Reading view
iFixit says new Arm Surface hardware “puts repair front and center”
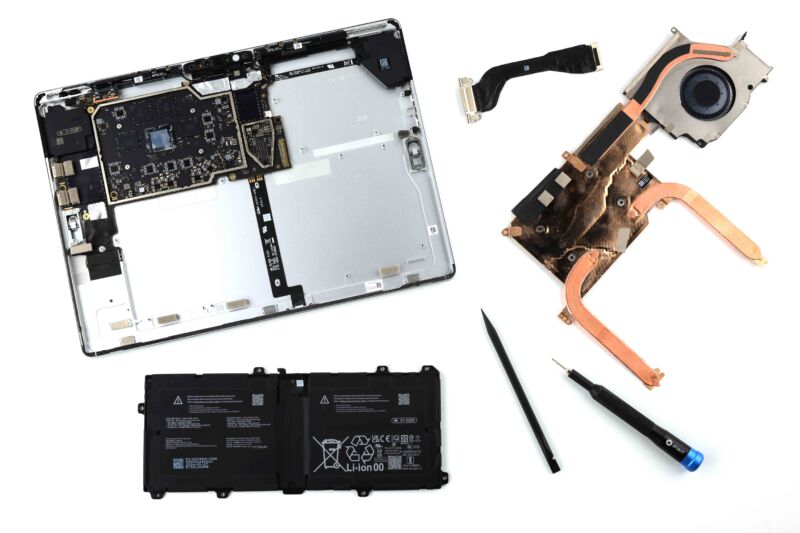
Enlarge / Microsoft's 11th-edition Surface Pro, as exploded by iFixit. Despite adhesive holding in the screen and the fact that you need to remove the heatsink to get at the battery, it's still much more repairable than past Surfaces or competing tablets. (credit: iFixit)
For a long time, Microsoft's Surface hardware was difficult-to-impossible to open and repair, and devices as recent as 2019's Surface Pro 7 still managed a repairability score of just 1 out of 10 on iFixit's scale. 2017's original Surface Laptop needed to be physically sliced apart to access its internals, making it essentially impossible to try to fix the machine without destroying it.
But in recent years, partly due to pressure from shareholders and others, Microsoft has made an earnest effort to improve the repairability of its devices. The company has published detailed repair manuals and videos and has made changes to its hardware designs over the years to make it easier to open them without breaking them and easier to replace parts once you’re inside. Microsoft also sells some first-party parts for repairs, though not every part from every Surface is available, and Microsoft and iFixit have partnered to offer other parts as well.
Now, iFixit has torn apart the most recent Snapdragon X-powered Surface Pro and Surface Laptop devices and has mostly high praise for both devices in its preliminary teardown video. Both devices earn an 8 out of 10 on iFixit's repairability scale, thanks to Microsoft's first-party service manuals, the relative ease with which both devices can be opened, and clearly labeled internal components.
New TikTag Attack Targets Arm CPU Security Feature
Researchers have targeted the MTE security feature in Arm CPUs and showed how attackers could bypass protections.
The post New TikTag Attack Targets Arm CPU Security Feature appeared first on SecurityWeek.
Ukraine Detains Suspects Behind Bot Farms and Kremlin’s Propaganda Machinery

Russian Intelligence Installed Spyware in Campaign
The woman sold or rented these accounts in exchange for cryptocurrency on online Russian underground marketplaces. Russian intelligence used these accounts and numbers to hack phones of Ukrainian military personnel by sending phishing emails containing spyware that collected sensitive confidential data. Russian hackers were recently observed using legitimate remote monitoring and management (RMM) software to spy on Ukraine and its allies. [caption id="attachment_77338" align="aligncenter" width="1024"] Source: SBU[/caption]
According to the SBU, the accounts hosted on this bot farm were also used to spread pro-Kremlin propaganda purporting as ordinary Ukrainian citizens.
Another 30-year-old man from Dnipro allegedly registered nearly 15,000 fake accounts on various social networks and messaging platforms using Ukrainian SIM cards. He sold these accounts to Russian intelligence services on darknet forums.
[caption id="attachment_77337" align="aligncenter" width="1024"]
Source: SBU[/caption]
According to the SBU, the accounts hosted on this bot farm were also used to spread pro-Kremlin propaganda purporting as ordinary Ukrainian citizens.
Another 30-year-old man from Dnipro allegedly registered nearly 15,000 fake accounts on various social networks and messaging platforms using Ukrainian SIM cards. He sold these accounts to Russian intelligence services on darknet forums.
[caption id="attachment_77337" align="aligncenter" width="1024"] Source: SBU[/caption]
Both suspects face up to three years in prison or a fine if found guilty. The investigation continues.
Source: SBU[/caption]
Both suspects face up to three years in prison or a fine if found guilty. The investigation continues.
Russian Bot Farms Used Since Invasion Started
Russia has used bot farms to disseminate Kremlin propaganda, incite panic and manipulate narratives since the beginning of its Ukrainian invasion. The Ukrainian authorities have busted dozens of bot farms and arrested hundreds of people across the country who operate them. In December 2022, they dismantled more than a dozen bot farms. In September of that year, two bot farms were taken down, while in August a group that operated more than 1 million bots was also dismantled. Bot farm operators typically receive payments in Russian rubles, a prohibited currency in Ukraine. These activities continued in the second year of the war, where the Ukrainian Cyber Police raided 21 locations across the country and seized computer equipment, mobile phones and more than 250 GSM gateways. This included 150,000 SIM cards of different mobile operators used in the illicit activities to create fake social media profiles.Arm Warns of Exploited Kernel Driver Vulnerability
Arm warns that CVE-2024-4610, a Mali GPU kernel driver vulnerability addressed two years ago, is exploited in attacks.
The post Arm Warns of Exploited Kernel Driver Vulnerability appeared first on SecurityWeek.