WordPress Plugin Supply Chain Attack Gets Worse

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

30,000 websites at risk: Check yours ASAP! (800 Million Ostriches Can’t Be Wrong.)
The post WordPress Plugin Supply Chain Attack Gets Worse appeared first on Security Boulevard.

A report from the Government Accountability Office (GAO) highlighted an urgent need to address critical cybersecurity challenges facing the nation.
The post GAO Urges Action to Address Critical Cybersecurity Challenges Facing U.S. appeared first on Security Boulevard.

In the first quarter of 2024, nearly half of all security incidents our team responded to involved multi-factor authentication (MFA) issues, according to the latest Cisco Talos report.
The post Misconfigured MFA Increasingly Targeted by Cybercriminals appeared first on Security Boulevard.
More than 100,000 websites are affected by a supply chain attack injecting malware via a Polyfill domain.
The post Polyfill Supply Chain Attack Hits Over 100k Websites appeared first on SecurityWeek.

Red Teaming security assessments aim to demonstrate to clients how attackers in the real world might link together various exploits and attack methods to reach their objectives.
The post Stepping Into the Attacker’s Shoes: The Strategic Power of Red Teaming (Insights from the Field) appeared first on Security Boulevard.

By introducing a mobile device management (MDM) platform into the existing infrastructure, administrators gain the ability to restrict sideloading on managed devices.
The post EU Opens the App Store Gates: A Call to Arms for MDM Implementation appeared first on Security Boulevard.
Snowflakes has become the latest corporate victim in a cyberattack but how it is playing out is a little different than many breaches.
The post Snowflake Breach appeared first on Security Boulevard.


The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada Why Red TeamsPlay a Central Rolein Helping OrganizationsSecure AI Systems se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
Let’s explore some of the details behind this escalating threat to SaaS applications, what may be driving it, and what you can do to better protect your SaaS footprint from these types of threats.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on RevealSecurity.
The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on Security Boulevard.

Year after year, the cyber talent gap is increasing — currently estimated to have 3,5 million open positions worldwide — presenting all sorts of headaches for leaders and the organizations they aim to protect. Moreover, organizations have a short window to identify, foster and hopefully retain a pipeline of emerging cybersecurity leaders to ensure the […]
La entrada Recommended Skills for a Cyber Security Career se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

The LockBit ransomware group is claiming that it hacked into systems at the U.S. Federal Reserve and stole 33TB of data that it will begin leaking as early as Tuesday if the institution doesn’t pay the unspecified ransom. The notorious cybercriminals announced the attack on its dark web leak site on June 23, giving the..
The post LockBit Claims Ransomware Attack on U.S. Federal Reserve appeared first on Security Boulevard.
I've been covering Blink deals on Amazon for some time now, and have seen some good bundle deals before, but none compare to this one.
Right now, you can get a Blink Video Doorbell ($59.99 when bought by itself), a Blink Outdoor 4 camera ($99.99 purchased separately), and a Sync Module 2 ($49.99 purchased separately) for $59.99 with this Blink bundle. This is the lowest price the package deal has reached—by a long shot—according to price-checking tools.



You can also expand your coverage by adding two or three Blink Outdoor 4 cameras and still get a very good discount. This sale is part of Amazon's official early Prime Day deals, according to its press release, which also served as the official announcement that Prime Day 2024 will take place July 16-17.
This bundle has all the basics you need to set up your Blink security system. The Blink Video Doorbell has two-way audio so that you can communicate with guests from your phone, 1080p resolution, and infrared night vision. The Blink Outdoor 4 is the latest Blink outdoor camera and a great budget option that competes well with other outdoor cameras. The Sync Module 2 lets you use local storage for your video files instead of paying for cloud storage.
Note that you will need a Blink subscription to use all of this bundle's features. The Blink subscription plan starts at $30 a year for Blink Basic. For $100/year, you can get Blink Plus, which offers more features, including support for an unlimited number of devices.


Security analysts at Google are developing a framework that they hope will enable large language models (LLMs) to eventually be able to run automated vulnerability research, particularly analyses of malware variants. The analysts with Google’s Project Zero – a group founded a decade ago whose job it is to find zero-day vulnerabilities – have been..
The post Google’s Project Naptime Aims for AI-Based Vulnerability Research appeared first on Security Boulevard.

Copying users’ files and deleting some? Even a cartoon hound knows this isn’t fine.
The post Microsoft Privacy FAIL: Windows 11 Silently Backs Up to OneDrive appeared first on Security Boulevard.
Effective April 30, 2024 Airbnb, the global vacation rental giant, announced a significant policy change: the prohibition of all indoor security cameras in its listings worldwide. This decision, aims to bolster the privacy of guests and address longstanding concerns about hidden cameras. While the majority of Airbnb’s over 7 million listings did not report having […]
The post Airbnb’s Ban on Indoor Security Cameras: What It Means for Your Personal Cybersecurity appeared first on BlackCloak | Protect Your Digital Life™.
The post Airbnb’s Ban on Indoor Security Cameras: What It Means for Your Personal Cybersecurity appeared first on Security Boulevard.
Read more of this story at Slashdot.
Stefan Dumitrascu Brings Expertise to AMTSO Board We are delighted to announce that our Chief Technology Officer, Stefan Dumitrascu, has been elected as a Board Member of the Anti-Malware Testing Standards Organisation (AMTSO). What is AMTSO? AMTSO is an international non-profit association dedicated to improving the objectivity, quality, and relevance of anti-malware testing methodologies worldwide. […]
The post Our CTO joins AMTSO Board appeared first on SE Labs Blog.
The post Our CTO joins AMTSO Board appeared first on Security Boulevard.
Designing software from the ground up to be secure, as recommended by the Secure by Design initiative from the Cybersecurity and Infrastructure Security Agency (CISA), has its challenges, especially if it's done at scale. .
The post How platform engineering helps you get a good start on Secure by Design appeared first on Security Boulevard.
Five WordPress plugins were injected with malicious code that creates a new administrative account.
The post Several Plugins Compromised in WordPress Supply Chain Attack appeared first on SecurityWeek.
eBPF is one of the most widely used technologies in today’s computing ecosystem, starting from the cloud sector
The post Reverse engineering eBPF programs appeared first on ARMO.
The post Reverse engineering eBPF programs appeared first on Security Boulevard.
Node.js is an open-source, cross-platform JavaScript runtime environment built on the powerful V8 engine from Chrome. It allows you to run JavaScript code outside a web browser, making it popular for building real-time applications and data streaming services. However, like any software, it is not immune to security vulnerabilities. Recently, multiple vulnerabilities were discovered in […]
The post Addressing Node.js Vulnerabilities in Ubuntu appeared first on TuxCare.
The post Addressing Node.js Vulnerabilities in Ubuntu appeared first on Security Boulevard.
Google’s initiative to phase out third-party tracking cookies through its Google Privacy Sandbox has encountered criticism from Austrian privacy advocacy group noyb (none of your business). The non-profit alleges that Google’s proposed solution still facilitates user tracking, albeit in a different form. Allegations of Misleading Practices According to noyb, Google’s Privacy Sandbox, marketed as […]
The post Alert: Australian Non-Profit Accuses Google Privacy Sandbox appeared first on TuxCare.
The post Alert: Australian Non-Profit Accuses Google Privacy Sandbox appeared first on Security Boulevard.

History doesn’t repeat itself, but it often rhymes. As AppSec evolves towards a new playbook, here’s what we can learn from IT’s journey. Just over 20 years ago, Watts Humphrey declared that every business was a software business. Not everyone agreed. No one would image that, sports shoe manufacturers, automakers and even barbecue brands are […]
The post Back to the Future: What AppSec Can Learn From 30 Years of IT Security appeared first on OX Security.
The post Back to the Future: What AppSec Can Learn From 30 Years of IT Security appeared first on Security Boulevard.

The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada Best Practices for Cyber Crisis Management se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
In the United States, there is no national, statutory, cross-sector minimum standard for information security. No national law defineswhat would be considered reasonable security in matters involving data breaches. The federal and state governments have various statutes, regulations, policies, and caselaw covering elements of cybersecurity, like data breach notification and data privacy.But all of these […]
La entrada A Guide to Defining Reasonable Cybersecurity se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada AWS Cloud Security Checklist se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access this content. You can register for free. Thank you. The CISO2CISO Advisors Team.
La entrada Attacking .NET se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

The U.S. Department of Homeland Security (DHS) was tasked in Executive Order 14110: Safe, Secure, and Trustworthy Development and Use of Artificial Intelligence to develop safety and security guidelines for use by critical infrastructure owners and operators. DHS developed these guidelines in coordination with the Department of Commerce, the Sector Risk Management Agencies (SRMAs) for […]
La entrada MITIGATING ARTIFICIAL INTELLIGENCE (AI) RISK: Safety and Security Guidelinesfor Critical Infrastructure Ownersand Operators se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Enlarge (credit: Getty Images)
WordPress plugins running on as many as 36,000 websites have been backdoored in a supply-chain attack with unknown origins, security researchers said on Monday.
So far, five plugins are known to be affected in the campaign, which was active as recently as Monday morning, researchers from security firm Wordfence reported. Over the past week, unknown threat actors have added malicious functions to updates available for the plugins on WordPress.org, the official site for the open source WordPress CMS software. When installed, the updates automatically create an attacker-controlled administrative account that provides full control over the compromised site. The updates also add content designed to goose search results.
“The injected malicious code is not very sophisticated or heavily obfuscated and contains comments throughout making it easy to follow,” the researchers wrote. “The earliest injection appears to date back to June 21st, 2024, and the threat actor was still actively making updates to plugins as recently as 5 hours ago.”
Read more of this story at Slashdot.
Say goodbye to passwords! Passkeys are the next generation of authentication, offering enhanced security and convenience. Learn how passkeys work, their benefits over passwords, and why they are the future of secure online access.
The post Passkeys: The Future of Passwordless Authentication appeared first on Security Boulevard.

En 2023, la tensión estratégica ha vuelto a ocupar un primer plano. A la guerra iniciada por la invasión rusa de Ucrania en 2022 hay que sumar el nuevo conflicto en Gaza, desencadenado por el ataque terrorista de Hamás a Israel el 7 de octubre. La posibilidad de que el conflicto derive en una mayor […]
La entrada Informe Anual de Seguridad Nacional 2023 se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Multiple bad actors are using the Rafel RAT malware in about 120 campaigns aimed at compromising Android devices and launching a broad array of attacks that range from stealing data and deleting files to espionage and ransomware. Rafel RAT is an open-source remote administration tool that is spread through phishing campaigns aimed at convincing targets..
The post Rafel RAT Used in 120 Campaigns Targeting Android Device Users appeared first on Security Boulevard.

 Source: X[/caption]
Source: X[/caption]

In this episode of the Shared Security Podcast, the team debates the Surgeon General’s recent call for social media warning labels and explores the pros and cons. Scott discusses whether passwords should be stored in web browsers, potentially sparking strong opinions. The hosts also provide an update on Microsoft’s delayed release of CoPilot Plus PCs […]
The post Social Media Warning Labels, Should You Store Passwords in Your Web Browser? appeared first on Shared Security Podcast.
The post Social Media Warning Labels, Should You Store Passwords in Your Web Browser? appeared first on Security Boulevard.

© Derek Abella
Read more of this story at Slashdot.
The Payment Card Industry Data Security Standard (PCI DSS) is a global cornerstone for safeguarding cardholder data. PCI DSS version 4.0, the most recent iteration, emphasises a dynamic, risk-based approach to security, compelling organisations to tailor their controls to their unique environments. PCI DSS penetration tests are crucial for meeting and maintaining security standards. Within …
PCI DSS Penetration Testing Guide Read More »
The post PCI DSS Penetration Testing Guide appeared first on Security Boulevard.
ISO 27001, the internationally recognised standard for information security management systems (ISMS), provides a framework for organisations to protect their valuable information assets. Penetration testing is crucial in preventing data breaches and maintaining the business’s reputation. ISO 27001 strongly recommends it as a critical tool for assessing an organisation’s security posture and ensuring compliance with …
Learn about ISO 27001 Penetration Testing and its requirements Read More »
The post Learn about ISO 27001 Penetration Testing and its requirements appeared first on Security Boulevard.
Read more of this story at Slashdot.

Long simmering suspicions about the loyalty of Kaspersky Software, a cybersecurity firm headquartered in Russia, came to a head this week after the U.S. government banned the sale of the company’s software, effective July 20th, to both companies and individual consumers. In addition, the U.S. Treasury Department has placed sanctions on 12 senior leaders of..
The post U.S. Bans Sale of Kaspersky Cybersecurity Software appeared first on Security Boulevard.
Recently, we hosted Ross Randall, Director of Technology at Lamar County School District in Georgia, and Tim Miles, Director of Technology at Steamboat Springs School District in Colorado, for a summer-inspired live webinar focused on fortifying your district’s multilayered cybersecurity strategy. From beach balls to firewalls, Ross and Tim generously shared their practical insights, […]
The post Ross Randall’s 3 Essential Tips to Strengthening Your District’s Multilayered Cybersecurity appeared first on ManagedMethods.
The post Ross Randall’s 3 Essential Tips to Strengthening Your District’s Multilayered Cybersecurity appeared first on Security Boulevard.
In our purple team service, we try to take a depth and quality approach and run many different functionally diverse test cases for a given technique. In this blog, I will describe our process of defining and implementing test cases for our purple team runbooks. The goal of this blog post is to provide the community with a bit more information about how we implement test cases for logon session enumeration, what preventative controls might be, and how this process can be applied to other techniques.
We wanted to develop a logical numbering system to separate test cases for each technique. After a couple of iterations of our purple team service, we started to deliberately select test cases and run variations based on three distinct categories:
Defining test cases in this manner allows us to triangulate a technique’s coverage estimation rather than treat the techniques in the MITRE ATT&CK matrix as a bingo card where we run net session and net1 session, fill in the box for this technique, and move on to the next one. After running each test case during the purple team assessment, we look for whether the test case was prevented, detected, or observed (telemetry) by any security controls the organization may have.
Let’s dive into logon session enumeration by deconstructing the functional differences between three distinct procedures. If you want to learn more (or want to apply this methodology yourself), you can find out more about the process we use to examine the function call stack of tools in Nathan’s Beyond Procedures: Digging into the Function Call Stack and Jared’s On Detection: Tactical to Functional series.
We can start by examining the three distinct procedures that SharpHound implements. Rohan blogged about the three different methods SharpHound uses. SharpHound can attempt to use all three depending on the context it’s running under and what arguments are passed to it. The implementation of each procedure can be found here: NetSessionEnum, NetWkstaEnum, and GetSubKeyNames in the SharpHoundCommon library. Matt also talks about this in his BOFHound: Session Integration blog.
Here is a breakdown of each of the three unique procedures implemented in SharpHound for remote session enumeration:
Distinct Procedure #1: Network Session Enumeration (NetSessionEnum)
NetSessionEnum is a Win32 API implemented in netapi32.dll. The image below shows where each tool is implemented in the function call stack:
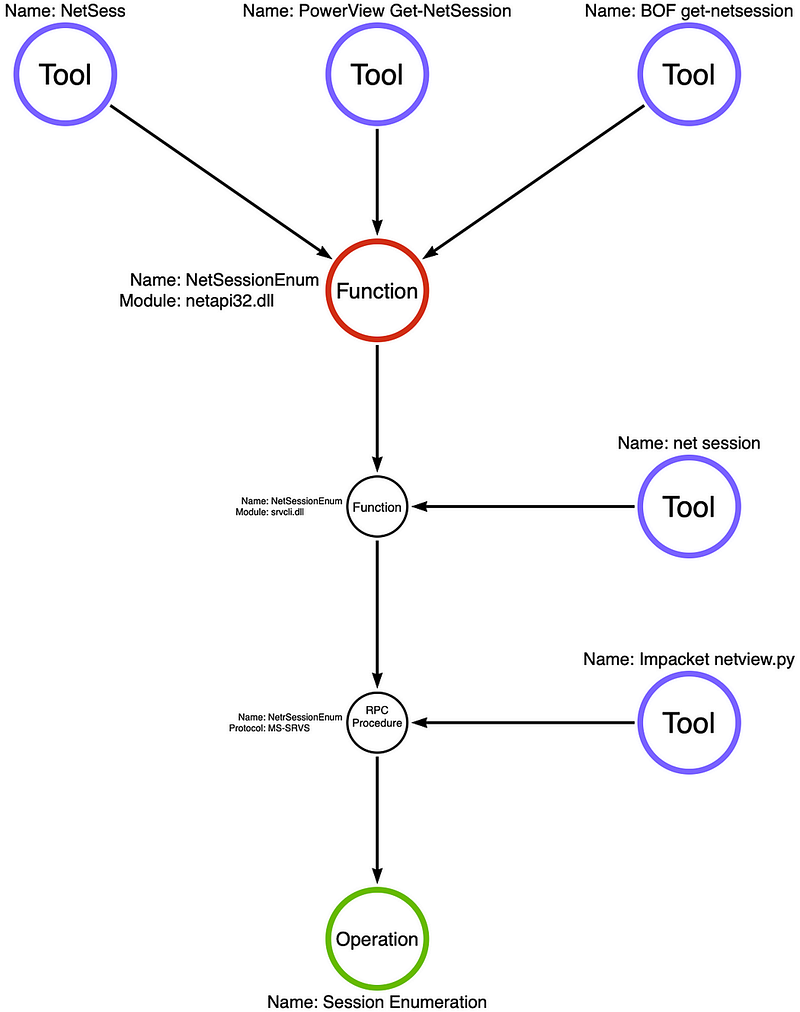
This Win32 API returns a list of active remote or network logon sessions. These two blogs (Netwrix and Compass Security) go into detail about which operating systems allow “Authenticated Users” to query logon sessions and how to check and restrict access to this API remotely by altering the security descriptor in the HKLM/SYSTEM/CurrentControlSet/Services/LanmanServer/DefaultSecurity/SrvsvcSessionInfo registry key. If we read Microsoft’s documentation on the RPC server, we see the MS-SRVS RPC server is only implemented via the \PIPE\srvsvc named pipe (RPC servers can also be commonly implemented via TCP as well). As Microsoft’s documentation states, named pipes communicate over CIFS\SMB via port 445.
In our purple team service, we usually target the organization’s most active file server for two reasons. First, port 445 (SMB) will generally be open from everywhere on the internal network for this server. Second, this server has the most value to an attacker since it could contain hundreds or even thousands of user-to-machine mappings an attacker could use for “user hunting.”
Distinct Procedure #2: Interactive, Service, and Batch Logon Session Enumeration (NetWkstaUserEnum)
NetWkstaUserEnum is also a Win32 API implemented in netapi32.dll. Below is the breakdown of the function call stack and where each tool is implemented:
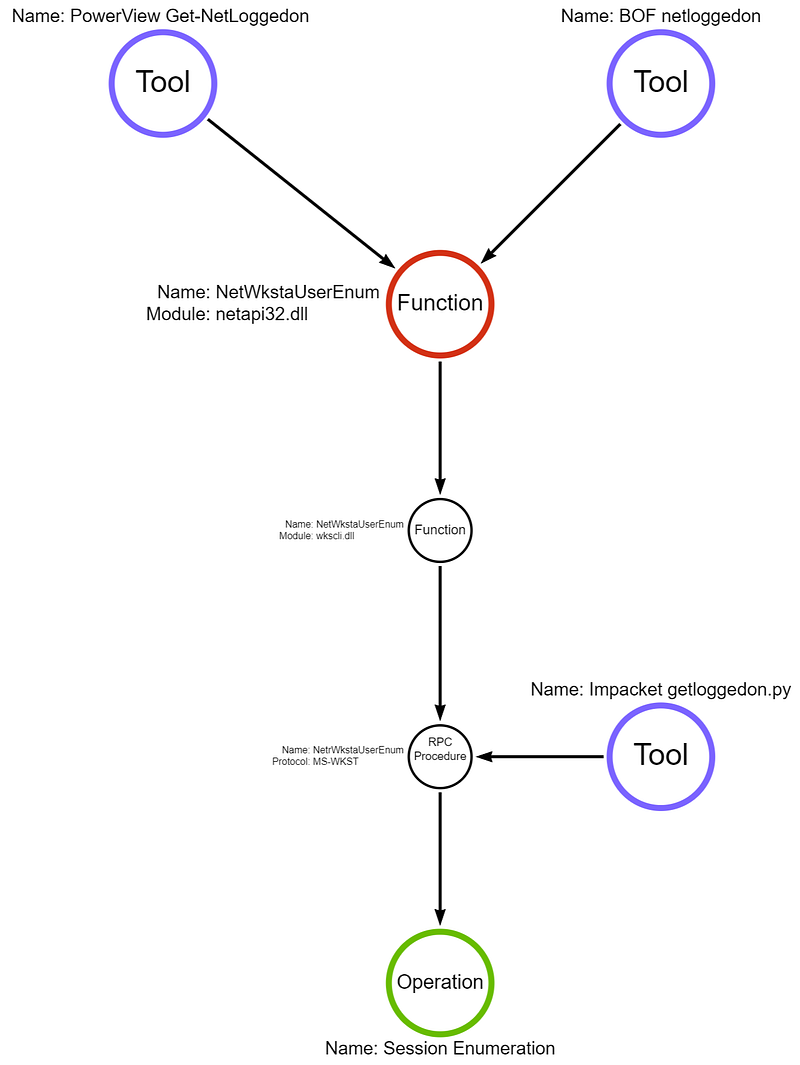
As Microsoft documentation says: “This list includes interactive, service, and batch logons” and “Members of the Administrators, and the Server, System, and Print Operator local groups can also view information.” This API call has different permission requirements and returns a different set of information than the NetSessionEnum API call; however, just like NetSessionEnum, the RPC server is implemented only via the \PIPE\wkssvc named pipe. Again, this blog from Compass Security goes into more detail about the requirements.
Since this, by default, requires administrator or other privileged rights on the target machine, we will again attempt to target file servers and usually get an access denied response when running this procedure. As a detection engineer, if someone attempts to enumerate sessions, do we have the telemetry even if they are unsuccessful? Next, we will attempt to target a workstation on which we have administrator rights to enumerate sessions using this minor variation in a different test case.
Distinct Procedure #3: Interactive Session Enumeration (RegEnumKeyExW)
Note: I’m only showing the function call stack of RegEnumKeyExW, SharpHound calls OpenRemoteBaseKey to get a handle to the remote key before calling RegEnumKeyExW. I also left out calls to API sets in this graph.
RegEnumKeyExW is, again, a Win32 API implemented in advapi32.dll. Below is the breakdown of the function call stack and where each tool is implemented:
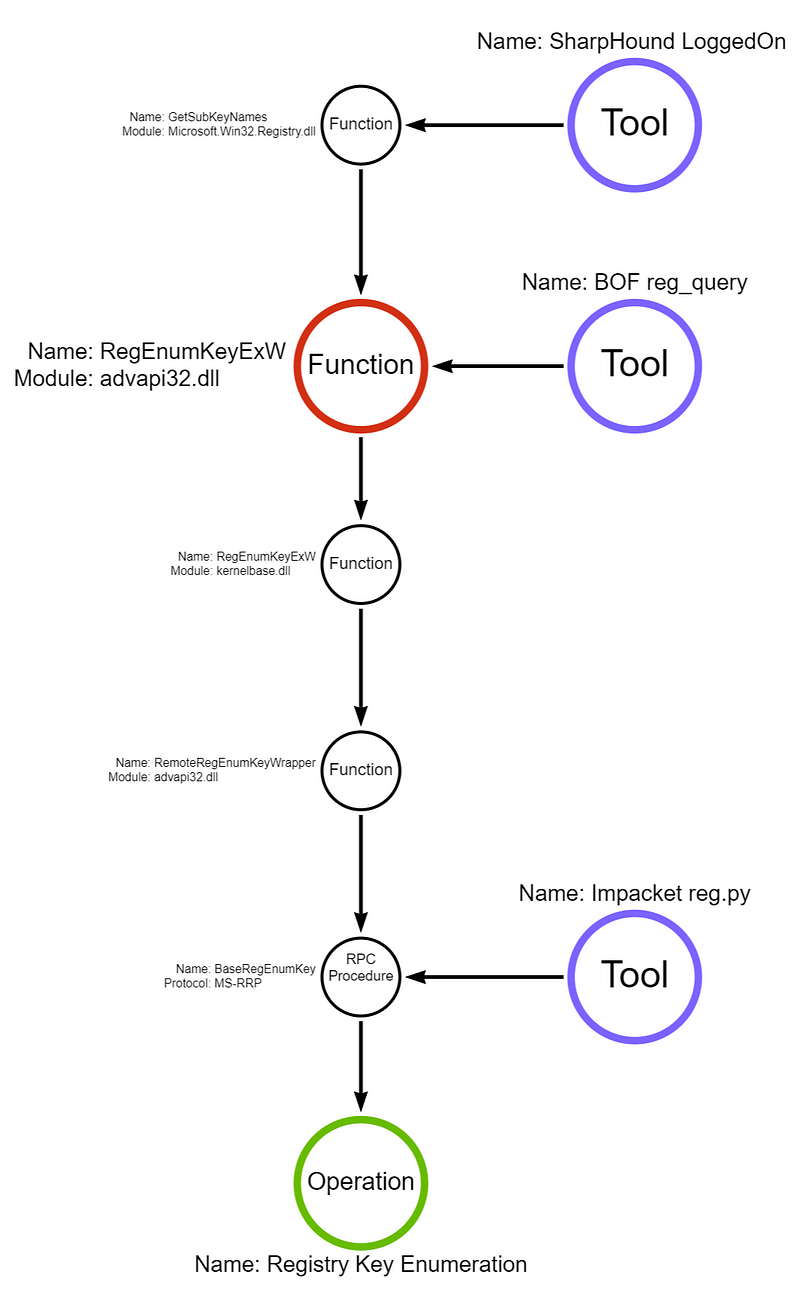
As Microsoft documentation says, the remote system “requires the Remote Registry service to be running on the remote computer.” Again, this blog from Compass Security goes into more detail about the requirements, but by default, the service is disabled on workstation operating systems like Windows 11 and 10 and set to trigger start on server operating systems by interacting with the \PIPE\winreg named pipe. If the remote registry service is running (or triggerable), then the HKEY_USERS hive can be queried for a list of subkeys. These subkeys contain SIDs for users that are interactively logged on. Like NetWkstaUserEnum and NetSessionEnum, the RPC server is implemented only via the \PIPE\winreg named pipe.
Now that we have a diverse set of procedures and tooling examples that use a variety of execution modalities, we can start creating test cases to run for this technique. Below, I have included an example set of test cases and associated numbering system using each of the three distinct procedures and altering the execution modality for each one.
You can also find a full TOML runbook for the examples below here: https://ghst.ly/session-enumeration-runbook. All of the test cases are free or open source and can be executed via an Apollo agent with the Mythic C2 framework.
For example, our numbering looks like: Test Case X.Y.Z
A sample set of test cases we might include:
Network Session Enumeration (NetSessionEnum)
Interactive, Service, and Batch Logon Session Enumeration (NetWkstaUserEnum)
Interactive Session Enumeration (RegEnumKeyExW)
After executing each test case, we can determine if the test case was prevented, detected, or observed. Tracking information like this allows us to provide feedback on your controls and predict how likely they would detect or prevent an adversary’s arbitrary selection of procedure or execution modality. Also, we space test cases about 10 minutes apart; name artifacts like files, registry keys, and processes by their corresponding test case number; and alternate the machine and source user we are executing from to make finding observable telemetry easier. We may include or exclude certain test cases based on the organization’s security controls. For example, if they block and alert on all powershell.exe usage, we aren’t going to run 40 test cases across multiple techniques that attempt to call the PowerShell binary.
By researching and deconstructing each tool and looking at the underlying function call stacks, we found that regardless of which distinct procedure or execution modality was used, they all used three different RPC servers, each implemented using named pipes. This will also allow us to triangulate detection coverage and help determine if a custom or vendor-based rule is looking for a brittle indicator or a tool-specific detail\toolmark.
We now have a fairly broad set of test cases for a runbook that accounts for a wide variety of attacker tradecraft for this technique. Knowing this as a blue teamer or detection engineer will allow me to implement a much more comprehensive detection strategy for this particular technique around the three named pipes we discovered. This allows us to write robust detection rules, rather than looking for the string “Get-NetSession” in a PowerShell script. Would this produce a perfect detection for session enumeration? No. Does this include every single way an attacker can determine where a user is logged? No. Does deconstructing adversary tradecraft in this manner vastly improve our coverage for the technique? Absolutely.
In my next post, I will cover many log sources native to Windows (I’m counting Sysmon as native) and a couple of EDRs that allow us to detect logon session enumeration via named pipes (or TCP in some cases). Some of these sources you might be familiar with, others aren’t very well documented. Each of these log sources can be enabled and shipped to a centralized place like a SIEM. Each source has its requirements, provides a different context, and has its pros and cons for use in a detection rule.
Deconstructing Logon Session Enumeration was originally published in Posts By SpecterOps Team Members on Medium, where people are continuing the conversation by highlighting and responding to this story.
The post Deconstructing Logon Session Enumeration appeared first on Security Boulevard.
ASUS announces major Firmware Update ASUS recently issued a firmware update to resolve a critical security vulnerability affecting seven different variants of its router models. Identified as CVE-2024-3080 with a CVSS v3 severity score of 9.8 (critical), the vulnerability permits remote attackers to take control of the affected router models without needing any login credentials. [...]
The post CVE-2024-3080: ASUS warns Customers about the latest Authentication Bypass Vulnerability detected Across seven Router Models appeared first on Wallarm.
The post CVE-2024-3080: ASUS warns Customers about the latest Authentication Bypass Vulnerability detected Across seven Router Models appeared first on Security Boulevard.

Spend more on security! Car and truck dealers fall back on pen and paper as huge SaaS provider gets hacked (again).
The post 30,000 Dealerships Down — ‘Ransomware’ Outage Outrage no. 2 at CDK Global appeared first on Security Boulevard.
Different models of access control offer unique methods and benefits. The three primary models are Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC), and Discretionary Access Control (DAC).
The post Understanding Access Control Models: RBAC, ABAC, and DAC appeared first on Security Boulevard.
