WordPress Plugin Supply Chain Attack Gets Worse

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.
The P2Pinfect worm targeting Redis servers has been updated with ransomware and cryptocurrency mining payloads.
The post P2Pinfect Worm Now Dropping Ransomware on Redis Servers appeared first on SecurityWeek.
Let’s explore some of the details behind this escalating threat to SaaS applications, what may be driving it, and what you can do to better protect your SaaS footprint from these types of threats.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on RevealSecurity.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on Security Boulevard.

Copying users’ files and deleting some? Even a cartoon hound knows this isn’t fine.
The post Microsoft Privacy FAIL: Windows 11 Silently Backs Up to OneDrive appeared first on Security Boulevard.
A Mirai-like botnet has started exploiting a critical-severity vulnerability in discontinued Zyxel NAS products.
The post Recent Zyxel NAS Vulnerability Exploited by Botnet appeared first on SecurityWeek.
Safeguarding your Linux environment from potential threats is more critical than ever. Whether you’re managing a small server or an extensive network, having hands-on knowledge of intrusion detection systems (IDS) is essential. IDS tools play a vital role in maintaining the security and integrity of your system. This guide will walk you through the practical […]
The post Intrusion Detection in Linux: Protecting Your System from Threats appeared first on TuxCare.
The post Intrusion Detection in Linux: Protecting Your System from Threats appeared first on Security Boulevard.
As per recent reports, cybersecurity experts uncovered a troubling development on the Python Package Index (PyPI) – a platform used widely by developers to find and distribute Python packages. A malicious package named ‘crytic-compilers‘ was discovered, mimicking the legitimate ‘crytic-compile’ library developed by Trail of Bits. This fraudulent package was designed with sinister intent: to […]
The post Python Developers Targeted Via Fake Crytic-Compilers Package appeared first on TuxCare.
The post Python Developers Targeted Via Fake Crytic-Compilers Package appeared first on Security Boulevard.
A years-long espionage campaign has targeted telecoms companies in Asia with tools associated with Chinese groups.
The post Cyber Assault on Asian Telecoms Traced to Chinese State Hackers appeared first on SecurityWeek.
A threat actor targeting Chinese-speaking victims has been using the SquidLoader malware loader in recent attacks.
The post Highly Evasive SquidLoader Malware Targets China appeared first on SecurityWeek.
The BadSpace backdoor is being distributed via drive-by attacks involving infected websites and JavaScript downloaders.
The post New BadSpace Backdoor Deployed in Drive-By Attacks appeared first on SecurityWeek.
China-linked threat actor Velvet Ant leveraged a legacy F5 BIG-IP appliance for three-year access to a victim’s network.
The post Chinese Hackers Leveraged Legacy F5 BIG-IP Appliance for Persistence appeared first on SecurityWeek.
As retailers compete in an increasingly competitive marketplace, they invest a great deal of resources in becoming household names. But brand recognition is a double-edged sword when it comes to cybersecurity. The bigger your name, the bigger the cyber target on your back. Data breaches in the retail sector cost an average of $3.28 million...
The post Navigating Retail: Overcoming the Top 3 Identity Security Challenges appeared first on Silverfort.
The post Navigating Retail: Overcoming the Top 3 Identity Security Challenges appeared first on Security Boulevard.
Security researchers at Cisco Talos and Volexity flag two Pakistani espionage campaigns targeting Indian government entities.
The post Pakistani Threat Actors Caught Targeting Indian Gov Entities appeared first on SecurityWeek.
CISA urges federal agencies to apply mitigations for an exploited Progress Telerik vulnerability as soon as possible.
The post CISA Warns of Progress Telerik Vulnerability Exploitation appeared first on SecurityWeek.

The rise in U.S.-politics-themed scams indicates that adversarial nation states understand the significance of election years.
The post Chinese Threats Aim for Government Sector appeared first on Security Boulevard.

Location tracking service leaks PII, because—incompetence? Seems almost TOO easy.
The post Tile/Life360 Breach: ‘Millions’ of Users’ Data at Risk appeared first on Security Boulevard.
The first quarter of 2024 painted a concerning picture of security threats for enterprise organizations: information leaks and breaches exposed sensitive data across major corporations.
The post Q1 2024: A Wake-up Call for Insider Threats appeared first on Security Boulevard.
The zero-day is tagged as CVE-2024-32896 and described as an elevation of privilege issue in Pixel Firmware.
The post Google Warns of Pixel Firmware Zero-Day Under Limited, Targeted Exploitation appeared first on SecurityWeek.
The Windows vulnerability carries a CVSS severity score of 9.8/10 and can be exploited by via specially crafted malicious MSMQ packets.
The post Patch Tuesday: Remote Code Execution Flaw in Microsoft Message Queuing appeared first on SecurityWeek.
Patch Tuesday: Adobe fixes critical flaws and warns of the risk of code execution attacks on Windows and macOS platforms.
The post Adobe Plugs Code Execution Holes in After Effects, Illustrator appeared first on SecurityWeek.

Not our fault, says CISO: “UNC5537” breached at least 165 Snowflake instances, including Ticketmaster, LendingTree and, allegedly, Advance Auto Parts.
The post Ticketmaster is Tip of Iceberg: 165+ Snowflake Customers Hacked appeared first on Security Boulevard.
Arm warns that CVE-2024-4610, a Mali GPU kernel driver vulnerability addressed two years ago, is exploited in attacks.
The post Arm Warns of Exploited Kernel Driver Vulnerability appeared first on SecurityWeek.

Akamai warns that a Chinese threat actor is exploiting years-old remote code execution vulnerabilities in ThinkPHP in new attacks.
The post Chinese Hackers Exploit Old ThinkPHP Vulnerabilities in New Attacks appeared first on SecurityWeek.
It remembers everything you do on your PC. Security experts are raging at Redmond to recall Recall.
The post Microsoft Recall is a Privacy Disaster appeared first on Security Boulevard.
Google and Microsoft warn of elevated risks of cyber threats facing the 2024 Paris Olympics, especially from Russian threat actors.
The post Google, Microsoft: Russian Threat Actors Pose High Risk to 2024 Paris Olympics appeared first on SecurityWeek.
Multiple Chinese state-sponsored groups have targeted a Southeast Asian government in a years-long cyberespionage campaign.
The post Multiple Chinese APTs Targeted Southeast Asian Government for Two Years appeared first on SecurityWeek.
A recent revelation in the cybersecurity realm uncovers a concerning development dubbed GHOSTENGINE, a cryptojacking campaign employing a sophisticated method to bypass security measures. In this blog, we’ll look at the GHOSTENGINE exploit in detail, shedding light on its modus operandi and implications for digital security. Understanding The GHOSTENGINE Exploit Cybersecurity researchers have unearthed […]
The post GHOSTENGINE Exploit: Vulnerable Drivers Facing Attack appeared first on TuxCare.
The post GHOSTENGINE Exploit: Vulnerable Drivers Facing Attack appeared first on Security Boulevard.

Train people. It makes a difference. In organizations without security awareness training, 34% of employees are likely to click on malicious links or comply with fraudulent requests.
The post Cybersecurity Training Reduces Phishing Threats – With Numbers to Prove It appeared first on Security Boulevard.
Attention Apache Flink users! The U.S. Cybersecurity and Infrastructure Security Agency (CISA) recently added an Apache Flink vulnerability to its Known Exploited Vulnerabilities Catalog, highlighting evidence of its active exploitation. Apache Flink is a popular open-source framework for processing large streams of data. It’s widely used in big data analytics and real-time applications. However, like […]
The post CISA Alert: Urgent Update Needed for Apache Flink Vulnerability appeared first on TuxCare.
The post CISA Alert: Urgent Update Needed for Apache Flink Vulnerability appeared first on Security Boulevard.
Cybersecurity researchers are demonstrating how malware could steal data collected by the new Windows Recall feature.
The post Researchers Show How Malware Could Steal Windows Recall Data appeared first on SecurityWeek.

Snowflake, Inc. says NO, threatening legal action against those who say it was. But reports are coming in of several more massive leaks from other Snowflake customers.
The post Was the Ticketmaster Leak Snowflake’s Fault? appeared first on Security Boulevard.
CISA has added an old Oracle WebLogic flaw tracked as CVE-2017-3506 to its known exploited vulnerabilities catalog.
The post CISA Warns of Attacks Exploiting Old Oracle WebLogic Vulnerability appeared first on SecurityWeek.
Law enforcement reveals the identities of eight cybercriminals linked to recently disrupted malware loaders.
The post Identities of Cybercriminals Linked to Malware Loaders Revealed appeared first on SecurityWeek.
PoC code targeting a recent Check Point VPN zero-day has been released as Censys identifies 14,000 internet-accessible appliances.
The post PoC Published for Exploited Check Point VPN Vulnerability appeared first on SecurityWeek.
The post Risk vs. Threat vs. Vulnerability: What is the difference? appeared first on Click Armor.
The post Risk vs. Threat vs. Vulnerability: What is the difference? appeared first on Security Boulevard.
Over 600,000 SOHO routers belonging to a single ISP and infected with the Chalubo trojan were rendered inoperable.
The post Mysterious Threat Actor Used Chalubo Malware to Brick 600,000 Routers appeared first on SecurityWeek.
Malicious campaign exploits high-severity XSS flaws in three WordPress plugins to backdoor websites.
The post Critical WordPress Plugin Flaws Exploited to Inject Malicious Scripts and Backdoors appeared first on SecurityWeek.
The TrickBot botnet and other malware droppers have been targeted by international law enforcement in Operation Endgame.
The post TrickBot and Other Malware Droppers Disrupted by Law Enforcement appeared first on SecurityWeek.
Okta raises the alarm on credential stuffing attacks targeting endpoints used for cross-origin authentication.
The post Okta Warns of Credential Stuffing Attacks Targeting Cross-Origin Authentication appeared first on SecurityWeek.
The US announced that the 911 S5 (Cloud Router) botnet, likely the world’s largest, has been dismantled and its administrator arrested.
The post Massive 911 S5 Botnet Dismantled, Chinese Mastermind Arrested appeared first on SecurityWeek.
The recently disclosed Check Point VPN attacks involve the zero-day vulnerability CVE-2024-24919, which allows hackers to obtain passwords.
The post Check Point VPN Attacks Involve Zero-Day Exploited Since April appeared first on SecurityWeek.

Source: securityboulevard.com – Author: Rohan Timalsina On May 2, 2024, the City of Helsinki announced the data breach targeting its Education Division. However, the breach was discovered on April 30, 2024, and an investigation was promptly carried out. It was found that it has impacted tens of thousands of students, guardians, and personnel, causing considerable […]
La entrada City of Helsinki Data Breach: What You Need to Know – Source: securityboulevard.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: securelist.com – Author: CFR team Marketplace fraud is nothing new. Cybercriminals swindle money out of buyers and sellers alike. Lately, we’ve seen a proliferation of cybergangs operating under the Fraud-as-a-Service model and specializing in tricking users of online marketplaces, in particular, message boards. Criminals are forever inventing new schemes for stealing personal data and […]
La entrada Message board scams – Source: securelist.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: securelist.com – Author: Kaspersky ICS CERT Global statistics Statistics across all threats In the first quarter of 2024, the percentage of ICS computers on which malicious objects were blocked decreased by 0.3 pp from the previous quarter to 24.4%. Compared to the first quarter of 2023, the percentage decreased by 1.3 pp. Percentage of ICS […]
La entrada Threat landscape for industrial automation systems, Q1 2024 – Source: securelist.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Views: 0Source: www.securityweek.com – Author: Ionut Arghire Thousands of computers are at risk of complete takeover after hackers added a backdoor to the installer for the Justice AV Solutions (JAVS) Viewer software, Rapid7 warned in an advisory. According to Rapid7, the hackers injected a backdoor in the JAVS Viewer v8.3.7 installer that is being distributed […]
La entrada JAVS Courtroom Audio-Visual Software Installer Serves Backdoor – Source: www.securityweek.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
Backdoored JAVS courtroom recording and management software installer puts thousands at risk of complete takeover.
The post JAVS Courtroom Audio-Visual Software Installer Serves Backdoor appeared first on SecurityWeek.
The Change Healthcare ransomware attack has taken a third cruel twist. A new ransomware group, RansomHub, has listed the organisation as a victim on its dark web leak site, saying it has 4 TB of “highly selective data,” which relates to “all Change Health clients that have sensitive data being processed by the company.”
The announcement follows a series of events that require some unpacking.
Change Healthcare is one of the largest healthcare technology companies in the USA, responsible for the flow of payments between payers, providers, and patients. It was attacked on Wednesday February 21, 2024, by a criminal “affiliate” working with the ALPHV ransomware group, which led to huge disruptions in healthcare payments. Patients were left facing enormous pharmacy bills, small medical providers teetered on the edge of insolvency, and the government scrambled to keep the money flowing and the lights on.
American Hospital Association (AHA) President and CEO Rick Pollack described the attack as “the most significant and consequential incident of its kind against the US health care system in history.”
The notorious ALPHV ransomware group claimed responsibility, chalking up Change Healthcare as one of a raft of healthcare victims in what looked like a deliberate campaign against the sector at the start of 2024.
ALPHV used the ransomware-as-a-service (RaaS) business model, selling the software and infrastructure used to carry out ransomware attacks to criminal gangs known as affiliates, in return for a share of the ransoms they extorted.
On March 3, a user on the RAMP dark web forum claimed they were the affiliate behind the attack, and that ALPHV had stolen the entirety of a $22 million ransom paid by Change Healthcare. Shortly after, the ALPHV group disappeared in an unconvincing exit scam designed to make it look as if the group’s website had been seized by the FBI.
ALPHV’s exit left Change Healthcare with nothing to show for its $22 million payment, a disgruntled affiliate looking for a ransom, and very possibly two different criminal gangs—ALPHV and its affiliate—in possession of a huge trove of stolen data.
Now, a month later, a newcomer ransomware group, RansomHub has listed Change Healthcare as a victim on its website.
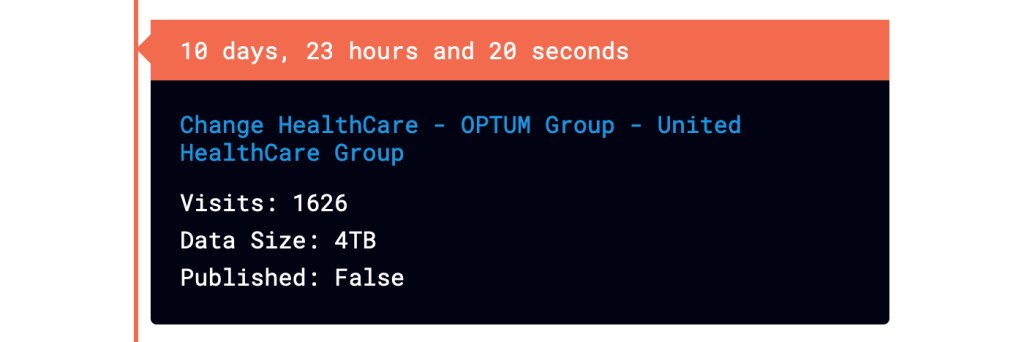
While some have speculated that Change Healthcare has suffered a second attack, the RansomHub site itself makes the connection to the events surrounding February 21 quite clear:
As an introduction we will give everyone a fast update on what happened previously and on the current situation.
ALPHV stole the ransom payment (22 Million USD) that Change Healthcare and United Health payed in order to restore their systems and prevent the data leak.
HOWEVER we have the data and not ALPHV.
RansomHub first appeared in late February and its arrival dovetails neatly with ALPHV’s disappearance in very early March, leading some to think they are the same group under two different names.
The statement also pours water on the idea that RansomHub is a rebrand of the ALPHV group with its suggestion that “we have the data and not ALPHV.” However, any public statement like this has to be tempered by the fact that ransomware groups are prolific liars.
It’s not uncommon for affiliates to work with multiple RaaS providers, so the most likely explanation is that having lost its money to ALPHV, the affiliate that ransacked Change Healthcare has paired up with a different ransomware group.
Whatever the reason, there is no comfort in it for Change Healthcare. Having apparently already paid a ransom thirty times greater than the average demand, it now has to decide whether it’s going to pay out again.
For everyone else, it’s a lesson in how devastating ransomware can be, and how badly things can go even when you pay a ransom.
Our business solutions remove all remnants of ransomware and prevent you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.