5 Essential Cybersecurity Measures for Protecting IoT Devices



Enlarge / The peloton passing through a sunflowers field during the stage eight of the 110th Tour de France in 2023. (credit: David Ramos/Getty Images)
Most readers probably did not anticipate seeing a Tour de France preview on Ars Technica, but here we are. Cycling is a huge passion of mine and several other staffers, and this year, a ton of intrigue surrounds the race, which has a fantastic route. So we're here to spread Tour fever.
The three-week race starts Saturday, paradoxically in the Italian region of Tuscany. Usually, there is a dominant rider, or at most two, and a clear sense of who is likely to win the demanding race. But this year, due to rider schedules, a terrible crash in early April, and new contenders, there is more uncertainty than usual. A solid case could be made for at least four riders to win this year's Tour de France.
For people who aren't fans of pro road cycling—which has to be at least 99 percent of the United States—there's a great series on Netflix called Unchained to help get you up to speed. The second season, just released, covers last year's Tour de France and introduces you to most of the protagonists in the forthcoming edition. If this article sparks your interest, I recommend checking it out.
Enlarge (credit: Aurich Lawson)
In 2017, Kathleen Odean thought she had found the last cell phone plan she would ever need. T-Mobile was offering a mobile service for people age 55 and over, with an "Un-contract" guarantee that it would never raise prices.
"I thought, wow, I can live out my days with this fixed plan," Odean, a Rhode Island resident who is now 70 years old, told Ars last week. Odean and her husband switched from Verizon to get the T-Mobile deal, which cost $60 a month for two lines.
Despite its Un-contract promise, T-Mobile in May 2024 announced a price hike for customers like Odean who thought they had a lifetime price guarantee on plans such as T-Mobile One, Magenta, and Simple Choice. The $5-per-line price hike will raise her and her husband's monthly bill from $60 to $70, Odean said.

Enlarge / A mysterious assassin is targeting Jedi masters in The Acolyte. (credit: Disney+)
The Star Wars franchise is creeping up on the 50-year mark for the original 1977 film that started it all, and Disney+ has successfully kept things fresh with its line of live-action Star Wars spinoff series. The Mandalorian and Andor were both unquestionably popular and critical successes, while The Book of Boba Fett ultimately proved disappointing, focusing less on our favorite bounty hunter and more on setting up the third season of The Mandalorian. Obi-Wan Kenobi and Ahsoka fell somewhere in between, bolstered by strong performances from its leads but often criticized for sluggish pacing.
It's unclear where the latest addition to the TV franchise, The Acolyte, will ultimately fall, but the first five episodes aired thus far bode well for its place in the growing canon. The series eschews the usual Star Wars space-battle fare for a quieter, space Western detective story—who is killing the great Jedi masters of the galaxy?—with highly choreographed fight scenes that draw heavily from the martial arts. And like its predecessors, The Acolyte is recognizably Star Wars. Yet it also boasts a unique aesthetic style that is very much its own.
(Spoilers below for episodes 1 through 5 of The Acolyte.)

Enlarge / Someone just asked what it would look like if their girlfriend was a Smurf. Better add another rack of servers! (credit: Getty Images)
Late last week, both Bloomberg and The Washington Post published stories focused on the ostensibly disastrous impact artificial intelligence is having on the power grid and on efforts to collectively reduce our use of fossil fuels. The high-profile pieces lean heavily on recent projections from Goldman Sachs and the International Energy Agency (IEA) to cast AI's "insatiable" demand for energy as an almost apocalyptic threat to our power infrastructure. The Post piece even cites anonymous "some [people]" in reporting that "some worry whether there will be enough electricity to meet [the power demands] from any source."
Digging into the best available numbers and projections available, though, it's hard to see AI's current and near-future environmental impact in such a dire light. While generative AI models and tools can and will use a significant amount of energy, we shouldn't conflate AI energy usage with the larger and largely pre-existing energy usage of "data centers" as a whole. And just like any technology, whether that AI energy use is worthwhile depends largely on your wider opinion of the value of generative AI in the first place.
While the headline focus of both Bloomberg and The Washington Post's recent pieces is on artificial intelligence, the actual numbers and projections cited in both pieces overwhelmingly focus on the energy used by Internet "data centers" as a whole. Long before generative AI became the current Silicon Valley buzzword, those data centers were already growing immensely in size and energy usage, powering everything from Amazon Web Services servers to online gaming services, Zoom video calls, and cloud storage and retrieval for billions of documents and photos, to name just a few of the more common uses.


Enlarge (credit: Aurich Lawson | Id | GDC)
John Romero remembers the moment he realized what the future of gaming would look like.
In late 1991, Romero and his colleagues at id Software had just released Catacomb 3-D, a crude-looking, EGA-colored first-person shooter that was nonetheless revolutionary compared to other first-person games of the time. "When we started making our 3D games, the only 3D games out there were nothing like ours," Romero told Ars in a recent interview. "They were lockstep, going through a maze, do a 90-degree turn, that kind of thing."
Despite Catacomb 3-D's technological advances in first-person perspective, though, Romero remembers the team at id followed its release by going to work on the next entry in the long-running Commander Keen series of 2D platform games. But as that process moved forward, Romero told Ars that something didn't feel right.

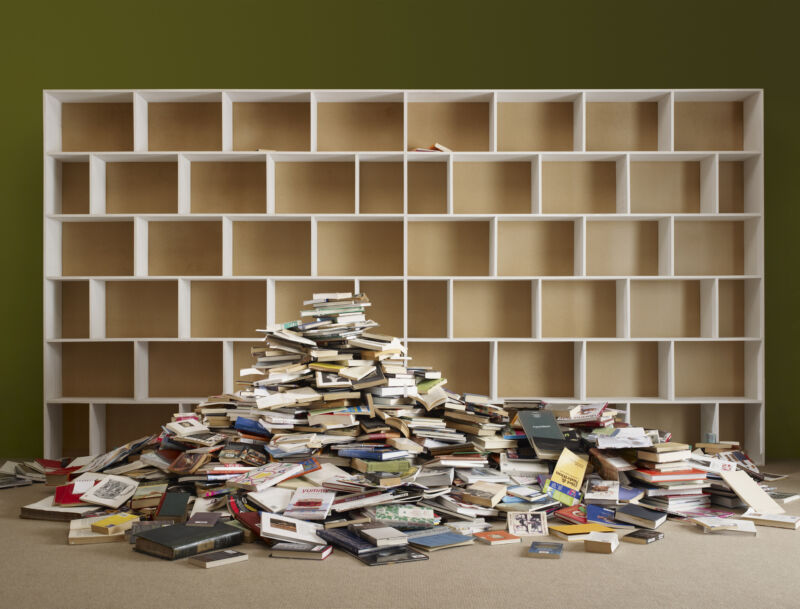
Enlarge (credit: Tim Macpherson | Image Source)
As a result of book publishers successfully suing the Internet Archive (IA) last year, the free online library that strives to keep growing online access to books recently shrank by about 500,000 titles.
IA reported in a blog post this month that publishers abruptly forcing these takedowns triggered a "devastating loss" for readers who depend on IA to access books that are otherwise impossible or difficult to access.
To restore access, IA is now appealing, hoping to reverse the prior court's decision by convincing the US Court of Appeals in the Second Circuit that IA's controlled digital lending of its physical books should be considered fair use under copyright law. An April court filing shows that IA intends to argue that the publishers have no evidence that the e-book market has been harmed by the open library's lending, and copyright law is better served by allowing IA's lending than by preventing it.
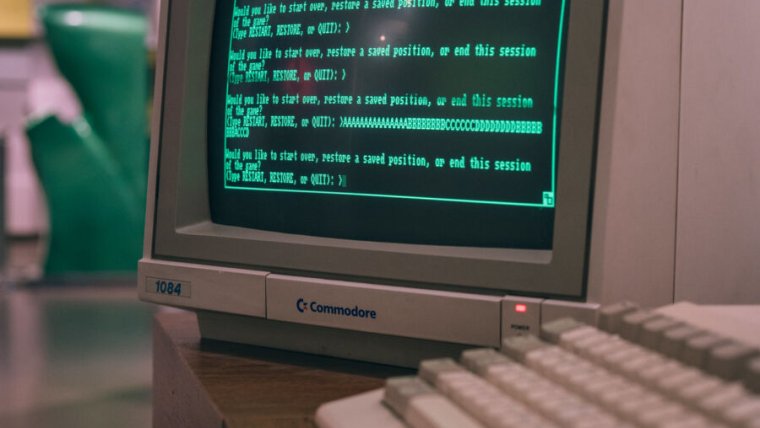
Enlarge / Zork running on an Amiga at the Computerspielemuseum in Berlin, Germany. (credit: Marcin Wichary (CC by 2.0 Deed))
You are standing at the end of a road before a small brick building.
That simple sentence first appeared on a PDP-10 mainframe in the 1970s, and the words marked the beginning of what we now know as interactive fiction.
From the bare-bones text adventures of the 1980s to the heartfelt hypertext works of Twine creators, interactive fiction is an art form that continues to inspire a loyal audience. The community for interactive fiction, or IF, attracts readers and players alongside developers and creators. It champions an open source ethos and a punk-like individuality.

Enlarge (credit: Aurich Lawson)
As the Intel Mac era has wound down over the last couple of years, we've been painstakingly tracking the amount of software support that each outgoing model is getting. We did this to establish, with over 20 years' worth of hard data, whether Intel Mac owners were getting short shrift as Apple shifted its focus to Apple Silicon hardware and to software that leveraged Apple Silicon-exclusive capabilities.
So far, we've found that owners of Intel Macs made in the mid-to-late 2010s are definitely getting fewer major macOS updates and fewer years' worth of security updates than owners of Intel Macs made in the late 2000s and early 2010s but that these systems are still getting more generous support than old PowerPC Macs did after Apple switched to Intel's processors.
The good news with the macOS 15 Sequoia release is that Apple is dropping very few Intel Mac models this year, a much-needed pause that slows the steady acceleration of support-dropping we've seen over the last few macOS releases.

Ubuntu 23.10, codenamed “Mantic Minotaur,” was released on October 12, 2023, nearly nine months ago. Since it is an interim release, its support period is now approaching with the end of life scheduled on July 11, 2024. After this date, Ubuntu 23.10 will no longer receive software and security updates from Canonical. As a result, […]
The post Ubuntu 23.10 Reaches End of Life on July 11, 2024 appeared first on TuxCare.
The post Ubuntu 23.10 Reaches End of Life on July 11, 2024 appeared first on Security Boulevard.


Enlarge / The introduction of model year 2025 brings a retractable hard-top option for the McLaren Artura, plus a host of other upgrades. (credit: McLaren)
MONACO—The idea of an "entry-level" supercar might sound like a contradiction in terms, but every car company's range has to start somewhere, and in McLaren's case, that's the Artura. When Ars first tested this mid-engined plug-in hybrid in 2022, It was only available as a coupe. But for those who prefer things al fresco, the British automaker has now given you that option with the addition of the Artura Spider.
The Artura represented a step forward for McLaren. There's a brand-new carbon fiber chassis tub, an advanced electronic architecture (with a handful of domain controllers that replace the dozens of individual ECUs you might find in some of its other models), and a highly capable hybrid powertrain that combines a twin-turbo V6 gasoline engine with an axial flux electric motor.
For model year 2025 and the launch of the $273,800 Spider version, the engineering team at McLaren have given it a spruce-up, despite only being a couple of years old. Overall power output has increased by 19 hp (14 kW) thanks to new engine maps for the V6, which now has a bit more surge from 4,000 rpm all the way to the 8,500 rpm redline. Our test car was fitted with the new sports exhaust, which isn't obnoxiously loud. It makes some interesting noises as you lift the throttle in the middle of the rev range, but like most turbo engines, it's not particularly mellifluous.






As some Ars readers may recall, I reviewed The Maven Cargo e-bike earlier this year as a complete newb to e-bikes. For my second foray into the world of e-bikes, I took an entirely different path.
The stylish Maven was designed with utility in mind—it's safe, user-friendly, and practical for accomplishing all the daily transportation needs of a busy family. The second bike, the $4,299 Mod Easy Sidecar 3, is on the other end of the spectrum. Just a cursory glance makes it clear: This bike is built for pure, head-turning fun.
The Mod Easy 3 is a retro-style Class 2 bike—complete with a sidecar that looks like it's straight out of Indiana Jones and the Last Crusade. Nailing this look wasn't the initial goal of Mod Bike founder Dor Korngold. In an interview with Ars, Korngold said the Mod Easy was the first bike he designed for himself. "It started with me wanting to have this classic cruiser," he said, but he didn't have a sketch or final design in mind at the outset. Instead, the design was based on what parts he had in his garage.

Enlarge (credit: TopMicrobialStock, Getty Images)
When Ina Chung, a Colorado mother, first fed packaged foods to her infant, she was careful to read the labels. Her daughter was allergic to peanuts, dairy, and eggs, so products containing those ingredients were out. So were foods with labels that said they may contain the allergens.
Chung felt like this last category suggested a clear risk that wasn’t worth taking. “I had heard that the ingredient labels were regulated. And so I thought that that included those statements,” said Chung. “Which was not true.”
Precautionary allergen labels like those that say "processed in a facility that uses milk" or "may contain fish" are meant to address the potential for cross-contact. For instance, a granola bar that doesn’t list peanuts as an ingredient could still say they may be included. And in the United States, these warnings are not regulated; companies can use whatever precautionary phrasing they choose on any product. Some don’t bother with any labels, even in facilities where unintended allergens slip in; others list allergens that may pose little risk. Robert Earl, vice president of regulatory affairs at Food Allergy Research & Education, or FARE, a nonprofit advocacy, research, and education group, has even seen such labels that include all nine common food allergens. “I would bet my bottom dollar not all of those allergens are even in the facility,” he said.

Enlarge / A logo on equipment stored near the OceanGate Inc. offices in Everett, Washington, US, on Thursday, June 22, 2023. (credit: Bloomberg via Getty Images)
The Ocean Sciences Building at the University of Washington in Seattle is a brightly modern, four-story structure, with large glass windows reflecting the bay across the street.
On the afternoon of July 7, 2016, it was being slowly locked down.
Red lights began flashing at the entrances as students and faculty filed out under overcast skies. Eventually, just a handful of people remained inside, preparing to unleash one of the most destructive forces in the natural world: the crushing weight of about 2½ miles of ocean water.
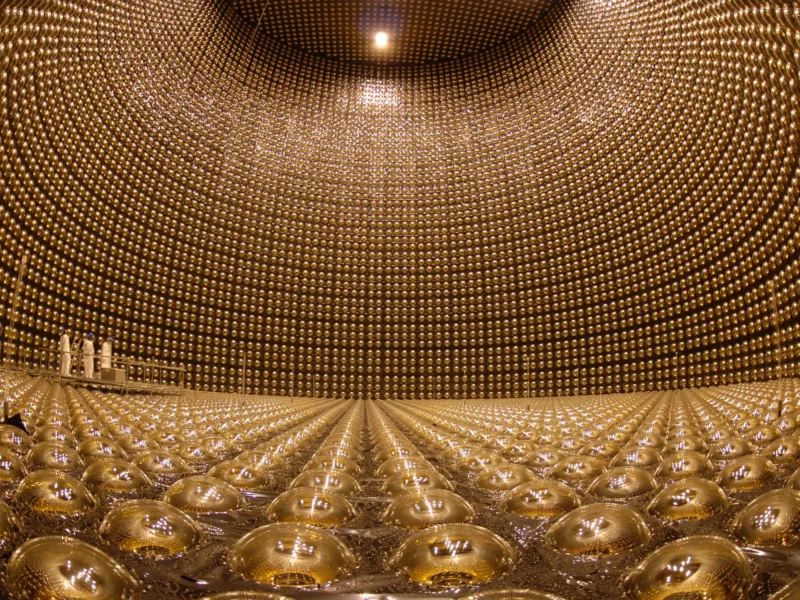
Enlarge / The Super-Kamiokande neutrino detector at the Kamioka Observatory in Japan. (credit: Kamioka Observatory, ICRR (Institute for Cosmic Ray Research), the University of Tokyo )
Somehow, neutrinos went from just another random particle to becoming tiny monsters that require multi-billion-dollar facilities to understand. And there’s just enough mystery surrounding them that we feel compelled to build those facilities since neutrinos might just tear apart the entire particle physics community at the seams.
It started out innocently enough. Nobody asked for or predicted the existence of neutrinos, but there they were in our early particle experiments. Occasionally, heavy atomic nuclei spontaneously—and for no good reason—transform themselves, with either a neutron converting into a proton or vice-versa. As a result of this process, known as beta decay, the nucleus also emits an electron or its antimatter partner, the positron.
There was just one small problem: Nothing added up. The electrons never came out of the nucleus with the same energy; it was a little different every time. Some physicists argued that our conceptions of the conservation of energy only held on average, but that didn’t feel so good to say out loud, so others argued that perhaps there was another, hidden particle participating in the transformations. Something, they argued, had to sap energy away from the electron in a random way to explain this.

Enlarge / NASA's James Webb Space Telescope reveals the Rho Ophiuchi cloud complex, the closest star-forming region to Earth.
In a feat of galactic archeology, astronomers are using ever more detailed information to trace the origin of our galaxy—and to learn about how other galaxies formed in the early stages of the Universe. Using powerful space telescopes like Gaia and James Webb, astronomers are able to peer back in time and look at some of the oldest stars and galaxies. Between Gaia’s data on the position and movements of stars within our Milky Way and Webb’s observations of early galaxies that formed when the Universe was still young, astronomers are learning how galaxies come together and have made surprising discoveries that suggest the early Universe was busier and brighter than anyone previously imagined.
In a recent paper, researchers using the Gaia space telescope identified two streams of stars, named Shakti and Shiva, each of which contains a total mass of around 10 million Suns and which are thought to have merged into the Milky Way around 12 billion years ago.
These streams were present even before the Milky Way had features like a disk or its spiral arms, and researchers think they could be some of the earliest building blocks of the galaxy as it developed.




Enlarge / What can I say? It was tough putting the Brompton C Line Electric through its paces. Finding just the right context for it. Grueling work. (credit: Kevin Purdy)
There’s never been a better time to ride a weird bike.
That's especially true if you live in a city where you can regularly see kids being dropped off at schools from cargo bikes with buckets, child seats, and full rain covers. Further out from the urban core, fat-tire e-bikes share space on trails with three-wheelers, retro-style cruisers, and slick roadies. And folding bikes, once an obscurity, are showing up in more places, especially as they’ve gone electric.
So when I got to try out the Brompton Electric C Line (in a six-speed model), I felt far less intimidated riding, folding, and stashing the little guy wherever I went than I might have been a few years back. A few folks recognized the distinctively small and British bike and offered a thumbs-up or light curiosity. If anyone was concerned about the oddity of this quirky ride, it was me, mostly because I obsessed over whether I could and should lock it up outside or not.

Enlarge (credit: Aurich Lawson | Getty Images)
We’ve been living through the generative AI boom for nearly a year and a half now, following the late 2022 release of OpenAI’s ChatGPT. But despite transformative effects on companies’ share prices, generative AI tools powered by large language models (LLMs) still have major drawbacks that have kept them from being as useful as many would like them to be. Retrieval augmented generation, or RAG, aims to fix some of those drawbacks.
Perhaps the most prominent drawback of LLMs is their tendency toward confabulation (also called “hallucination”), which is a statistical gap-filling phenomenon AI language models produce when they are tasked with reproducing knowledge that wasn’t present in the training data. They generate plausible-sounding text that can veer toward accuracy when the training data is solid but otherwise may just be completely made up.
Relying on confabulating AI models gets people and companies in trouble, as we’ve covered in the past. In 2023, we saw two instances of lawyers citing legal cases, confabulated by AI, that didn’t exist. We’ve covered claims against OpenAI in which ChatGPT confabulated and accused innocent people of doing terrible things. In February, we wrote about Air Canada’s customer service chatbot inventing a refund policy, and in March, a New York City chatbot was caught confabulating city regulations.