of a digital sovereignty strategy for organizations that leverage AWS XKS to enhance data security.
By leveraging the Thales external key manager with AWS XKS to manage cryptographic keys securely, organizations have complete confidence that data encryption keys are handled and stored securely, can be backed up and managed external to the Cloud Provider, and use of policy prevents unauthorized access to encrypted data. By managing keys external to the Cloud Provider KMS, organizations can selectively apply encryption based on organizational policy and enterprise key lifecycle management. This organizational enterprise external key management allows organizations to isolate data protection, including the option to store the encryption keys external to the Cloud Provider. This isolation is a key risk mitigation strategy. Using Thales for external key management in AWS supported platforms, organizations who may be concerned about data loss or leakage can disable access to the cryptographic keys, providing an additional layer of security and assurance. With the wrapping keys being inaccessible, organizations ensure that encrypted data remains encrypted even if other online defenses are compromised.
Thales external key manager implements robust auditing and monitoring capabilities. Monitoring is crucial for detecting unauthorized access or anomalies in data usage, which is often an early or first indicator of a security breach or detection of anomalous behavior. Thales CipherTrust Manager provides audit logging that enables organizations to track how and when data is accessed and by whom.
As a cybersecurity aligned solution, Thales increases the protection of organizational data that is an essential foundational building block to AI research and models. Thales and AWS work together to provide a robust framework for securing sensitive data used by AI systems, ensuring compliance with data protection regulations, and maintaining the integrity and confidentiality of the data.
For organizations looking to secure their confidential data, whether on-prem, in a cloud provider or in the hybrid enterprise, Thales offers CipherTrust Transparent Encryption (CTE). CTE facilitates Bring Your Own Encryption (BYOE) for organizations by maintaining nonpublic data in an encrypted state until the time of use by an authorized service or entity. The Thales transparent data encryption solution automatically encrypts and decrypts data as it is read and written to storage, operating invisibly to applications and business processes. Thales CTE enables organizations to protect their data without altering existing workflows.
Cybersecurity best practices dictate that organizations employ enterprise key lifecycle management including issuing, rotating, and backing up the encryption keys used to protect nonpublic data. The Thales CTE solution along with CipherTrust Manager allows organizations to own, instantiate, and use their keys, which they manage and store independently, crucial for maintaining control in BYOE scenarios. Thales transparent encryption provides granular access controls, enhancing security by ensuring data cannot be decrypted without appropriate permissions. The Thales BYOE solution provides comprehensive auditing capabilities that support regulatory compliance by monitoring encrypted data access and key usage. With support for various environments, including cloud, hybrid, and on-premises, Thales CTE ensures organizations can apply BYOE consistently across all supported platforms and locations.
Managing how the GenAI can access nonpublic data is essential. Organizations need to ensure only authorized processes can access and monitor the processes that are accessing or attempting to access the nonpublic data. A best practice and risk mitigation approach is to use dynamic credential rotation to ensure human or machine credentials cannot be obtained and improperly used. Advantages to organizations using dynamic credential rotation include:
Thales CipherTrust Secrets Management provides a solution to support automated dynamic credential management. Employing just-in-time or dynamic credential rotation can significantly improve an organization's security posture and improve the overall security of an AI initiative by making it more difficult for attackers to exploit stolen credentials. It also results in improved audit results to ensure only authorized services are accessing nonpublic data.
We understand that GenAI is important to our customers. Where security and compliance are concerned, Thales and AWS are here for your journey. Thales has over 50 corporate AI related initiatives and we follow a secure AI development methodology to ensure we are benefiting from AI without jeopardizing data integrity or privacy.
Thales encryption and key management solutions are used to protect organizational data as the organization commences on internal AI development efforts. Thales offers a wide range of security solutions. The broad range of Thales security solutions include those offered by Imperva that enables enterprises protect their applications and APIs anywhere at scale.
Thales data security solutions provide granular protection of applications and credentials -- protecting both human and machine identities, and data at rest, in use, and in motion.
The post Securing the Journey to AI with Thales Sovereign Solutions for AWS appeared first on Security Boulevard.
PKI ensures secure digital communication by verifying online entities. Root and intermediate certificates create a trust chain, ensuring information integrity.
The post Intermediate vs Root Certificates appeared first on Security Boulevard.
In today’s business landscape, adhering to the Payment Card Industry Data Security Standard (PCI DSS) is essential. As a business owner, have you ever considered how secure your client’s credit card information is? In the modern digital age, safeguarding sensitive data is crucial. Protecting your clients’ card information not only maintains their trust in your […]
The post What’s New in PCI DSS Version 4.1? appeared first on Kratikal Blogs.
The post What’s New in PCI DSS Version 4.1? appeared first on Security Boulevard.
History doesn’t repeat itself, but it often rhymes. As AppSec evolves towards a new playbook, here’s what we can learn from IT’s journey. Just over 20 years ago, Watts Humphrey declared that every business was a software business. Not everyone agreed. No one would image that, sports shoe manufacturers, automakers and even barbecue brands are […]
The post Back to the Future: What AppSec Can Learn From 30 Years of IT Security appeared first on OX Security.
The post Back to the Future: What AppSec Can Learn From 30 Years of IT Security appeared first on Security Boulevard.
According to Gartner, who coined the term, AI TRiSM (AI Trust, Risk and Security Management) ensures an AI model’s governance, trustworthiness, fairness, reliability, robustness, efficacy, and data protection. This includes solutions and techniques for model interpretability and explainability, AI data protection, and attack resistance. “Organizations that do not consistently manage AI risks are exponentially more […]
The post What is AI TRiSM? And Why Is It Important? appeared first on Centraleyes.
The post What is AI TRiSM? And Why Is It Important? appeared first on Security Boulevard.
Weekly Threat Intelligence Report
Date: June 24, 2024
Prepared by: David Brunsdon, Threat Intelligence - Security Engineer, HYAS
Malware developers will use all sorts of techniques to obfuscate their C2 location and keep security analysts from being able to understand the operation of their malware. One common technique is to have the malware communicate with a popular online service, such as Pastebin, where the malware will contact a URL that responds with the IP address of the C2 server. This type of design keeps the C2 address out of the malware, and allows the C2 operator to change or remove the C2 destination as needed. If the right service is chosen, then this request might go unnoticed because it’s seen as regular traffic.
We detonated a malware sample on Windows 7 that was identified as containing both StealC and Vidar, and we found the same technique being used on the gaming platform, Steam. In this case, the malware requests the page of a specific user account. The steam user account name contains the IP address of a component of the C2 infrastructure. Steam even shows a history of the username, so we can see previous IPs that have existed in this field.
Steam is an interesting choice as a vector for retrieving a C2 destination because it’s a gaming platform that isn’t typically used on corporate infrastructure, except perhaps in gaming companies. It is commonly used in residential communications however. A more traditional choice would be a service that is typically seen within an organization's network traffic, like a Microsoft service.
Although a direct relationship has not been confirmed, Vidar is a stealer known to be used by Scattered Spider, aka UNC3944. They are a criminal organization responsible for many high profile victims, including MGM Grand, Caesars, Snowflake, LastPass, Apple, Walmart, and Zendesk. Recently the head of the organization was arrested by the FBI, but their operations continue.
Learn more about the
HYAS Insight threat intelligence solution.
MD5: 8cfe70cf4f35c7f9b4ddba327d44c1f8
https://tria.ge/240617-fvryqazelj/behavioral1
https://steamcommunity.com/profiles/76561199699680841
(Image: Malicious usage of a Steam profile that contains the C2 location)
65.109.240.138 (Currently offline)
ISP:Hetzner Online GmbH
Country: Finland
ASN: AS24940
65.109.243.78 (Currently offline)
ISP:Hetzner Online GmbH
Country: Finland
ASN: AS24940
95.216.142.162
ISP:Hetzner Online GmbH
Country: Finland
ASN: AS24940
With this address we can see there is a single port open, 443, which has a banner that contains a recent date/time stamp. We can attempt to pivot off of this potentially unique banner using free accounts with Shodan or Censys.
With Censys we can take that banner in hex (to avoid problems with formatting) and create a custom search query to look for matches on that ASN.
Censys Query:
(services.banner_hex="485454502f312e3120333032204d6f7665642054656d706f726172696c790d0a5365727665723a206e67696e780d0a446174653a20203c52454441435445443e0d0a436f6e74656e742d547970653a20746578742f68746d6c0d0a436f6e74656e742d4c656e6774683a203133380d0a436f6e6e656374696f6e3a206b6565702d616c6976650d0a4c6f636174696f6e3a2068747470733a2f2f676f6f676c652e636f6d0d0a") and autonomous_system.name=`HETZNER-AS`
From our search, we end up with a list of sixteen IP addresses on this ASN that present the same service banner and are mostly-if-not-entirely Vidar C2.
Vidar C2 IOCs:
95.216.165.53
116.203.13.231
195.201.47.189
116.203.166.11
116.203.167.34
116.203.4.20
49.13.32.109
162.55.53.18
195.201.248.182
95.216.142.162
95.216.182.224
78.47.205.62
116.203.13.42
116.203.13.51
195.201.46.4
That same malware also contacted Telegram which is using a similar technique to host a different address.
https://t.me/memve4erin
https://tria.ge/240617-fvryqazelj/behavioral2
162.55.53.18:9000
ISP:Hetzner Online GmbH
ASN:AS24940
Country: Germany
5.42.67.8
ISP: LetHost LLC
Location: Russia
ASN: AS210352
In our detonation, after Telegram was contacted, another IP was contacted, which may have come from a prior entry in the Telegram field (unconfirmed, no historical record for this field). HYAS Insight, our threat intelligence solution, was able to provide some recent information about C2 usage on this server. This login screen is for Risepro malware, however, so it’s possible that multiple actors or campaigns are using this same server. It’s not uncommon for a malicious server to be used in such a way.
Date: 2024/06/15 19:48:21 UTC (Most recent data)
C2 Admin URL: http://5.42.67.8:8081/
Actor IP: 109.95.78.5
Geo: 55.434553 36.696945
Device User Agent: Mozilla/5.0 (Linux; Android 14; 23021RAA2Y Build/UKQ1.230917.001; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/125.0.6422.165 Mobile Safari/537.36
(Image: Login screen of Risepro C2 hosted on server)
(Image: Actor who logged into C2 server’s GPS location, southwest of Moscow)
Want to see some malware detonated? View our
webinar on-demand.
Want more threat intel on a weekly basis?
Follow HYAS on LinkedIn
Follow HYAS on X
Read past reports:
Tracking an Active Remcos Malware Campaign
Revealing LOTL Techniques Used by An Active Remcos Malware Campaign
Agent Tesla Unmasked: Revealing Interrelated Cyber Campaigns
Risepro Malware Campaign On the Rise
An efficient and expedient investigation is the best way to protect your enterprise. HYAS Insight provides threat and fraud response teams with unparalleled visibility into everything you need to know about the attack.This includes the origin, current infrastructure being used and any infrastructure.
Read how the HYAS Threat Intelligence team uncovered and mitigated a Russian-based cyber attack targeting financial organizations worldwide.
Polymorphic Malware Is No Longer Theoretical: BlackMamba PoC.
Polymporphic, Intelligent and Fully Autonomous Malware: EyeSpy PoC.
Five Proven Techniques to Optimize Threat Intelligence
Leveraging ASNs and Pivoting to Uncover Malware Campaigns
Disclaimer: This Threat Intelligence Report is provided “as is” and for informational purposes only. HYAS disclaims all warranties, express or implied, regarding the report’s completeness, accuracy, or reliability. You are solely responsible for exercising your own due diligence when accessing and using this Report's information. The analyses expressed in this Report reflect our current understanding of available information based on our independent research using the HYAS Insight platform. The Report’s inclusion of any companies, organizations, or ASNs does not imply any wrongdoing on their part; it is simply an indication of where digital threat activities have been observed. HYAS reserves the right to update the Report as additional information is made known to us.
The post StealC & Vidar Malware Campaign Identified appeared first on Security Boulevard.
Securing AI-Native Platforms: A Comprehensive Approach with SecureFLO Securing AI-Native Platforms: A Comprehensive Approach with SecureFLO In the rapidly evolving landscape of artificial intelligence, ensuring robust cybersecurity measures is more critical than ever. AI-native platforms, which leverage advanced machine learning and data analytics, are at the forefront of technological innovation. However, they also face unique […]
The post Securing AI-Native Platforms: A Comprehensive Approach with SecureFLO appeared first on Cyber security services provider, data privacy consultant | Secureflo.
The post Securing AI-Native Platforms: A Comprehensive Approach with SecureFLO appeared first on Security Boulevard.
Distinguished Paper Award Winner
Authors/Presenters: Alexandra Nisenoff, Maximilian Golla, Miranda Wei, Juliette Hainline, Hayley Szymanek, Annika Braun, Annika Hildebrandt, Blair Christensen, David Langenberg
Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open Access.
Originating from the conference’s events situated at the Anaheim Marriott; and via the organizations YouTube channel.
The post USENIX Security ’23 – A Two-Decade Retrospective Analysis of a University’s Vulnerability to Attacks Exploiting Reused Passwords appeared first on Security Boulevard.

via the comic artistry and dry wit of Randall Munroe, creator of XKCD
The post Randall Munroe’s XKCD ‘Electric VS Gas’ appeared first on Security Boulevard.
Say goodbye to passwords! Passkeys are the next generation of authentication, offering enhanced security and convenience. Learn how passkeys work, their benefits over passwords, and why they are the future of secure online access.
The post Passkeys: The Future of Passwordless Authentication appeared first on Security Boulevard.

Authors/Presenters:Thorsten Eisenhofer, Erwin Quiring, Jonas Möller, Doreen Riepel, Thorsten Holz, Konrad Rieck
Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open Access.
Originating from the conference’s events situated at the Anaheim Marriott; and via the organizations YouTube channel.
The post USENIX Security ’23 – No More Reviewer #2: Subverting Automatic Paper-Reviewer Assignment Using Adversarial Learning appeared first on Security Boulevard.
Achieving CMMC compliance can feel like a daunting task, but there are tools available to help expedite the process, saving time and money. The tools explored here help address the 110 security controls outlined in NIST SP 800-171, which is the basis for CMMC Level 2. Below are 5 categories of tools to explore, alongside […]
The post CMMC Tools for Compliance + Assessment appeared first on PreVeil.
The post CMMC Tools for Compliance + Assessment appeared first on Security Boulevard.